Overview of Windows Autopilot
Windows Autopilot is a collection of technologies used to set up and pre-configure new devices, getting them ready for productive use. Windows Autopilot can be used to deploy Windows PCs or HoloLens 2 devices. For more information about deploying HoloLens 2 with Autopilot, see Windows Autopilot for HoloLens 2.
You can also use Windows Autopilot to reset, repurpose, and recover devices. This solution enables an IT department to achieve these goals with little to no infrastructure to manage, with a process that's easy and simple.
Windows Autopilot simplifies the Windows device lifecycle, for both IT and end users, from initial deployment to end of life. Using cloud-based services, Windows Autopilot:
- Reduces the time IT spends on deploying, managing, and retiring devices.
- Reduces the infrastructure required to maintain the devices.
- Maximizes ease of use for all types of end users.
See the following video:
Process overview
When new Windows devices are initially deployed, Windows Autopilot uses the OEM-optimized version of Windows client. This version is preinstalled on the device, so you don't have to maintain custom images and drivers for every device model. Instead of re-imaging the device, your existing Windows installation can be transformed into a "business-ready" state that can:
- Apply settings and policies.
- Install apps.
- Change the edition of Windows being used to support advanced features. For example, from Windows Pro to Windows Enterprise.
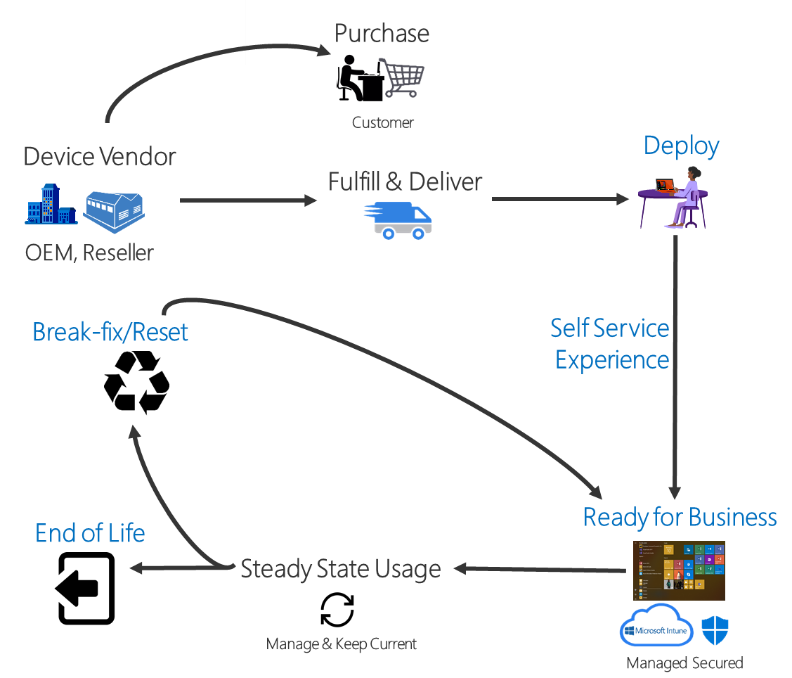
Once deployed, you can manage Windows devices with:
- Microsoft Intune.
- Windows Update for Business.
- Microsoft Configuration Manager.
- Other similar tools from 3rd parties.
Requirements
A supported version of Windows 11 or Windows 10 semi-annual channel is required to use Windows Autopilot. For more information, see Windows Autopilot software, networking, configuration, and licensing requirements.
Summary
Traditionally, IT pros spend significant time building and customizing images that are later deployed to devices. Windows Autopilot introduces a new approach.
- From the user's perspective, it only takes a few simple operations to make their device ready to use.
- From the IT pro's perspective, the only interaction required from the end user is to connect to a network and to verify their credentials. Everything beyond that is automated.
Windows Autopilot enables you to:
- Automatically join devices to Microsoft Entra ID or Active Directory (via Microsoft Entra hybrid join). For more information about the differences between these two join options, see Introduction to device management in Microsoft Entra ID.
- Auto-enroll devices into MDM services, such as Microsoft Intune (Requires a Microsoft Entra ID P1 or P2 subscription for configuration).
- Create and auto-assign devices to configuration groups based on a device's profile.
- Customize OOBE content specific to the organization.
Existing device can also be quickly prepared for a new user with Windows Autopilot Reset. The Reset capability is also useful in break/fix scenarios to quickly bring a device back to a business-ready state.
Tutorial
For a tutorial with detailed instructions on configuring Windows Autopilot, see Windows Autopilot scenarios.
Related articles
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for