Use an Azure Resource Manager template to deploy and connect an Azure virtual machine to Azure Arc
This article provides guidance for using an Azure Resource Manager template (ARM template) to automatically onboard an Azure virtual machine (Azure VM) running Windows to Azure Arc. The provided ARM template is responsible for creating the Azure resources and executing the Azure Arc onboard script on the VM.
Azure VMs are using the Azure Instance Metadata Service (IMDS) by default. By projecting an Azure VM as an Azure Arc-enabled server, a conflict is created, which will not allow for the Azure Arc server resources to be represented as one when the IMDS is being used. Instead, the Azure Arc server will still "act" as a native Azure VM.
This guide will allow you to use and onboard Azure VMs to Azure Arc for demo purposes only. You will have the ability to simulate a server deployed outside of Azure, for example, on-premises or in other cloud platforms.
Note
An Azure VM is not expected to be an Azure Arc-enabled server. The following scenario is unsupported and should only be used for demo and testing purposes.
Prerequisites
Clone the Azure Arc Jumpstart repository.
git clone https://github.com/microsoft/azure_arc.gitInstall or update Azure CLI to version 2.7 and above. Use the following command to check your current installed version.
az --versionAzure subscription: if you don't have an Azure subscription, you can create a free Azure account.
Create an Azure service principal.
In order for you to deploy the Azure resources using the ARM template, an Azure service principal assigned with the Contributor role is required. To create it, sign in to your Azure account and run the following command. You can also run this command in Azure Cloud Shell.
az login az account set -s <Your Subscription ID> az ad sp create-for-rbac -n "<Unique SP Name>" --role contributor --scopes "/subscriptions/<Your Subscription ID>"For example:
az ad sp create-for-rbac -n "http://AzureArcServers" --role contributor --scopes "/subscriptions/00000000-0000-0000-0000-000000000000"The output should look like this:
{ "appId": "XXXXXXXXXXXXXXXXXXXXXXXXXXXX", "displayName": "http://AzureArcServers", "password": "XXXXXXXXXXXXXXXXXXXXXXXXXXXX", "tenant": "XXXXXXXXXXXXXXXXXXXXXXXXXXXX" }Note
We highly recommend that you scope the service principal to a specific Azure subscription and resource group.
Automation flow
For you to get familiar with the automation and deployment flow, below is an explanation.
A user edits the ARM template parameters file (a one-time edit). These parameter values are being used throughout the deployment.
