Windows Hello Enhanced Sign-in Security
Windows Hello enables a user to authenticate using their biometrics or a PIN eliminating the need for a password. Biometric authentication uses facial recognition or fingerprint to prove a user’s identity in a way that is secure, personal, and convenient. Enhanced Sign-in Security provides an additional level of security to biometric data by leveraging specialized hardware and software components, such as Virtualization Based Security (VBS) and Trusted Platform Module 2.0 to isolate and protect a user’s authentication data and secure the channel by which that data is communicated.
How does Enhanced Sign-in Security protect biometric data
Face
When Enhanced Sign-in Security is enabled, the face algorithm is protected using VBS to isolate it from the rest of Windows. The hypervisor is used to specify and protect memory regions, so that they can only be accessed by processes running in VBS. The hypervisor allows the face camera to write to these memory regions providing an isolated pathway to deliver face data from the camera to the face matching algorithm.
Face templates are generated in VBS by the protected face algorithm. When not in use, face template data is encrypted using keys generated and only accessible to VBS, and then stored on disk.
Fingerprint
Enhanced Sign-in Security is only supported on fingerprint sensors with match on sensor capabilities. This type of sensor includes a microprocessor and memory which can be used to isolate fingerprint matching and template storage using hardware.
Sensors that support Enhanced Sign-in Security have a certificate embedded during manufacturing. This certificate can be validated by the Windows biometric components running in VBS and is used to establish a secure session with the sensor. The sensor and Windows biometric components use this session to communicate enrollment operations and match results securely.
Credential Operations
The Windows biometric components running in VBS establish a secure channel to the TPM using information shared with VBS by the TPM during boot. When a matching operation is a success, the biometric components in VBS use this channel to authorize the usage of Windows Hello keys for authenticating the user with their identity provider, applications, and services.
How do I get Enhanced Sign-in Security
Enablement is dependent on specialized hardware, drivers, and firmware that are being pre-installed on the system. Device manufacturers can choose to enable Enhanced Sign-in Security on their devices during configuration of the device in factory.
System Compatibility
Compatible hardware and software components are required to enable Enhanced Sign-in Security:
- Devices with Windows 10 October 2020 update configured from factory
- Meet the requirements for Virtualization-Based Security (VBS) including Device Guard Enablement and Trusted Platform Module 2.0
- Biometric sensor hardware that supports Enhanced Sign-in Security
- Biometric sensor drivers compatible with Enhanced Sign-in Security
- Device firmware with a Secure Devices (SDEV) ACPI table properly configured by the device manufacturer for the included biometric hardware
Biometric Sensor Compatibility
Face Biometric Sensor
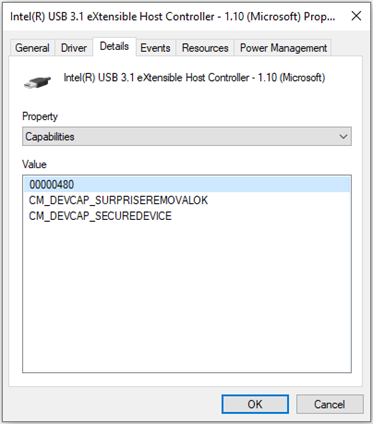
Enhanced Sign-in Security only supports some IR cameras on a limited number of chip sets. Supported cameras must support Enhanced Sign-in Security in firmware. Usage of the Windows inbox UVC camera driver is required. To check if the camera module is Enhanced Sign-in Security-capable, first go to Device Manager and expand the “Universal Serial Bus controllers” section. Right click on the device that has eXtensible Host Controller in the name and select the Properties option to view the device properties. If there are multiple entries for a host controller, check the properties section for all. Navigate to the Details tab of the driver and select Capabilities from the Property drop down menu. One of the devices should show it has the “CM_DEVCAP_SECUREDEVICE” capability.
Next, check the properties sections of the PC Cameras by going to the “Cameras” section in Device Manager. If there are multiple entries for PC Cameras, check the properties section for all. Navigate to the Details tab of the drivers and select Capabilities from the Property drop down menu. One of the PC camera devices should have the “CM_DEVCAP_SECUREDEVICE” capability.

Fingerprint Biometric Sensor
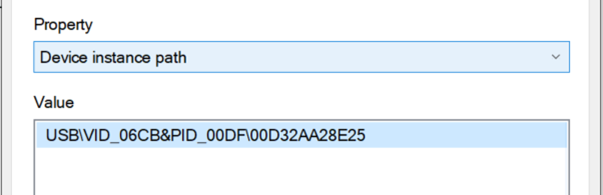
Enhanced Sign-in Security capable fingerprint sensors must be match on chip. The sensor must have a Microsoft issued certificate burned into the device during manufacturing. The device driver and firmware must support Enhanced Sign-in Security functionality. To check if a fingerprint module is Enhanced Sign-in Security-capable, first navigate open device manager and expand the Biometric devices section. There should be an entry for a fingerprint sensor. Right click the fingerprint reader entry and go to Properties, then Details. Under the Property option, select “Device instance path”.
