Azure Key Vault backup and restore
This document shows you how to back up secrets, keys, and certificates stored in your key vault. A backup is intended to provide you with an offline copy of all your secrets in the unlikely event that you lose access to your key vault.
Overview
Azure Key Vault automatically provides features to help you maintain availability and prevent data loss. Back up secrets only if you have a critical business justification. Backing up secrets in your key vault may introduce operational challenges such as maintaining multiple sets of logs, permissions, and backups when secrets expire or rotate.
Key Vault maintains availability in disaster scenarios and will automatically fail over requests to a paired region without any intervention from a user. For more information, see Azure Key Vault availability and redundancy.
If you want protection against accidental or malicious deletion of your secrets, configure soft-delete and purge protection features on your key vault. For more information, see Azure Key Vault soft-delete overview.
Limitations
Important
Key Vault does not support the ability to backup more than 500 past versions of a key, secret, or certificate object. Attempting to backup a key, secret, or certificate object may result in an error. It is not possible to delete previous versions of a key, secret, or certificate.
Key Vault doesn't currently provide a way to back up an entire key vault in a single operation and keys, secrets and certitificates must be backup indvidually.
Also consider the following issues:
- Backing up secrets that have multiple versions might cause time-out errors.
- A backup creates a point-in-time snapshot. Secrets might renew during a backup, causing a mismatch of encryption keys.
- If you exceed key vault service limits for requests per second, your key vault will be throttled, and the backup will fail.
Design considerations
When you back up a key vault object, such as a secret, key, or certificate, the backup operation will download the object as an encrypted blob. This blob can't be decrypted outside of Azure. To get usable data from this blob, you must restore the blob into a key vault within the same Azure subscription and Azure geography.
Prerequisites
To back up a key vault object, you must have:
- Contributor-level or higher permissions on an Azure subscription.
- A primary key vault that contains the secrets you want to back up.
- A secondary key vault where secrets will be restored.
Back up and restore from the Azure portal
Follow the steps in this section to back up and restore objects by using the Azure portal.
Back up
Go to the Azure portal.
Select your key vault.
Go to the object (secret, key, or certificate) you want to back up.
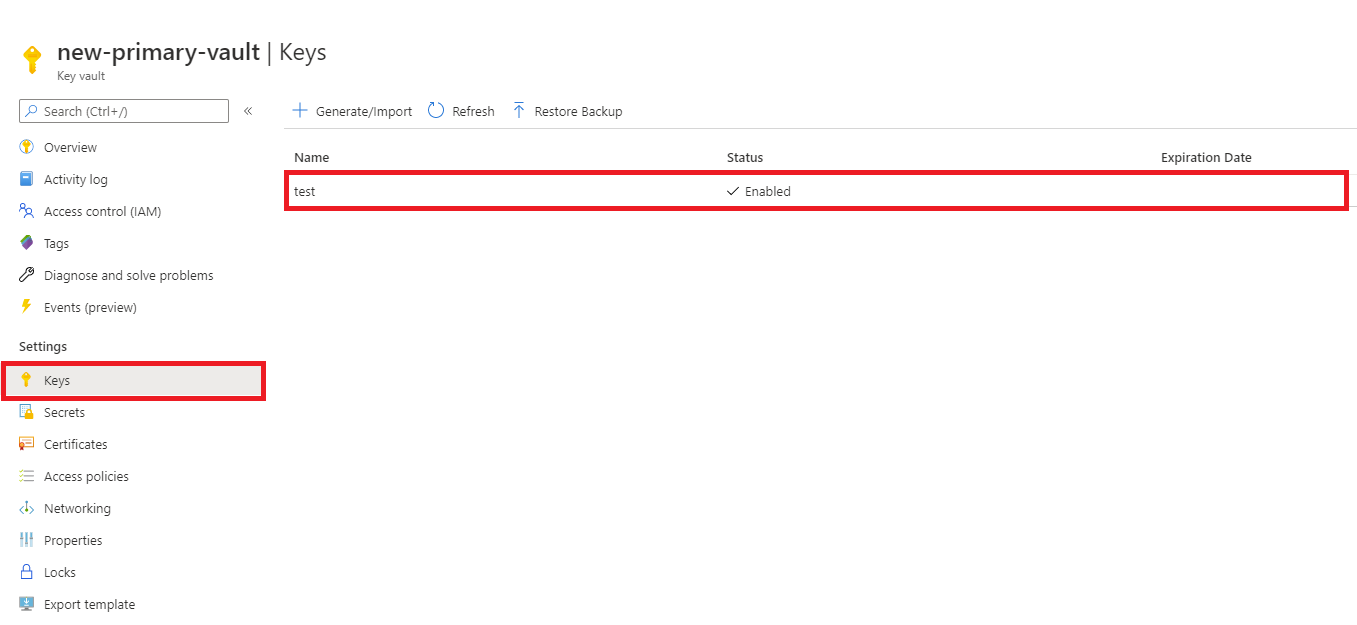
Select the object.