The ARM template includes an Azure VM custom script extension, which deploys the
install_arc_agent.ps1PowerShell script.In order to allow the Azure VM to successfully be projected as an Azure Arc-enabled server, the script will:
Set local OS environment variables.
Generate a local OS sign-in script named
LogonScript.ps1. This script will:Create the
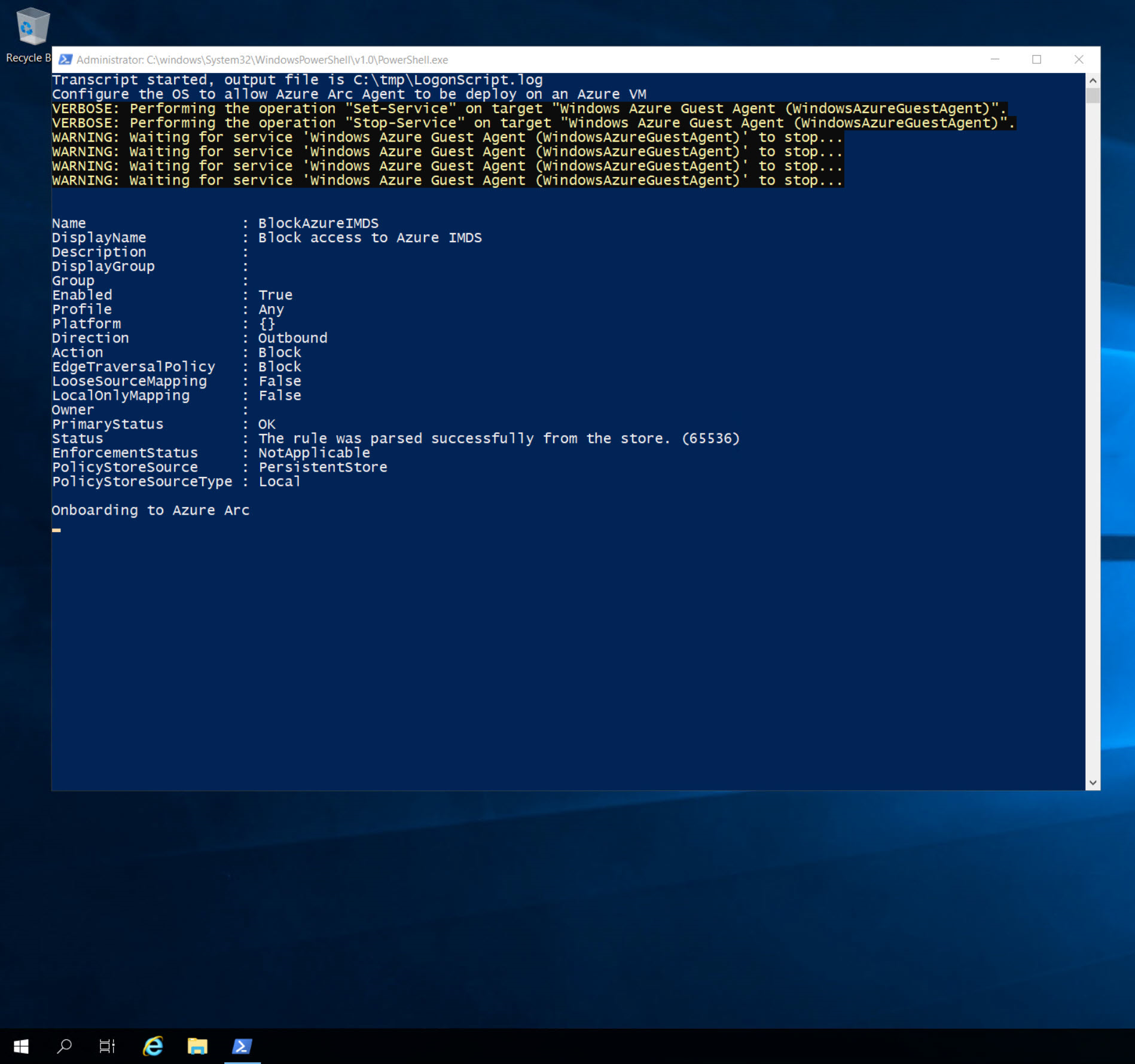
LogonScript.logfile.Stop and disable the Windows Azure guest agent service.
Create a new Windows Firewall rule to block Azure IMDS outbound traffic to the
169.254.169.254remote address.Unregister the sign-in script Windows scheduled task so it won't run after first sign-in.
Disable and prevent Windows Server Manager from running on startup.
A user connects via RDP to the Windows VM, which starts running
LogonScript.ps1and onboards the VM to Azure Arc.
Deployment
As mentioned, this deployment will use ARM templates. You will deploy a single template, responsible for creating all the Azure resources in a single resource group and onboarding the created VM to Azure Arc.
Before deploying the ARM template, sign in to Azure using Azure CLI with the
az logincommand.The deployment is using the ARM template parameters file. Before initiating the deployment, edit the