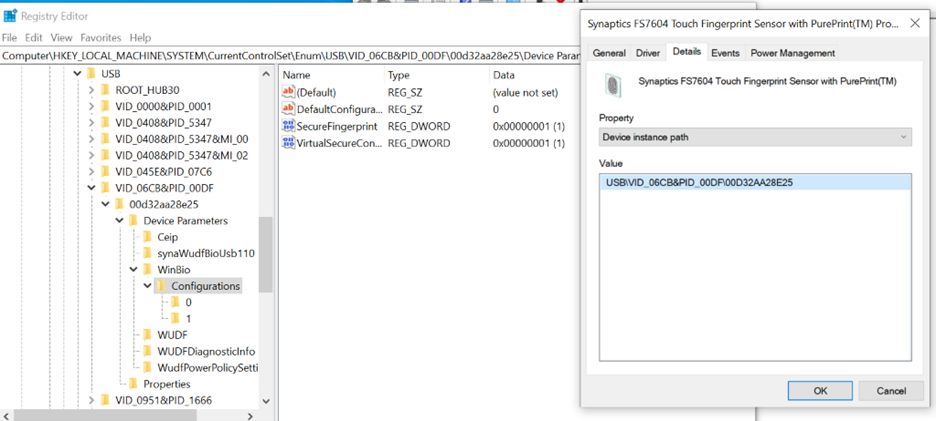
Open regedit.exe and navigate to HKLM\SYSTEM\CurrentControlSet\Enum\[DeviceInstancePath]\Device Parameters\WinBio\Configurations where DeviceInstancePath is the path listed in Device Manager. Select “Configurations”. There should be a registry key listed named “SecureFingerprint” with a data value of 1. If it does not exist, the device is not secure-capable.
Configurations should also have two folders beneath it: one labelled “0” and one labelled “1”. If there is only one folder and not two, the device is not secure-capable.
How do I know if Enhanced Sign-in Security is enabled
Security Center
In the Device Security section of the Windows Security application, there will be an entry for Enhanced Sign-in Security if it is enabled on the system. This entry will describe the hardware capability of the system. If the Enhanced Sign-in Security section is not present, the feature is not enabled on the system.
If there is a biometric sensor embedded in the device that does not support Enhanced Sign-in Security or that type of biometric hardware is absent from the system, it will be indicated by the “Unavailable due to incompatible hardware” description next to the corresponding sensor. This message indicates that the hardware does not follow the sensor requirements needed to support Enhanced Sign-in Security.
Event Viewer
The Windows biometric framework generates logs events when each sensor on a system is enumerated. These logs include information indicating whether a sensor is operating with Enhanced Sign-in Security enabled. Biometric event logs are found in Event Viewer under Event Viewer > Applications and Services Logs > Microsoft > Windows > Biometrics > Operational.
If the biometric device has been loaded properly by the Windows biometric framework there will be a log event with ID 1108 for the corresponding sensor. If the device is operating with Enhanced Sign-in Security enabled, the sensor will be specified as isolated in a “Virtual Secure Mode” process. If the device is not using Enhanced Sign-in Security, it will be specified as isolated in a “System” process.
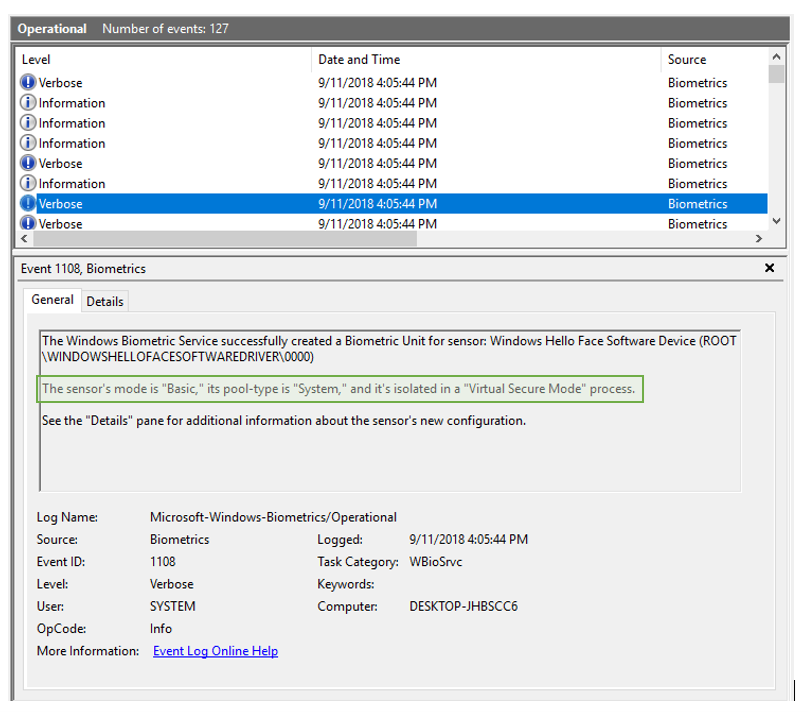
In the event 1108, cameras will be described using “Windows Hello Face Software Device (ROOT\WINDOWSHELLOFACESOFTWAREDRIVER\0000)” and fingerprint devices will be described using the device’s specific module and device ID. For fingerprint devices, the device ID can be found in device Manager under Biometric Devices > [Fingerprint Module] > Properties > Details > Device Instance Path.
