About pipeline security roles
Azure DevOps Services | Azure DevOps Server 2022 - Azure DevOps Server 2019
While the majority of features and functional tasks are managed by individual permissions, there are several artifacts and features that the system manages through role-based permissions. You can add users or groups to a role. Each role determines the set of operations that the user can perform as described in the following sections.
Many role-based permissions can be set for all artifacts of a specific type in a project, or for the project or collection and then selectively inherited for a specific artifact. Role memberships for individual items automatically inherit those set for the project or collection. If required, you can turn off Inheritance for a specific artifact.
Default role assignments
By default, all contributors in a project are members of the User role on each hosted queue. This allows every contributor in a project to author and run build and release pipelines using hosted queues.
Agent pool security roles, project-level
You add users to the following security roles from the project-level admin context, Agent Pools page. For information on adding and managing agent pools, see Agent pools.
| Role (project-level) | Description |
|---|---|
| Reader | Can view the pool. You typically add operators to this role that are responsible for monitoring the build and deployment jobs in that pool. |
| User | Can view and use the pool when authoring build or release pipelines. |
| Creator | Can create and use the pool when authoring build or release pipelines. |
| Administrator | Can manage membership for all roles of the pool, as well as view and use the pools. The user that created a pool is automatically added to the Administrator role for that pool. |
You control the security of all project agent pools from the Security tab. Role memberships for individual project agent pools automatically inherit from what those roles. By default, the following groups are added to the Administrator role of 'All agent pools': Build Administrators, Release Administrators, Project Administrators.
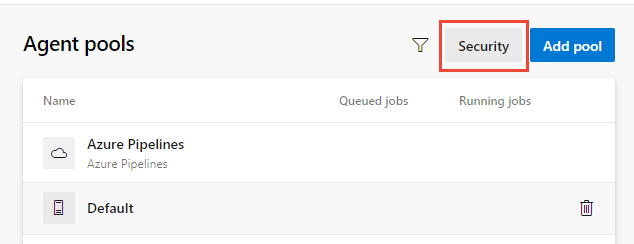
To manage role settings for a project agent pool, open Project settings and choose Agent Pools.
To set permissions for all pools within the project, choose Security, and then add a user and select their role.
To set permissions for a specific pool, choose the pool and then Security. Under Pipeline permissions, you can see which pipelines have access to the pool. You can explicitly allow a pipeline by using the
+button or allow all pipelines by using the⋮button. Under User permissions, you can add a user or group and select their role.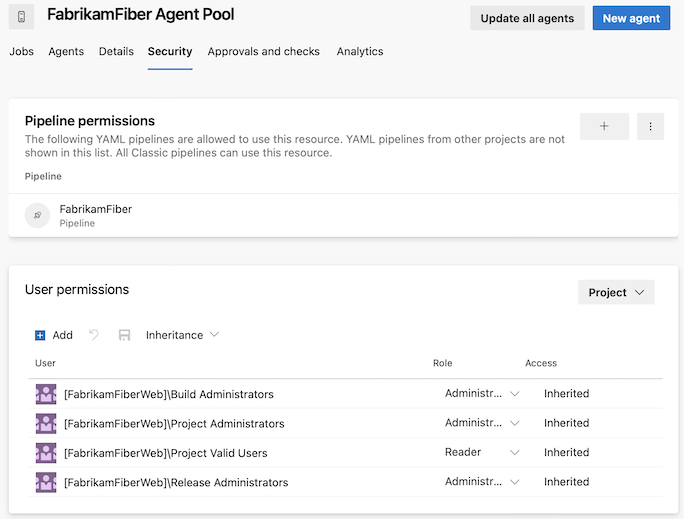
Agent pool security roles, organization or collection-level
You add users to the following security roles from the Organization settings or collection-level admin settings, Agent Pools page. For information on adding and managing agent pools, see Agent pools.
| Role (organization-level) | Description |
|---|---|
| Reader | Can view the pool as well as agents. You typically add operators to this role that are responsible for monitoring the agents and their health. |
| Service Account | Can use the pool to create an agent in a project. If you follow the guidelines for creating new pools, you typically do not have to add any members to this role. |
| Administrator | Can register or unregister agents from the pool and manage membership for all pools, as well as view and create pools. They can also use the agent pool when creating an agent in a project. The system automatically adds the user that created the pool to the Administrator role for that pool. |
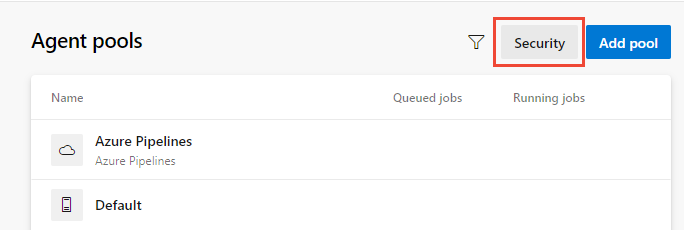
To manage role settings for an organization or collection-level agent pools, open Organization settings and choose Agent Pools.
To set permissions for all pools within the organization or collection, choose Security, and then add a user or group and select their role.
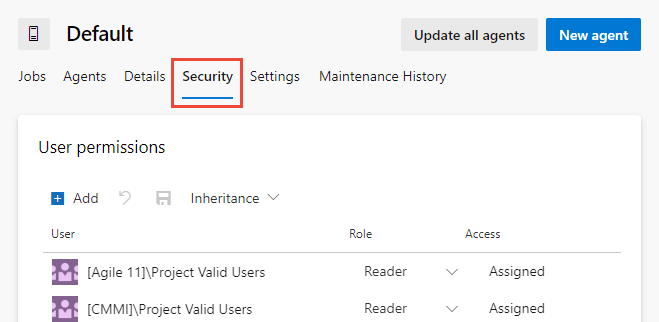
To set permissions for a specific pool, choose the pool and then Security. Then add a user or group and select their role.
Deployment group security roles
You add users to the following roles from Pipelines or Build and Release. For information on adding and managing deployment groups, see Deployment groups.
| Role | Description |
|---|---|
| Reader | Can only view deployment groups. |
| Creator | Can view and create deployment groups. |
| User | Can view and use but cannot manage or create deployment groups. |
| Administrator | Can administer roles, manage, view and use deployment groups. |
Deployment pool security roles
You add users to the following roles from the collection-level admin context, Deployment Pools page. To create and manage deployment pools, see Deployment groups.
| Role | Description |
|---|---|
| Reader | Can only view deployment pools. |
| Service Account | Can view agents, create sessions, and listen for jobs from the agent pool. |
| User | Can view and use the deployment pool for creating deployment groups. |
| Administrator | Can administer, manage, view and use deployment pools. |
Library asset security roles: Variable groups and secure files
You add users to a library role from Pipelines or Build and Release. To learn more about using these library assets, see Variable groups and Secure files
| Role | Description |
|---|---|
| Administrator | Can edit/delete and manage security for library items. |
| Creator | Can create library items. |
| Reader | Can only read library items. |
| User | Can consume library items in pipelines. |
Service connection security roles
You add users to the following roles from the project-level admin context, Services page. To create and manage these resources, see Service connections for build and release.
| Role | Description |
|---|---|
| User | Can use the endpoint when authoring build or release pipelines. |
| Administrator | Can manage membership of all other roles for the service connection as well as use the endpoint to author build or release pipelines. The system automatically adds the user that created the service connection to the Administrator role for that pool. |
Related articles
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for