azuredeploy.parameters.jsonfile located in your local cloned repository folder. An example parameters file is located here.To deploy the ARM template, navigate to the local cloned deployment folder and run the following command:
az group create --name <Name of the Azure resource group> --location <Azure Region> --tags "Project=jumpstart_azure_arc_servers" az deployment group create \ --resource-group <Name of the Azure resource group> \ --name <The name of this deployment> \ --template-uri https://raw.githubusercontent.com/microsoft/azure-arc/main/azure_arc_servers_jumpstart/azure/windows/arm_template/azuredeploy.json \ --parameters <The `azuredeploy.parameters.json` parameters file location>Note
Make sure that you are using the same Azure resource group name as the one you used in the
azuredeploy.parameters.jsonfile.For example:
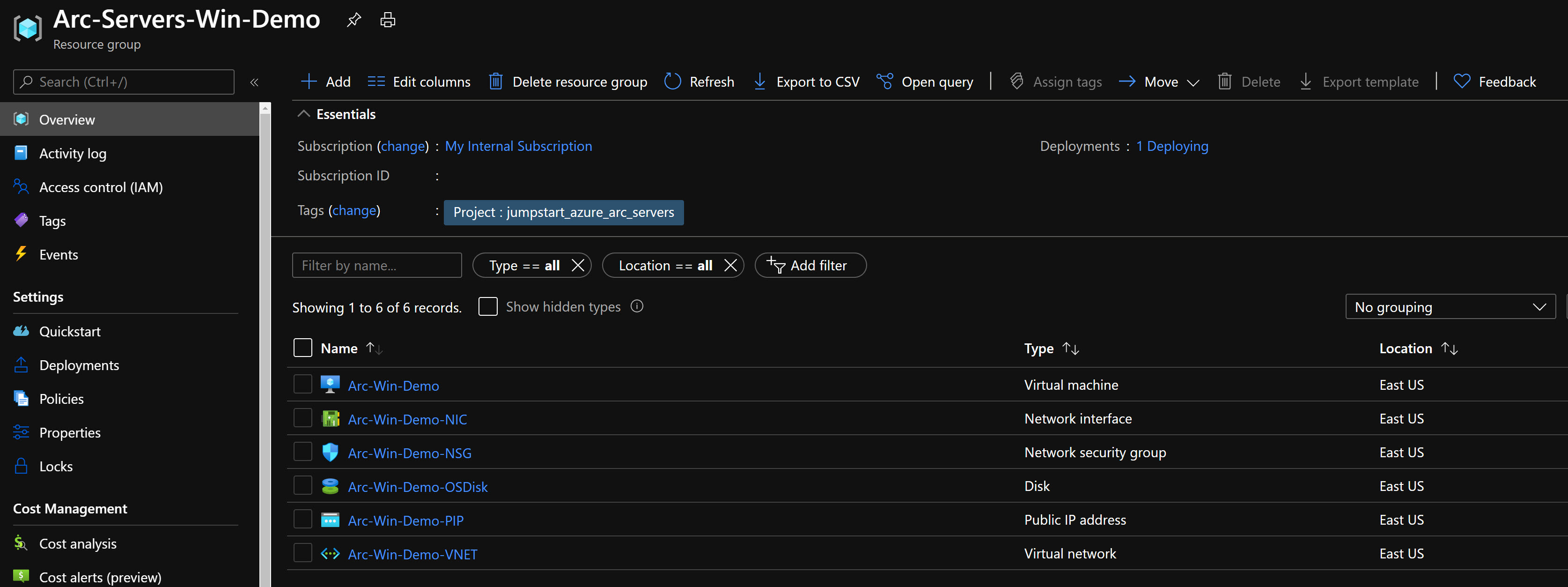
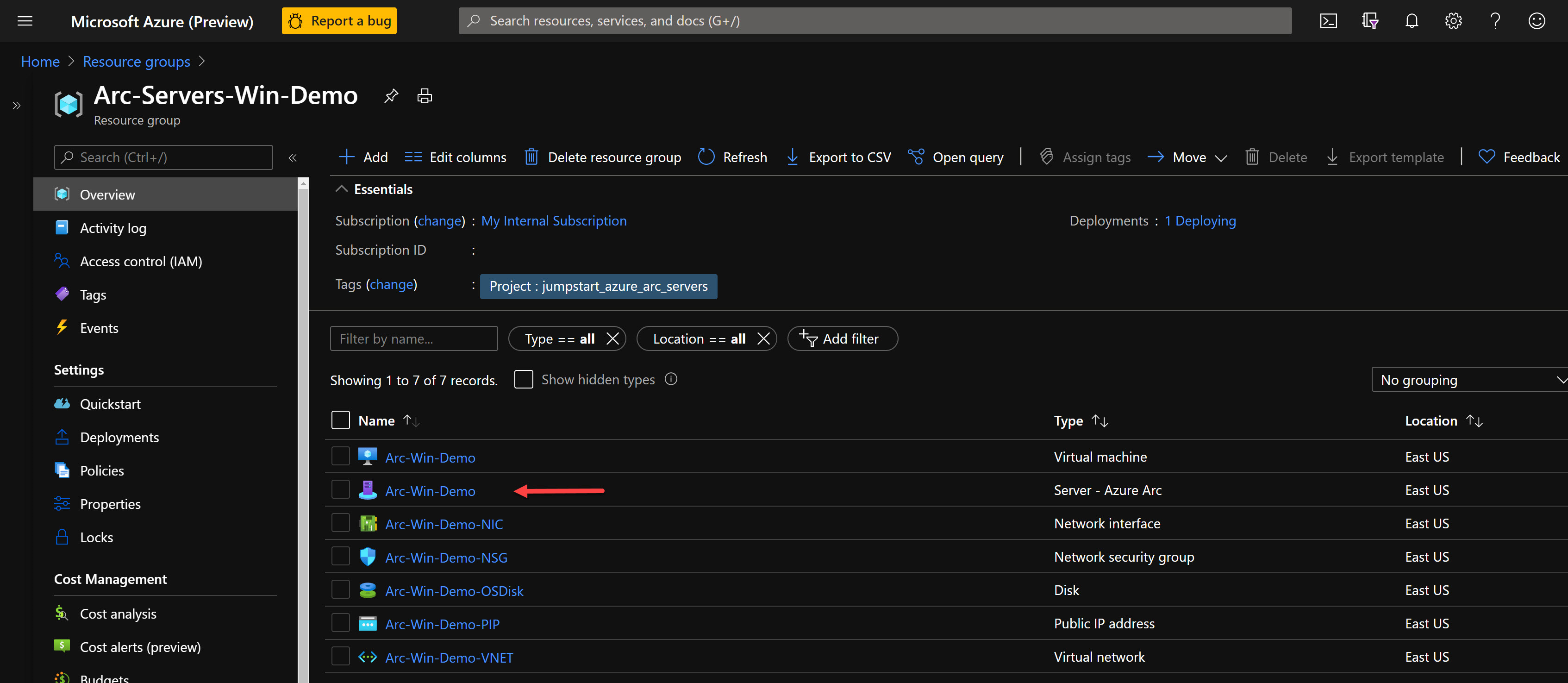
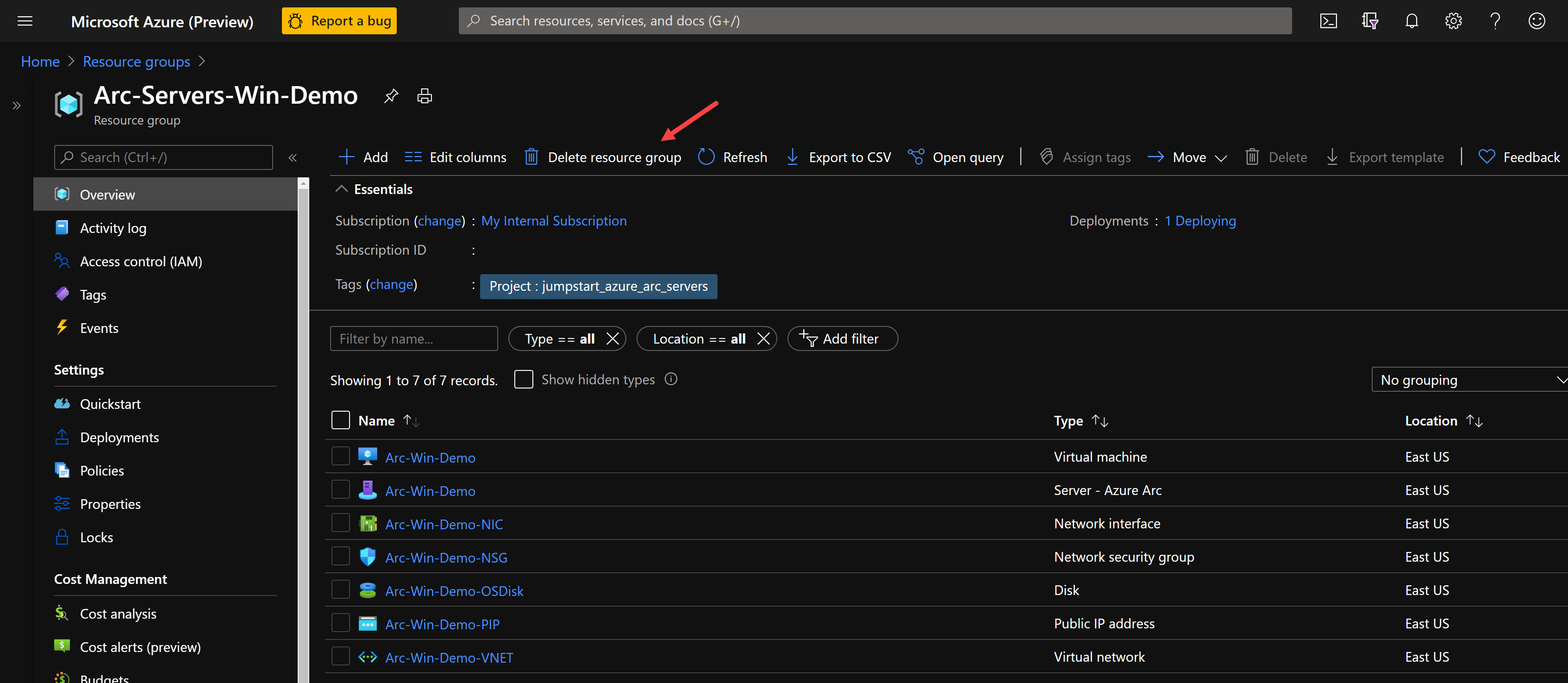
az group create --name Arc-Servers-Win-Demo --location "East US" --tags "Project=jumpstart_azure_arc_servers" az deployment group create \ --resource-group Arc-Servers-Win-Demo \ --name arcwinsrvdemo \ --template-uri https://raw.githubusercontent.com/microsoft/azure-arc/main/azure_arc_servers_jumpstart/azure/windows/arm_template/azuredeploy.json \ --parameters azuredeploy.parameters.jsonOnce the Azure resources have been provisioned, you can see them in the Azure portal.