Application Compatibility
For devices with Enhanced Sign-in Security-capable cameras, a Secure Devices (SDEV) table is required. When an SDEV table is implemented and VBS is turned on, the SDEV table is parsed by the Secure Kernel and restrictions are enforced on accessing Peripheral Component Interconnect (PCI) device configuration space. These restrictions are enacted to prevent malicious processes from manipulating the configuration space of secured devices specified in the SDEV table.
Applications that attempt to read/write the PCI configuration space, except by means explicitly supported by Windows, will result in bug checks when the SDEV table is parsed and enforced.
All drivers and software included in the device image must be tested for compatibility, given these software restrictions. Software or drivers that are distributed to the system via Windows Update, the Microsoft Store, or other acceptable channels by the device manufacturer should also be checked for compatibility. Without this verification, there may be unexpected behavior on the system.
Unsupported Scenarios
Enabling Enhanced Sign-in Support on Windows Upgrade
Enhanced Sign-in Security is currently only supported on devices configured by a device manufacturer to enable the capability with Windows 10 October 2020 update. In market devices that are hardware-capable that upgrade to this OS build are not currently supported.
Non-Enhanced Sign-in Supported Sensors
When Enhanced Sign-in Security is enabled, only biometric sensors that support Enhanced Sign-in Security will work on the system. All non-capable sensors will not be enumerated by the Windows Biometric framework.
It is the manufacturer’s decision on what hardware they include in the system and whether Enhanced Sign-in Security is enabled by default. If there are any concerns around biometric modalities being blocked, contact the device manufacturer for support.
Pluggable/Peripheral Biometric Sensors
Enhanced Sign-in Security is not supported for external fingerprint sensors or camera modules. With Enhanced Sign-in Security enabled, external or peripheral biometric sensor operations will be blocked, regardless of whether they are secure-capable or not. If you would like to use a peripheral with Enhanced Sign-in Security to log in with Windows Hello, see Disabling/Enabling Enhanced Sign-in Security
Wake on touch for fingerprint sensors
Wake on Touch (WoT) describes the ability for the fingerprint sensor to wake the system and login the user without requiring the user to touch the sensor twice. Devices that support Modern Standby enable Wake on Touch sensor behavior.
Starting in Windows 11 SE, version 22H2 and Windows 11 Pro Edu/Education, version 22H2 with KB5027303, WoT will be available for ESS devices.
Troubleshooting
Face/Fingerprint authentication is not working
If biometric authentication is not working, first check that VBS is running and that the secure component has started. To check if VBS is running, open System Information and check under “System Summary”; there should be an entry for “Virtualization Based Security” listed as Running.

Also check that the biometric isolation trust-lets are running. These should be listed under System Information > Software Environment > Running Tasks as “bioiso.exe” and “ngciso.exe”. If either of these checks fail, the system may not meet the requirements for Enhanced Sign-in Security. Attempt to restart the biometric service using (3) below.
To check that the secure connection succeeded, refer to the “How do I know if Enhanced Sign-in Security is enabled?” section.
- In Settings under Sign-in Options, remove the non-functioning enrollment and re-enroll; if the entry for Windows Hello Face/Fingerprint is unavailable with the condition “We couldn’t find a fingerprint scanner compatible with Windows Hello Face”, or something similar skip to (2) Check if authentication is working.
- In device manager, the sensor should be listed under Biometrics devices. Reinstall the driver by right clicking the name of the device and select Uninstall Device. Restart the device, at which point Windows will attempt to reinstall the driver. Check if authentication is working.
- To restart the biometric service, first remove PIN from the system by going to Sign-in Options and removing PIN. Open a command prompt as administrator and enter “net stop wbiosrvc” then “net start wbiosrvc”. Check if fingerprint authentication is working.
- If biometrics are still not working on the device, file a feedback item using Feedback Hub.
PIN is not working
PIN can be reset in the lock screen under Sign-in options. To do so, remove PIN and add it again. This will prompt PIN reset, which should restore PIN functionality.
Disable/Enable Enhanced Sign-in Security
Starting in Windows 11, version 22H2 with KB5031455, users can temporarily turn off ESS if they would like to use an external peripheral to authenticate with Windows Hello on their device.
You can use the Settings app to disable ESS. Select Start > Settings > Accounts > Sign-in options or use the following shortcut:
Under Additional settings > Sign in with an external camera or fingerprint reader, there's a toggle that allows you to enable or disable ESS:
- When the toggle is Off, ESS is enabled and you can't use external peripherals to sign in. Remember, you can still use external peripherals within apps like Teams
- When the toggle is On, ESS is disabled and you can use Windows Hello compatible peripherals to sign in