How to use the Microsoft data classification dashboard
As a Microsoft 365 administrator or compliance administrator, you can evaluate and then tag content in your organization in order to control where it goes, protect it no matter where it is, and ensure that it is preserved and deleted according to your organization's needs. You do this through the application of sensitivity labels, retention labels, and sensitive information type classification. There are various ways to do the discovery, evaluation, and tagging, but the end result is that you may have very large numbers of documents and emails that are tagged and classified with one or both of these labels. After you apply your retention labels and sensitivity labels, you'll want to see how the labels are being used across your tenant and what is being done with those items. The data classification page provides visibility into that body of content, specifically:
- the number items that have been classified as a sensitive information type and what those classifications are
- the top applied sensitivity labels in both Microsoft 365 and Azure Information Protection
- the top applied retention labels
- a summary of activities that users are taking on your sensitive content
- the locations of your sensitive and retained data
You also manage these features on the data classification page:
- trainable classifiers
- sensitive information types
- Learn about exact data match based sensitive information types
- content explorer
- activity explorer
You can find data classification in the Microsoft Purview compliance portal or Microsoft Defender portal > Classification > Data Classification.
Data classification will scan your sensitive content and labeled content before you create any policies. This is called zero change management. This lets you see the impact that all the retention and sensitivity labels are having in your environment and empower you to start assessing your protection and governance policy needs.
Tip
If you're not an E5 customer, use the 90-day Microsoft Purview solutions trial to explore how additional Purview capabilities can help your organization manage data security and compliance needs. Start now at the Microsoft Purview compliance portal trials hub. Learn details about signing up and trial terms.
Prerequisites
Permissions
In order to get access to the data classification page, an account must be assigned membership in any one of these roles or role groups.
Microsoft 365 role groups
- Global administrator
- Compliance administrator
- Security administrator
- Compliance data administrator
Note
As a best practice, always use the role with least privilege to grant access to Microsoft 365 data classification.
Roles and Role Groups
There are roles and role groups that you can use to fine tune your access controls.
Here's a list of applicable roles. To learn more about them, see Permissions in the Microsoft Purview compliance portal.
- Information Protection Admin
- Information Protection Analyst
- Information Protection Investigator
- Information Protection Reader
Here's a list of applicable role groups. To learn more about them, see Permissions in the Microsoft Purview compliance portal.
- Information Protection
- Information Protection Admins
- Information Protection Analysts
- Information Protection Investigators
- Information Protection Readers
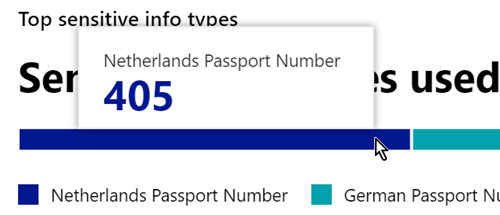
Sensitive information types used most in your content
Microsoft 365 comes with many definitions of sensitive information types, such as an item containing a social security number or a credit card number. For more information on sensitive information types, see Sensitive information type entity definitions.
The sensitive information type card shows the top sensitive information types that have been found and labeled across your organization.
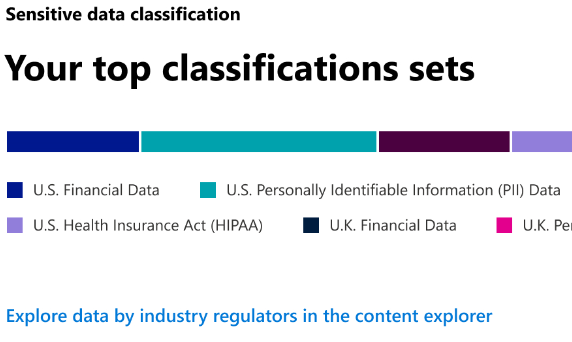
To find out how many items are in any given classification category, hover over the bar for the category.
Note
If the card displays the message "No data found with sensitive information", it means that there are no items in your organization that have been classified as being a sensitive information type or no items that have been crawled. To get started with labels, see:
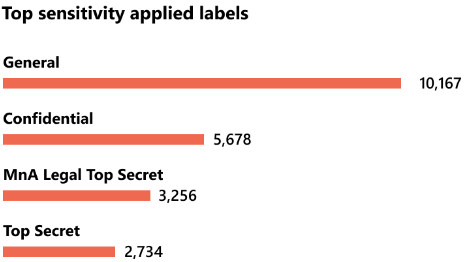
Top sensitivity labels applied to content
When you apply a sensitivity label to an item either by using Microsoft 365 apps and services or the Microsoft Purview Information Protection client and scanner, two things happen:
- A tag that indicates the value of the item to your org is embedded in the document and will follow it everywhere it goes.
- The presence of the tag enables various protective behaviors, such as mandatory watermarking or encryption. With end point protection enabled you can even prevent an item from leaving your organizational control.
For more information on sensitivity labels, see: Learn about sensitivity labels
Sensitivity labels must be enabled for files that are in SharePoint and OneDrive in order for the corresponding data to surface in the data classification page. For more information, see Enable sensitivity labels for files in SharePoint and OneDrive.
The sensitivity label card shows the number of items (email or document) by sensitivity level.
Note
If you haven't created or published any sensitivity labels or no content has had a sensitivity label applied, this card will display the message "No sensitivity labels detected". To get started with sensitivity labels, see Get started with sensitivity labels.
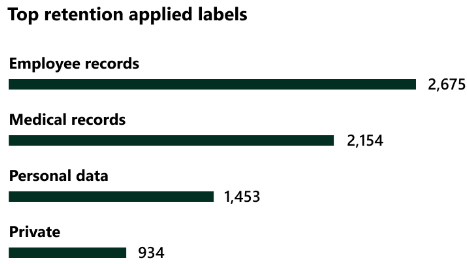
Top retention labels applied to content
Retention labels are used to manage the retention and disposition of content in your organization. When applied, they can be used to control how long an item will be kept before deletion, whether it should be reviewed prior to deletion, when its retention period expires, and whether it should be marked as a record. For more information, see Learn about retention policies and retention labels.
The top applied retention labels card shows you how many items have a given retention label.
Note
If this card displays the message, "No retention labels detected", it means you haven't created or published any retention labels or no content has had a retention label applied. To get started with retention labels, see:
Top activities detected
This card provides a quick summary of the most common actions that users are taking on the sensitivity labeled items. You can use the Activity explorer to drill deep down on the different activities that Microsoft 365 tracks on labeled content and content that is located on Windows 10 endpoints.
Note
If this card displays the message, "No activity detected" it means that there's been no activity on the files or that user and admin auditing isn't turned on. To turn the audit logs on , see:
Sensitivity and retention labeled data by location
The point of the data classification reporting is to provide visibility into the number of items that have which label as well as their location. These cards let you know how many labeled items the are in Exchange, SharePoint, and OneDrive etc.
Note
If this card displays the message, "No locations detected, it means you haven't created or published any sensitivity labels or no content has had a retention label applied. To get started with sensitivity labels, see:
See also
- View label activity
- View labeled content
- Learn about sensitivity labels
- Learn about retention policies and retention labels
- Learn about sensitive information types
- Sensitive information type entity definitions
- Learn about trainable classifiers (preview)
To learn how to use data classification to comply with data privacy regulations, see Deploy information protection for data privacy regulations with Microsoft 365 (aka.ms/m365dataprivacy).
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for