3.7.5.1 Received Extended Mode First Exchange Request
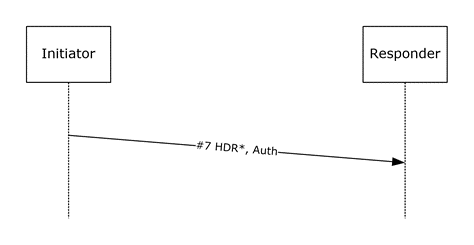
Figure 23: Transition to Extended Mode Initiator packet
If the responder is not in Quick Mode Responder Done state when it receives the above packet, the responder MUST tear down the corresponding main mode (MM) if it can match the packet to an existing main mode, or silently discard it otherwise.
On receiving the above packet in Quick Mode Responder Done state, the responder MUST verify that message #7 is constructed as follows:
HDR: The ISAKMP header MUST have a format identical to the first IKE phase 2 initiator packet, as specified in [RFC2409] section 5.5, except that the exchange type MUST be 245 (EM exchange type). The Encrypted flag MUST be set. The responder SHOULD<18> also verify that the message ID field value is set to one.
The payloads that remain MUST be encapsulated in a Crypto payload. If an error occurs at this stage or before, the responder MUST silently discard the message. The Crypto payload MUST be constructed as specified in section 3.3.5.1.
Auth: The proposed authentication methods. This payload MUST be processed identically to the Auth payload in the MM exchange (see section 3.3.5.1), except that all operations on the MMSAD are on the EM Auth method state.
If the responder encounters no errors while it processes message #7, the responder MUST construct message #8 in response, formatted as specified in the following diagram and constructed as follows:
HDR: The ISAKMP header MUST have an identical format to the first IKE phase 2 initiator packet, as specified in [RFC2409] section 5.5, except that the exchange type MUST be 245 (EM exchange type). The Encrypted flag MUST be set. The responder MUST also set the message ID value to zero.
The payloads that remain MUST be encapsulated in a Crypto payload. The Crypto payload MUST be constructed as specified in section 3.3.5.1.
Auth: The responder MUST determine which set of the proposed authentication methods is acceptable (by comparing the proposals with the PAD's IKE Peer Authentication Data (see [RFC4301] section 4.4.3.2) and MUST respond with at least one method of that set. To allow for Auth retry, the responder MUST respond with all valid authentication methods. When responding with multiple authentication methods, the responder MUST put the methods in its Auth payload in the same order as they were in the initiator payload.
GSS_ID: This payload MUST have identical format to the GSS_ID payload sent as part of the MM exchange (see section 3.3.5.1).
After sending this response, the Responder MUST transition to the Extended Mode Responder first exchange done state.

Figure 24: Quick Mode Synchronize Notify packet
If the responder encounters any errors in the processing of this message, it MUST be treated as an Invalid Message Received (section 3.7.7.1) event.