Understand the advanced hunting schema
Applies to:
- Microsoft Defender XDR
Important
Some information in this article relates to a prereleased product which may be substantially modified before it's commercially released. Microsoft makes no warranties, expressed or implied, with respect to the information provided here.
The advanced hunting schema is made up of multiple tables that provide either event information or information about devices, alerts, identities, and other entity types. To effectively build queries that span multiple tables, you need to understand the tables and the columns in the advanced hunting schema.
Get schema information
While constructing queries, use the built-in schema reference to quickly get the following information about each table in the schema:
- Tables description—type of data contained in the table and the source of that data.
- Columns—all the columns in the table.
- Action types—possible values in the
ActionTypecolumn representing the event types supported by the table. This information is provided only for tables that contain event information. - Sample query—example queries that feature how the table can be utilized.
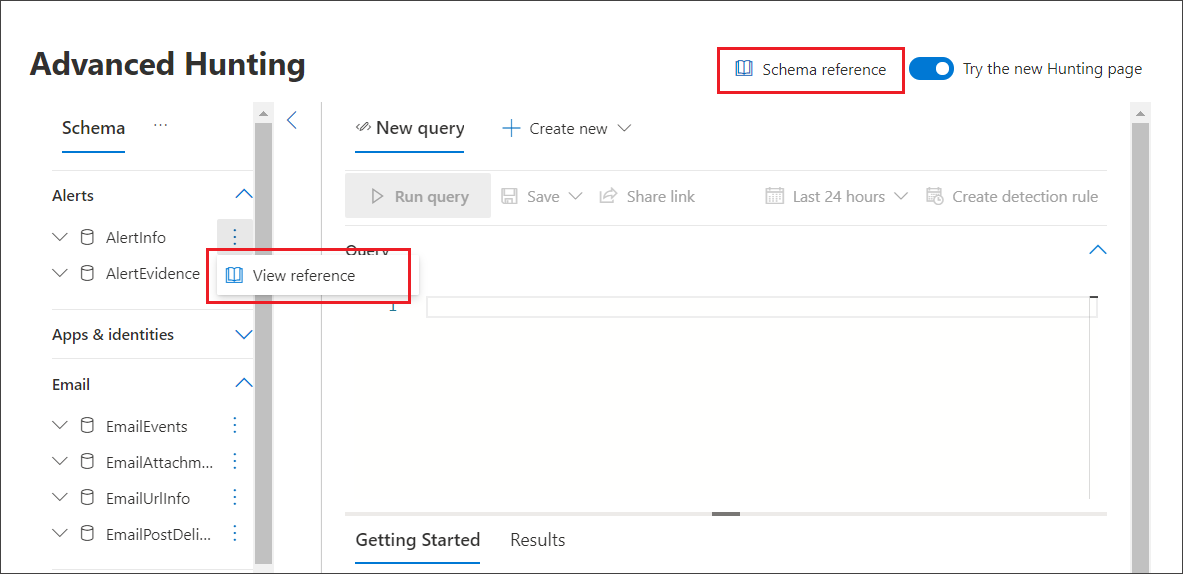
Access the schema reference
To quickly access the schema reference, select the View reference action next to the table name in the schema representation. You can also select Schema reference to search for a table.
Learn the schema tables
The following reference lists all the tables in the schema. Each table name links to a page describing the column names for that table. Table and column names are also listed in Microsoft Defender XDR as part of the schema representation on the advanced hunting screen.
| Table name | Description |
|---|---|
| AADSignInEventsBeta | Microsoft Entra interactive and non-interactive sign-ins |
| AADSpnSignInEventsBeta | Microsoft Entra service principal and managed identity sign-ins |
| AlertEvidence | Files, IP addresses, URLs, users, or devices associated with alerts |
| AlertInfo | Alerts from Microsoft Defender for Endpoint, Microsoft Defender for Office 365, Microsoft Defender for Cloud Apps, and Microsoft Defender for Identity, including severity information and threat categorization |
| BehaviorEntities | Behavior data types in Microsoft Defender for Cloud Apps |
| BehaviorInfo | Alerts from Microsoft Defender for Cloud Apps |
| CloudAppEvents | Events involving accounts and objects in Office 365 and other cloud apps and services |
| DeviceEvents | Multiple event types, including events triggered by security controls such as Microsoft Defender Antivirus and exploit protection |
| DeviceFileCertificateInfo | Certificate information of signed files obtained from certificate verification events on endpoints |
| DeviceFileEvents | File creation, modification, and other file system events |
| DeviceImageLoadEvents | DLL loading events |
| DeviceInfo | Machine information, including OS information |
| DeviceLogonEvents | Sign-ins and other authentication events on devices |
| DeviceNetworkEvents | Network connection and related events |
| DeviceNetworkInfo | Network properties of devices, including physical adapters, IP and MAC addresses, as well as connected networks and domains |
| DeviceProcessEvents | Process creation and related events |
| DeviceRegistryEvents | Creation and modification of registry entries |
| DeviceTvmHardwareFirmware | Hardware and firmware information of devices as checked by Defender Vulnerability Management |
| DeviceTvmInfoGathering | Defender Vulnerability Management assessment events including configuration and attack surface area states |
| DeviceTvmInfoGatheringKB | Metadata for assessment events collected in the DeviceTvmInfogathering table |
| DeviceTvmSecureConfigurationAssessment | Microsoft Defender Vulnerability Management assessment events, indicating the status of various security configurations on devices |
| DeviceTvmSecureConfigurationAssessmentKB | Knowledge base of various security configurations used by Microsoft Defender Vulnerability Management to assess devices; includes mappings to various standards and benchmarks |
| DeviceTvmSoftwareEvidenceBeta | Evidence info about where a specific software was detected on a device |
| DeviceTvmSoftwareInventory | Inventory of software installed on devices, including their version information and end-of-support status |
| DeviceTvmSoftwareVulnerabilities | Software vulnerabilities found on devices and the list of available security updates that address each vulnerability |
| DeviceTvmSoftwareVulnerabilitiesKB | Knowledge base of publicly disclosed vulnerabilities, including whether exploit code is publicly available |
| EmailAttachmentInfo | Information about files attached to emails |
| EmailEvents | Microsoft 365 email events, including email delivery and blocking events |
| EmailPostDeliveryEvents | Security events that occur post-delivery, after Microsoft 365 delivers the emails to the recipient mailbox |
| EmailUrlInfo | Information about URLs on emails |
| ExposureGraphEdges | Microsoft Security Exposure Management exposure graph edge information provides visibility into relationships between entities and assets in the graph |
| ExposureGraphNodes | Microsoft Security Exposure Management exposure graph node information, about organizational entities and their properties |
| IdentityDirectoryEvents | Events involving an on-premises domain controller running Active Directory (AD). This table covers a range of identity-related events and system events on the domain controller. |
| IdentityInfo | Account information from various sources, including Microsoft Entra ID |
| IdentityLogonEvents | Authentication events on Active Directory and Microsoft online services |
| IdentityQueryEvents | Queries for Active Directory objects, such as users, groups, devices, and domains |
| UrlClickEvents | Safe Links clicks from email messages, Teams, and Office 365 apps |
Related topics
- Advanced hunting overview
- Learn the query language
- Work with query results
- Use shared queries
- Hunt across devices, emails, apps, and identities
- Apply query best practices
Tip
Do you want to learn more? Engage with the Microsoft Security community in our Tech Community: Microsoft Defender XDR Tech Community.
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for