What is Microsoft Defender for open-source relational databases
Defender for Cloud detects anomalous activities indicating unusual and potentially harmful attempts to access or exploit databases. The plan makes it simple to address potential threats to databases without the need to be a security expert or manage advanced security monitoring systems.
Availability
Check out the pricing page for pricing information for Microsoft Defender for open-source relational databases.
Defender for open-source relational database is supported on PaaS environments for Azure and AWS and not on Azure Arc-enabled machines.
This plan brings threat protections for the following open-source relational databases on Azure:
Protected versions of Azure Database for PostgreSQL include:
- Single Server - General Purpose and Memory Optimized. Learn more in PostgreSQL Single Server pricing tiers.
- Flexible Server - all pricing tiers.
Protected versions of Azure Database for MySQL include:
- Single Server - General Purpose and Memory Optimized. Learn more in MySQL pricing tiers.
- Flexible Server - all pricing tiers.
Protected versions of Azure Database for MariaDB include:
- General Purpose and Memory Optimized. Learn more in MariaDB pricing tiers.
For RDS instances on AWS (Preview):
- Aurora PostgreSQL
- Aurora MySQL
- PostgreSQL
- MySQL
- MariaDB
View cloud availability for Defender for open-source relational databases
What are the benefits of Microsoft Defender for open-source relational databases?
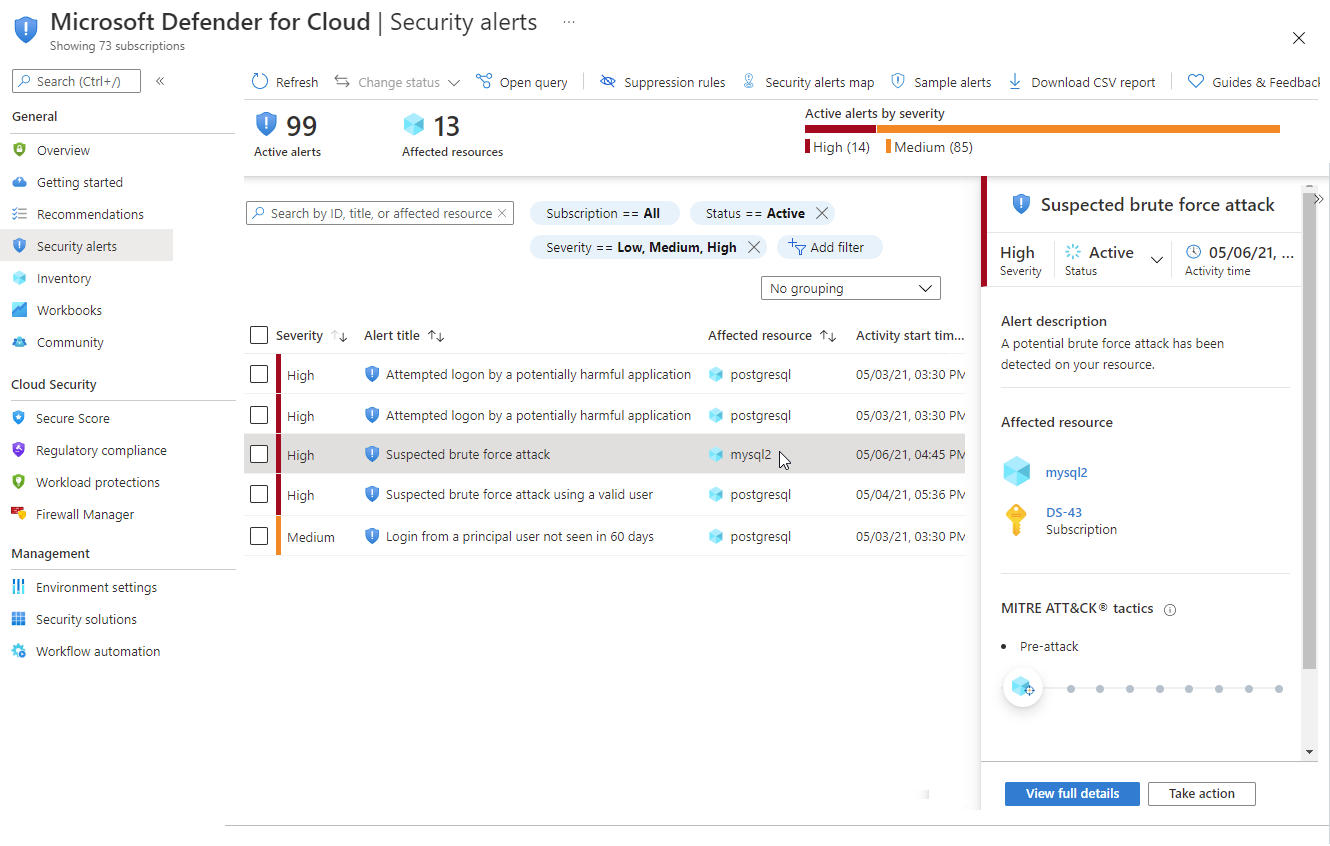
Defender for Cloud provides multicloud alerts on anomalous activities so that you can detect potential threats and respond to them as they occur.
When you enable this plan, Defender for Cloud will provide alerts when it detects anomalous database access and query patterns as well as suspicious database activities.
These alerts appear in Defender for Cloud's multicloud alerts page and include:
- details of the suspicious activity that triggered them
- the associated MITRE ATT&CK tactic
- recommended actions for how to investigate and mitigate the threat
- options for continuing your investigations with Microsoft Sentinel
What kind of alerts does Microsoft Defender for open-source relational databases provide?
Threat intelligence enriched multicloud alerts are triggered when there are:
- Anomalous database access and query patterns - For example, an abnormally high number of failed sign-in attempts with different credentials (a brute force attempt).
- Suspicious database activities - For example, a legitimate user accessing an SQL Server from a breached computer which communicated with a crypto-mining C&C server.
- Brute-force attacks – With the ability to separate simple brute force or a successful brute force.
Tip
View the full list of multicloud alerts for database servers in the alerts reference page.
Related articles
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for