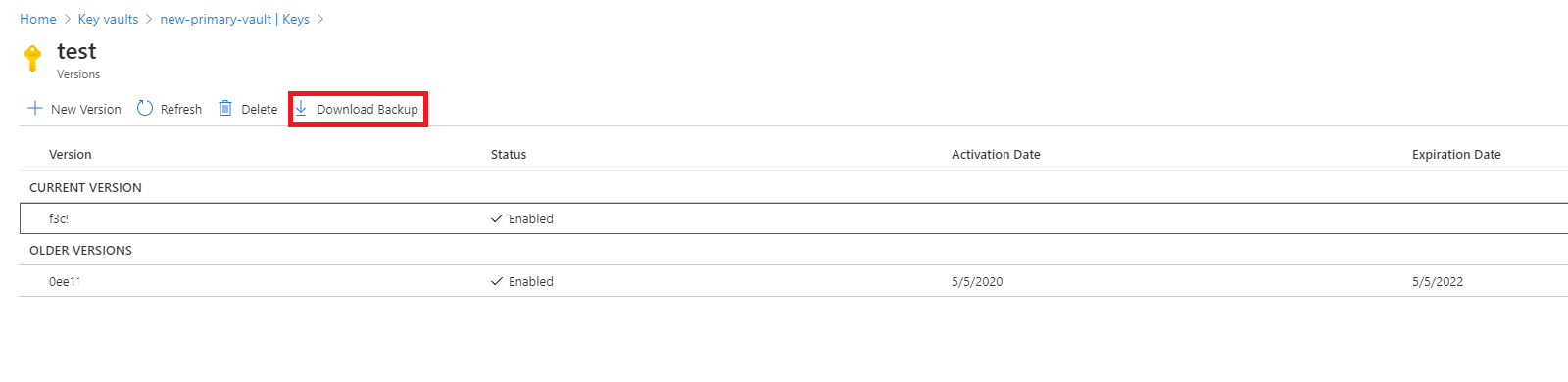
Select Download Backup.
Select Download.
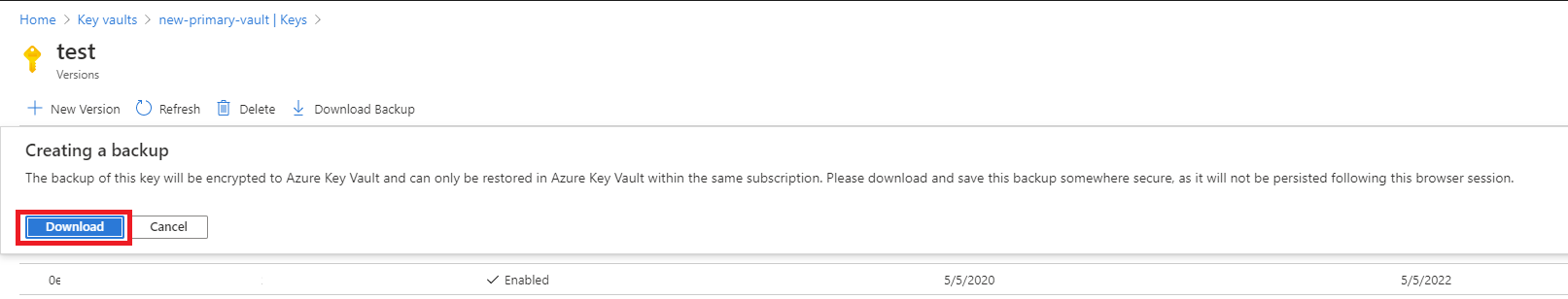
Store the encrypted blob in a secure location.