Windows sign-in and post-deployment
Now that the Windows Server VM is created, the next step is connecting it. Using its public IP address, RDP to the VM.

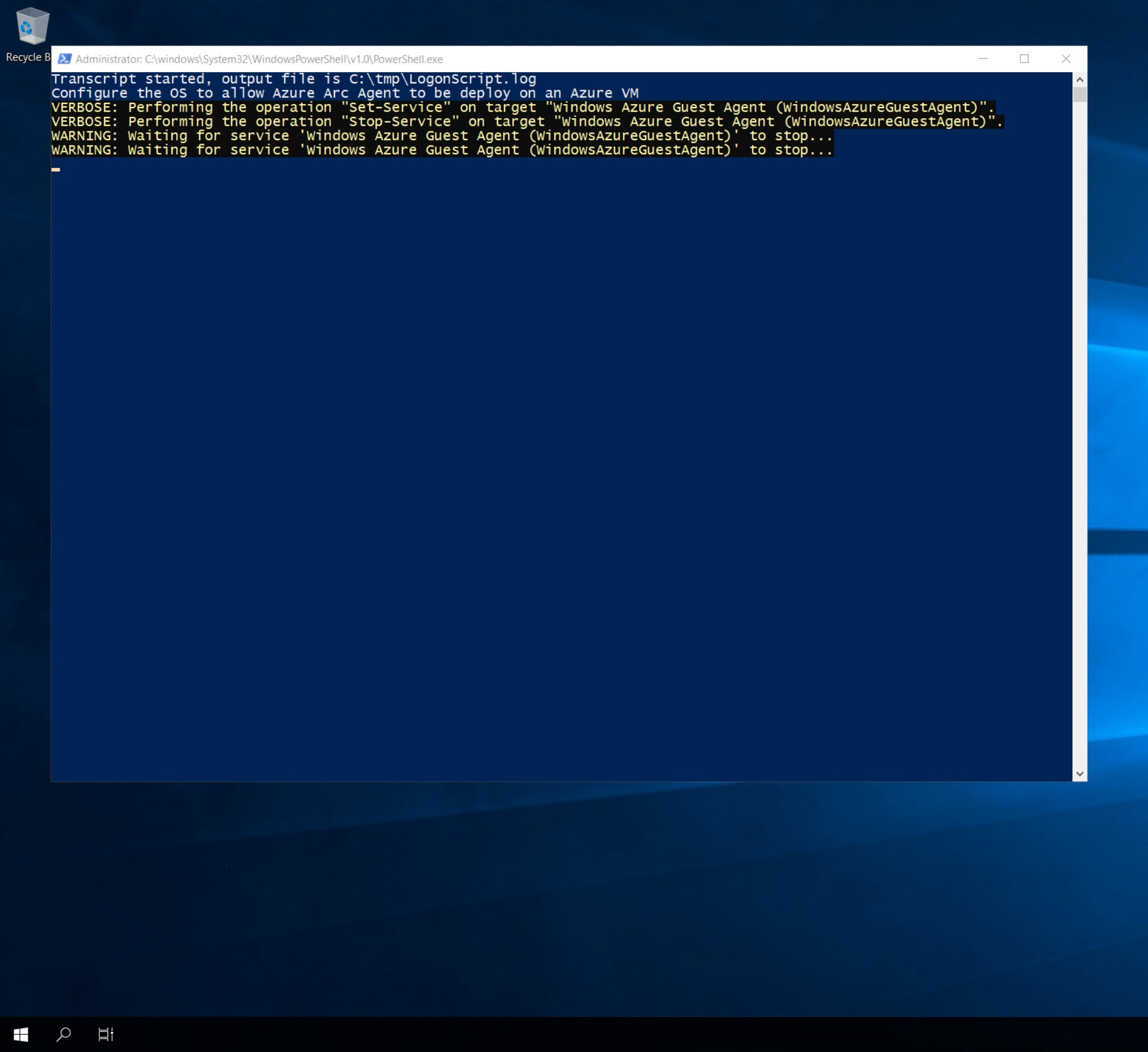
Upon first sign-in, as mentioned in the Automation flow section, a sign-in script will get executed. This script is created as part of the automated deployment process.
