4713(S): Kerberos policy was changed.
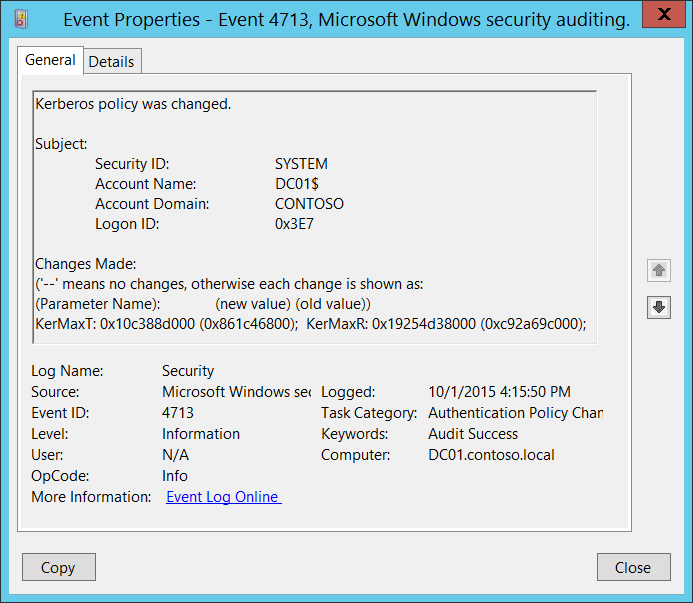
Subcategory: Audit Authentication Policy Change
Event Description:
This event generates when Kerberos policy was changed.
This event is generated only on domain controllers.
Note For recommendations, see Security Monitoring Recommendations for this event.
Event XML:
- <Event xmlns="http://schemas.microsoft.com/win/2004/08/events/event">
- <System>
<Provider Name="Microsoft-Windows-Security-Auditing" Guid="{54849625-5478-4994-A5BA-3E3B0328C30D}" />
<EventID>4713</EventID>
<Version>0</Version>
<Level>0</Level>
<Task>13569</Task>
<Opcode>0</Opcode>
<Keywords>0x8020000000000000</Keywords>
<TimeCreated SystemTime="2015-10-01T23:15:50.811774300Z" />
<EventRecordID>1049772</EventRecordID>
<Correlation />
<Execution ProcessID="500" ThreadID="4116" />
<Channel>Security</Channel>
<Computer>DC01.contoso.local</Computer>
<Security />
</System>
- <EventData>
<Data Name="SubjectUserSid">S-1-5-18</Data>
<Data Name="SubjectUserName">DC01$</Data>
<Data Name="SubjectDomainName">CONTOSO</Data>
<Data Name="SubjectLogonId">0x3e7</Data>
<Data Name="KerberosPolicyChange">KerMaxT: 0x10c388d000 (0x861c46800); KerMaxR: 0x19254d38000 (0xc92a69c000);</Data>
</EventData>
</Event>
Required Server Roles: Active Directory domain controller.
Minimum OS Version: Windows Server 2008.
Event Versions: 0.
Field Descriptions:
Subject:
- Security ID [Type = SID]: SID of account that made a change to Kerberos policy. Event Viewer automatically tries to resolve SIDs and show the account name. If the SID cannot be resolved, you will see the source data in the event.
Note A security identifier (SID) is a unique value of variable length used to identify a trustee (security principal). Each account has a unique SID that is issued by an authority, such as an Active Directory domain controller, and stored in a security database. Each time a user logs on, the system retrieves the SID for that user from the database and places it in the access token for that user. The system uses the SID in the access token to identify the user in all subsequent interactions with Windows security. When a SID has been used as the unique identifier for a user or group, it cannot ever be used again to identify another user or group. For more information about SIDs, see Security identifiers.
Account Name [Type = UnicodeString]: the name of the account that made a change to Kerberos policy.
Account Domain [Type = UnicodeString]: subject’s domain or computer name. Formats vary, and include the following:
Domain NETBIOS name example: CONTOSO
Lowercase full domain name: contoso.local
Uppercase full domain name: CONTOSO.LOCAL
For some well-known security principals, such as LOCAL SERVICE or ANONYMOUS LOGON, the value of this field is “NT AUTHORITY”.
For local user accounts, this field will contain the name of the computer or device that this account belongs to, for example: “Win81”.
Logon ID [Type = HexInt64]: hexadecimal value that can help you correlate this event with recent events that might contain the same Logon ID, for example, “4624: An account was successfully logged on.”
Changes Made [Type = UnicodeString]: '--' means no changes, otherwise each change is shown as: Parameter_Name: new_value (old_value). Here is a list of possible parameter names:
| Parameter Name | Description |
|---|---|
| KerProxy | 1. Maximum tolerance for computer clock synchronization. To convert the KerProxy to minutes you need to: Convert the value to decimal value. Divide value by 600000000. |
| KerMaxR | 1. Maximum lifetime for user ticket renewal. To convert the KerProxy to days you need to: Convert the value to decimal value. Divide value by 864000000000. |
| KerMaxT | 1. Maximum lifetime for user ticket. To convert the KerMaxT to hours you need to: Convert the value to decimal value. Divide value by 36000000000. |
| KerMinT | 1. Maximum lifetime for service ticket. To convert the KerMinT to minutes you need to: Convert the value to decimal value. Divide value by 600000000. |
| KerOpts | - Enforce user logon restrictions: 0x80 – Enabled 0x0 - Disabled |
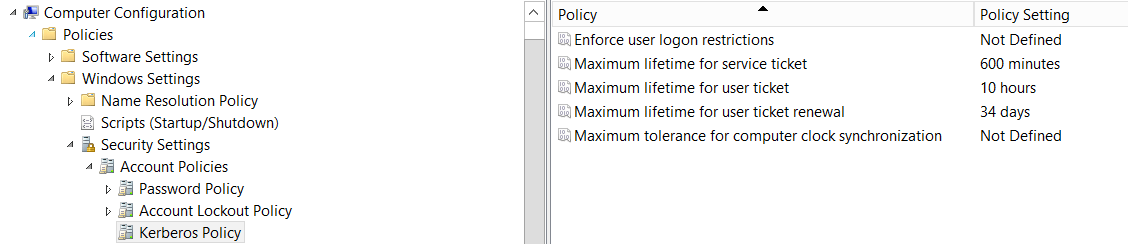
This event shows changes in “Kerberos policy”. Here is location of Kerberos policies in Group Policy management console:
Security Monitoring Recommendations
For 4713(S): Kerberos policy was changed.
- Any changes in Kerberos policy reported by current event must be monitored and an alert should be triggered. If this change was not planned, investigate the reason for the change.