Proactively hunt for threats with advanced hunting in Microsoft Defender XDR
Applies to:
- Microsoft Defender XDR
Advanced hunting is a query-based threat hunting tool that lets you explore up to 30 days of raw data. You can proactively inspect events in your network to locate threat indicators and entities. The flexible access to data enables unconstrained hunting for both known and potential threats.
Advanced hunting supports two modes, guided and advanced. Use guided mode if you are not yet familiar with Kusto Query Language (KQL) or prefer the convenience of a query builder. Use advanced mode if you are comfortable using KQL to create queries from scratch.
To start hunting, read Choose between guided and advanced modes to hunt in Microsoft Defender XDR.
You can use the same threat hunting queries to build custom detection rules. These rules run automatically to check for and then respond to suspected breach activity, misconfigured machines, and other findings.
Advanced hunting supports queries that check a broader data set coming from:
- Microsoft Defender for Endpoint
- Microsoft Defender for Office 365
- Microsoft Defender for Cloud Apps
- Microsoft Defender for Identity
To use advanced hunting, turn on Microsoft Defender XDR.
For more information on advanced hunting in Microsoft Defender for Cloud Apps data, see the video.
Get access
To use advanced hunting or other Microsoft Defender XDR capabilities, you need an appropriate role in Microsoft Entra ID. Read about required roles and permissions for advanced hunting.
Also, your access to endpoint data is determined by role-based access control (RBAC) settings in Microsoft Defender for Endpoint. Read about managing access to Microsoft Defender XDR.
Data freshness and update frequency
Advanced hunting data can be categorized into two distinct types, each consolidated differently.
- Event or activity data—populates tables about alerts, security events, system events, and routine assessments. Advanced hunting receives this data almost immediately after the sensors that collect them successfully transmit them to the corresponding cloud services. For example, you can query event data from healthy sensors on workstations or domain controllers almost immediately after they are available on Microsoft Defender for Endpoint and Microsoft Defender for Identity.
- Entity data—populates tables with information about users and devices. This data comes from both relatively static data sources and dynamic sources, such as Active Directory entries and event logs. To provide fresh data, tables are updated with any new information every 15 minutes, adding rows that might not be fully populated. Every 24 hours, data is consolidated to insert a record that contains the latest, most comprehensive data set about each entity.
Time zone
Queries
Advanced hunting data uses the UTC (Universal Time Coordinated) timezone.
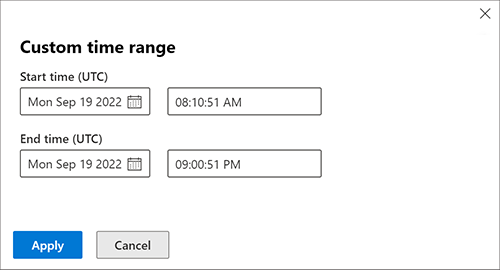
Queries should be created in UTC.
Results
Advanced hunting results are converted to the timezone set in Microsoft Defender XDR.
Related topics
- Choose between guided and advanced hunting modes
- Build hunting queries using guided mode
- Learn the query language
- Understand the schema
- Microsoft Graph security API
- Custom detections overview
Tip
Do you want to learn more? Engage with the Microsoft Security community in our Tech Community: Microsoft Defender XDR Tech Community.
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for