Let the script run and do not close the PowerShell session. The session closes for you automatically once completed.
Note
The script run time is ~1-2 minutes long.
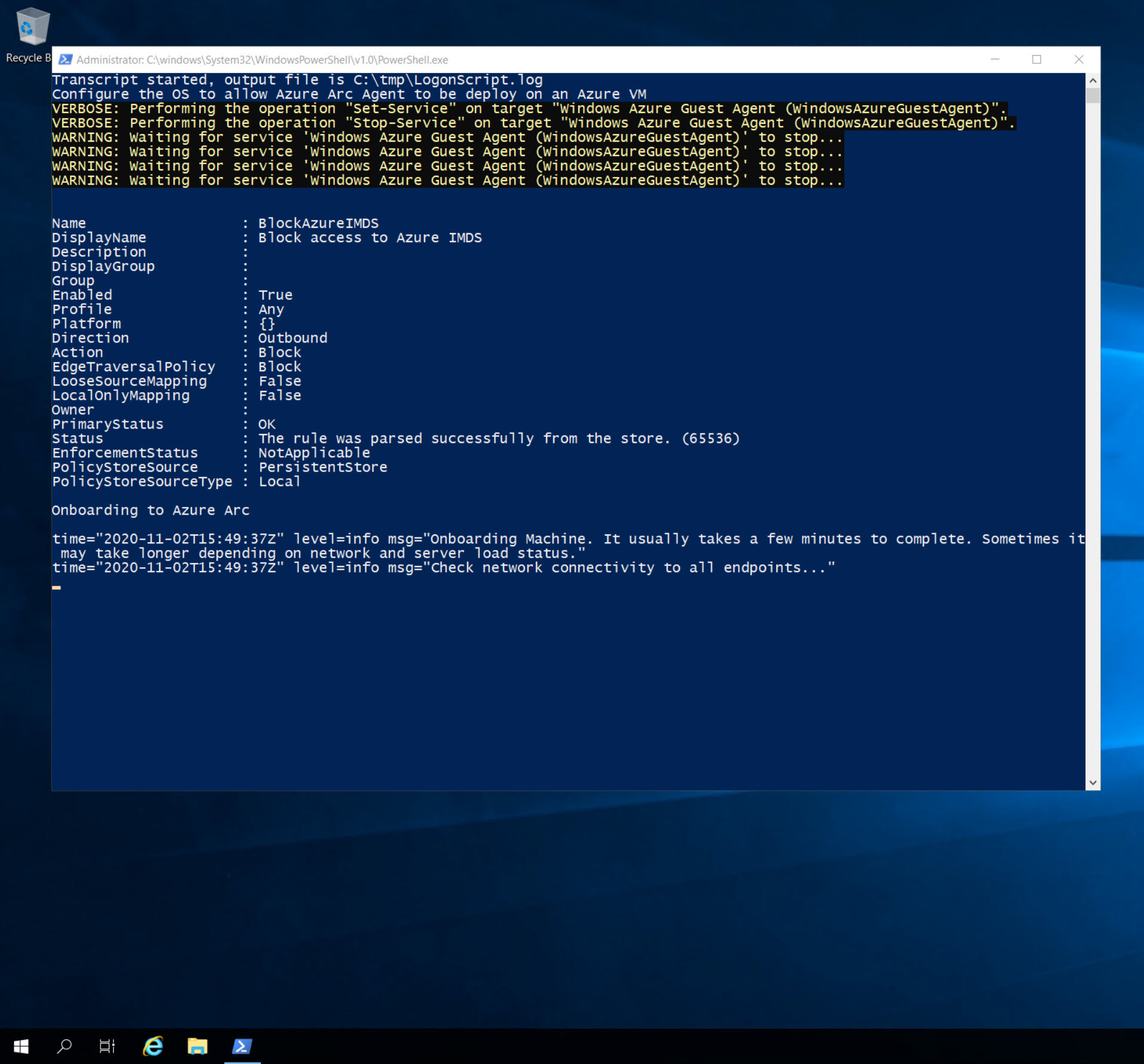
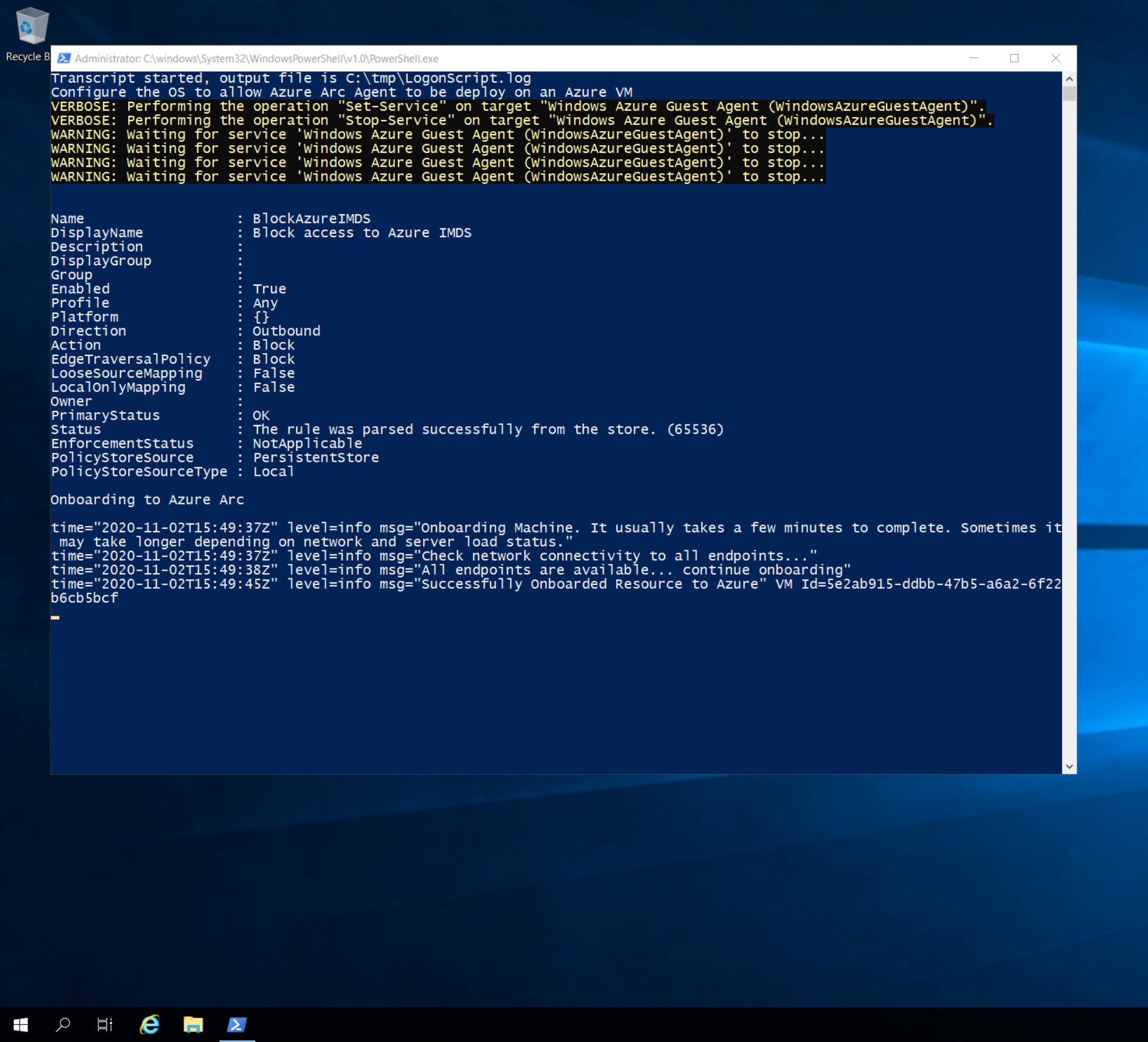
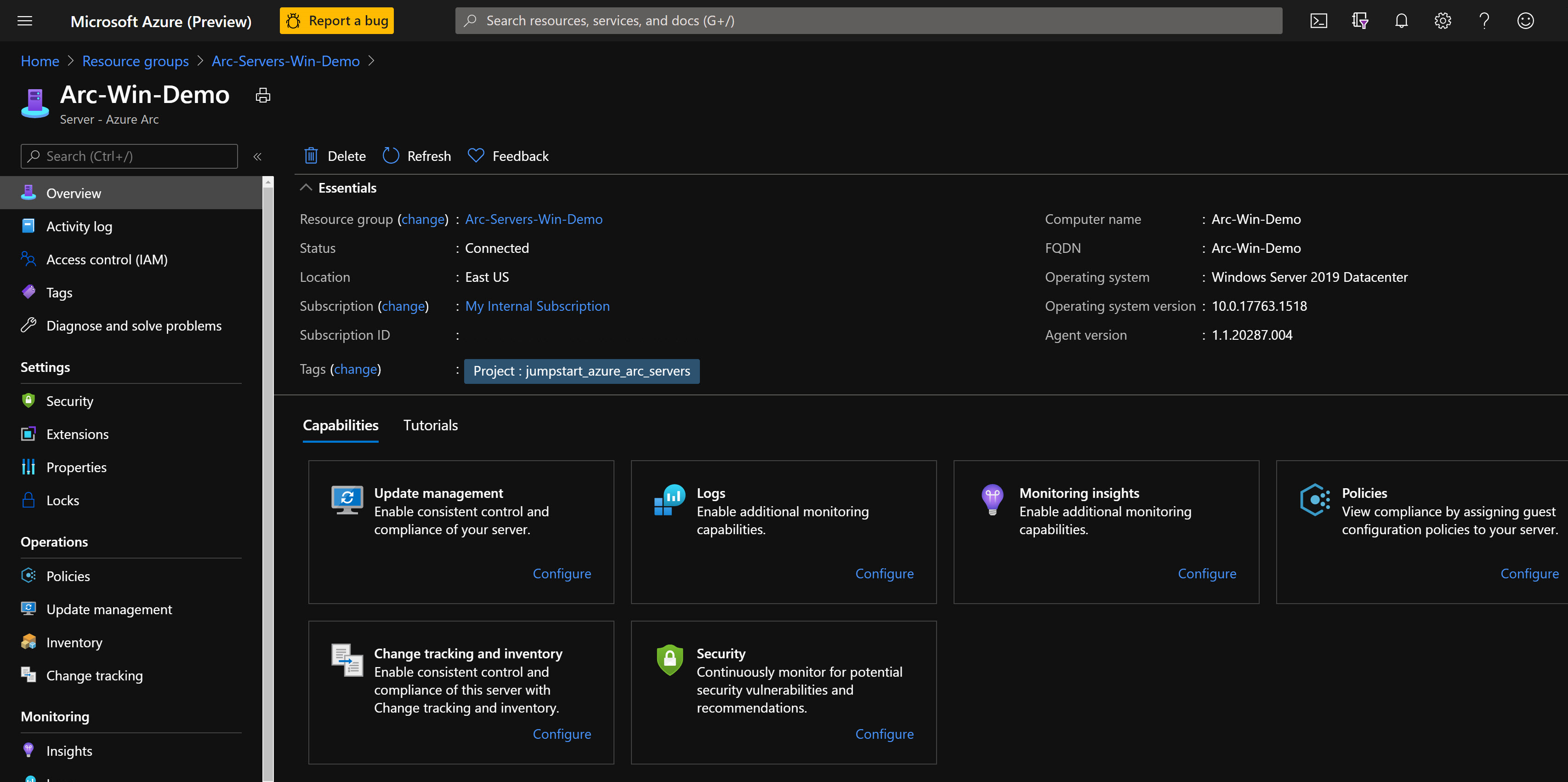
Upon successful completion, a new Azure Arc-enabled server will be added to the resource group.
Cleanup
To delete the entire deployment, delete the resource group from the Azure portal.
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for