Restore
Go to the Azure portal.
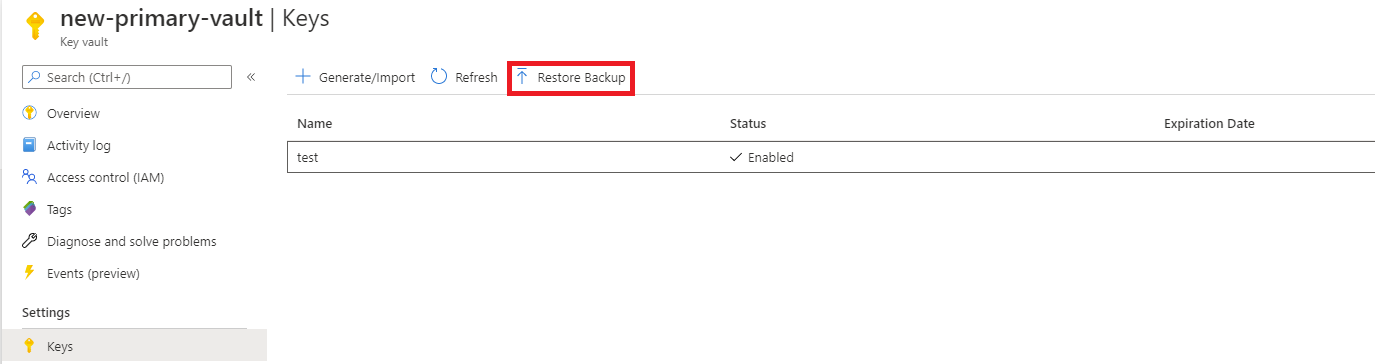
Select your key vault.
Go to the type of object (secret, key, or certificate) you want to restore.
Select Restore Backup.
Go to the location where you stored the encrypted blob.
Select OK.
Back up and restore from the Azure CLI or Azure PowerShell
## Log in to Azure
az login
## Set your subscription
az account set --subscription {AZURE SUBSCRIPTION ID}
## Register Key Vault as a provider
az provider register -n Microsoft.KeyVault
## Back up a certificate in Key Vault
az keyvault certificate backup --file {File Path} --name {Certificate Name} --vault-name {Key Vault Name} --subscription {SUBSCRIPTION ID}
## Back up a key in Key Vault
az keyvault key backup --file {File Path} --name {Key Name} --vault-name {Key Vault Name} --subscription {SUBSCRIPTION ID}
## Back up a secret in Key Vault
az keyvault secret backup --file {File Path} --name {Secret Name} --vault-name {Key Vault Name} --subscription {SUBSCRIPTION ID}
## Restore a certificate in Key Vault
az keyvault certificate restore --file {File Path} --vault-name {Key Vault Name} --subscription {SUBSCRIPTION ID}
## Restore a key in Key Vault
az keyvault key restore --file {File Path} --vault-name {Key Vault Name} --subscription {SUBSCRIPTION ID}
## Restore a secret in Key Vault
az keyvault secret restore --file {File Path} --vault-name {Key Vault Name} --subscription {SUBSCRIPTION ID}
Next steps
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for