Configure the Microsoft Dynamics 365 Server for claims-based authentication
After you have installed AD FS, you need to set the Dynamics 365 Server binding type and root domains before you enable claims-based authentication.
Set Microsoft Dynamics 365 Server binding to HTTPS and configure the root domain web addresses
On the Dynamics 365 Customer Engagement (on-premises) server, start the Deployment Manager.
In the Actions pane, select Properties.
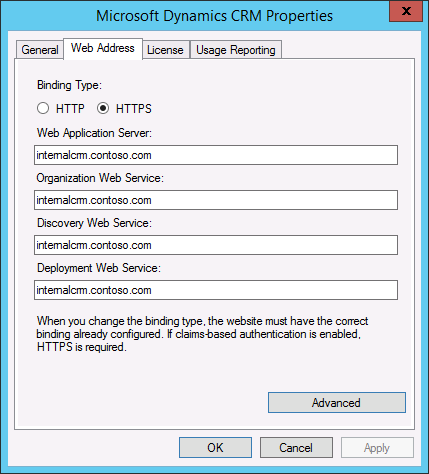
Select the Web Address tab.
Under Binding Type, select HTTPS.
Verify that the web addresses are valid for your TLS/SSL certificate and the TLS/SSL port bound to the Dynamics 365 Customer Engagement (on-premises) website. Because you are configuring Dynamics 365 Server to use claims authentication for internal access, use the host name for the root domain web addresses.
For example, for a *.contoso.com wildcard certificate, you would use internalcrm.contoso.com for the web addresses.
If you install AD FS and Dynamics 365 Server on separate servers, do not specify port 443 for the Web Application Server, Organization Web Service, or Discovery Web Service.
Select OK.
Warning
If Dynamics 365 for Outlook clients were configured using the old binding values, these clients will need to be configured with the new values.
The CRMAppPool account and the Microsoft Dynamics CRM encryption certificate
The certificate you specify in the Configure Claims-Based Authentication Wizard is used by AD FS to encrypt security tokens issued to the Dynamics 365 Server client. The CRMAppPool account of each Dynamics 365 Customer Engagement (on-premises) web application must have read permission to the private key of the encryption certificate.
On the Dynamics 365 Customer Engagement (on-premises) server, create a Microsoft Management Console (MMC) with the Certificates snap-in console that targets the Local computer certificate store.
In the console tree, expand the Certificates (Local Computer) node, expand the Personal store, and then select Certificates.
In the details pane, right-click the encryption certificate specified in the Configure Claims-Based Authentication Wizard, point to All Tasks, and then select Manage Private Keys.
Select Add, (or select the Network Service account if that is the account you used during Setup) add the CRMAppPool account, and then grant Read permissions.
Note
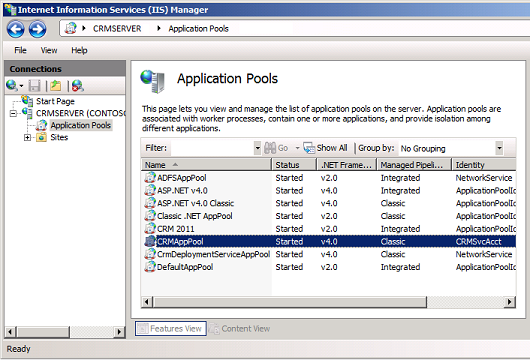
You can use IIS Manager to determine what account was used during setup for the CRMAppPool account. In the Connections pane, select Application Pools, and then check the Identity value for CRMAppPool.
Select OK.
Configuring claims-based authentication using the Configure Claims-Based Authentication Wizard
Run the Configure Claims-Based Authentication Wizard to enable claims authentication on your Dynamics 365 Server.
On the Dynamics 365 Customer Engagement (on-premises) server, start the Deployment Manager.
In the Deployment Manager console tree, right-click Microsoft Dynamics 365, and then select Configure Claims-Based Authentication.
Review the contents of the page, and then select Next.
On the Specify the security token service page, enter the federation metadata URL, such as https://sts1.contoso.com/federationmetadata/2007-06/federationmetadata.xml.
This data is typically located on the website where Active Directory Federation Services is running. To verify the correct URL, open an Internet browser and view the federation metadata URL. Verify that no certificate-related warnings appear.
You may need to turn on Compatibility View in Internet Explorer.
Select Next.
On the Specify the encryption certificate page, specify the encryption certificate in one of two ways:
In the Certificate box, type the complete common name (CN) of the certificate by using the format CN=certificate_subject_name.
Under Certificate, select Select, and then select a certificate.
This certificate is used by AD FS to encrypt authentication security tokens that are issued to the Dynamics 365 Customer Engagement (on-premises) client.
Note
The Dynamics 365 Customer Engagement (on-premises) service account must have Read permissions for the private key of the encryption certificate. For more information, see “The CRMAppPool account and the Dynamics 365 Customer Engagement (on-premises) encryption certificate” above.
Select Next.
The Configure Claims-Based Authentication Wizard verifies the token and certificate that you specified.
On the System Checks page, review the results, perform any steps required to fix problems, and then select Next.
On the Review your selections and then click Apply page, verify your selections, and then select Apply.
Note the URL you must use to add the relying party to the security token service. View and save the log file for later reference.
Select Finish.
Configuring claims-based authentication using Windows PowerShell
On the Dynamics 365 Customer Engagement (on-premises) server, open a Windows PowerShell prompt.
Add the Dynamics 365 Customer Engagement (on-premises)Windows PowerShell snap-in:
PS > Add-PSSnapin Microsoft.Crm.PowerShellGet the claims-based authentication settings:
PS > $claims = Get-CrmSetting -SettingType "ClaimsSettings"Configure the claims-based authentication object:
PS > $claims.Enabled = 1 (or $true) PS > $claims.EncryptionCertificate = certificate_namePS > $claims.FederationMetadataUrl = federation_metadata_URLWhere:
1 = "true".
certificate_nameis the name of the encryption certificate.federation_metadata_URLis the federation metadata URL for the security token service. (For example, https://sts1.contoso.com/federationmetadata/2007-06/federationmetadata.xml.)
Set the claims-based authentication values:
PS > Set-CrmSetting $claims
Set Read permissions for the ADFSAppPool account
If you are installing AD FS on a separate server, verify the account used for the ADFSAppPool application pool has Read permissions. See the preceding topic “The CRMAppPool account and the Dynamics 365 Customer Engagement (on-premises) encryption certificate” for the process steps.
See Also
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for