Network share configuration assessment
Applies to:
- Microsoft Defender Vulnerability Management
- Microsoft Defender XDR
- Microsoft Defender for Servers Plan 2
Note
To use this feature you'll require Microsoft Defender Vulnerability Management Standalone or if you're already a Microsoft Defender for Endpoint Plan 2 customer, the Defender Vulnerability Management add-on.
The ability to share files and folders over a network allows users to provide access to resources like files, documents, and media to other people on the network. As network shares can be easily accessed by network users, some common weaknesses exist that can cause network shares to be vulnerable.
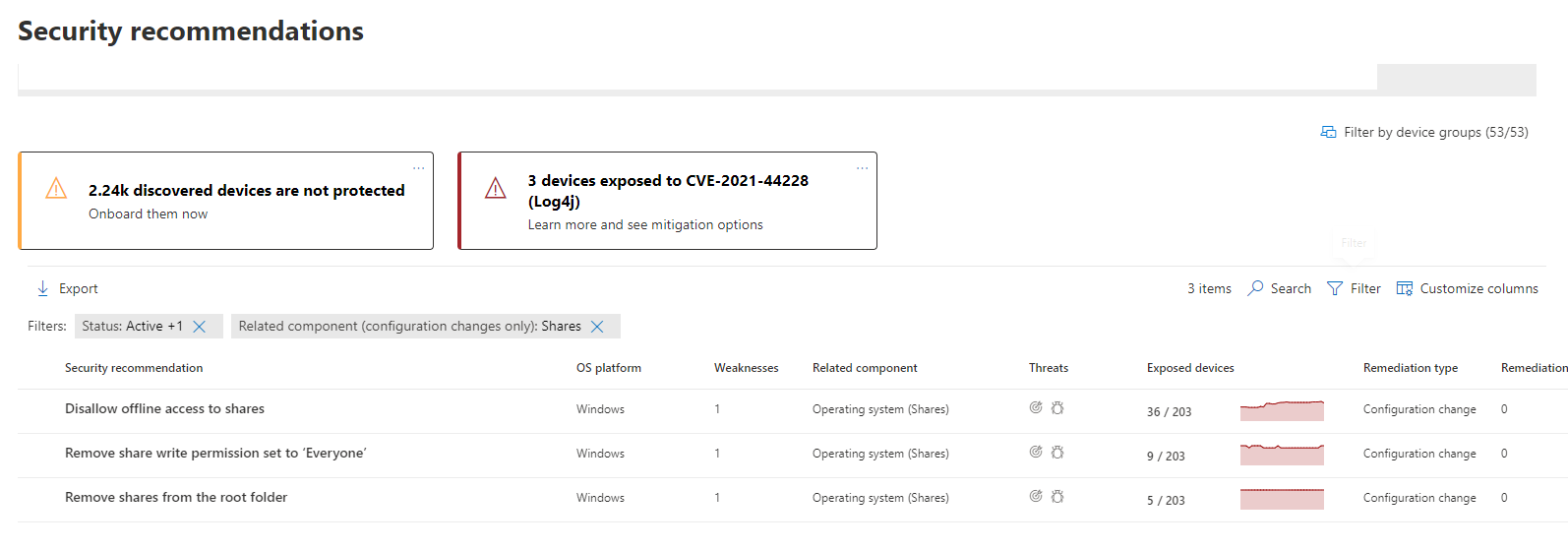
When vulnerable network share configurations are identified, they're mapped to actionable security recommendations in the Security recommendations page. The following recommendations can help protect against vulnerabilities in network shares that could be exploited by attackers:
- Disallow offline access to shares
- Remove shares from the root folder
- Remove share write permission set to 'Everyone'
- Set folder enumeration for shares
Tip
Did you know you can try all the features in Microsoft Defender Vulnerability Management for free? Find out how to sign up for a free trial.
Find information about exposed network shares
To see security recommendations addressing network share configurations:
- Go to Vulnerability management > Recommendations.
- Select Filters and choose Related component > OS > Shares.
- Select Apply.
If there are network shares with vulnerabilities to address, they'll appear in the list of recommendations
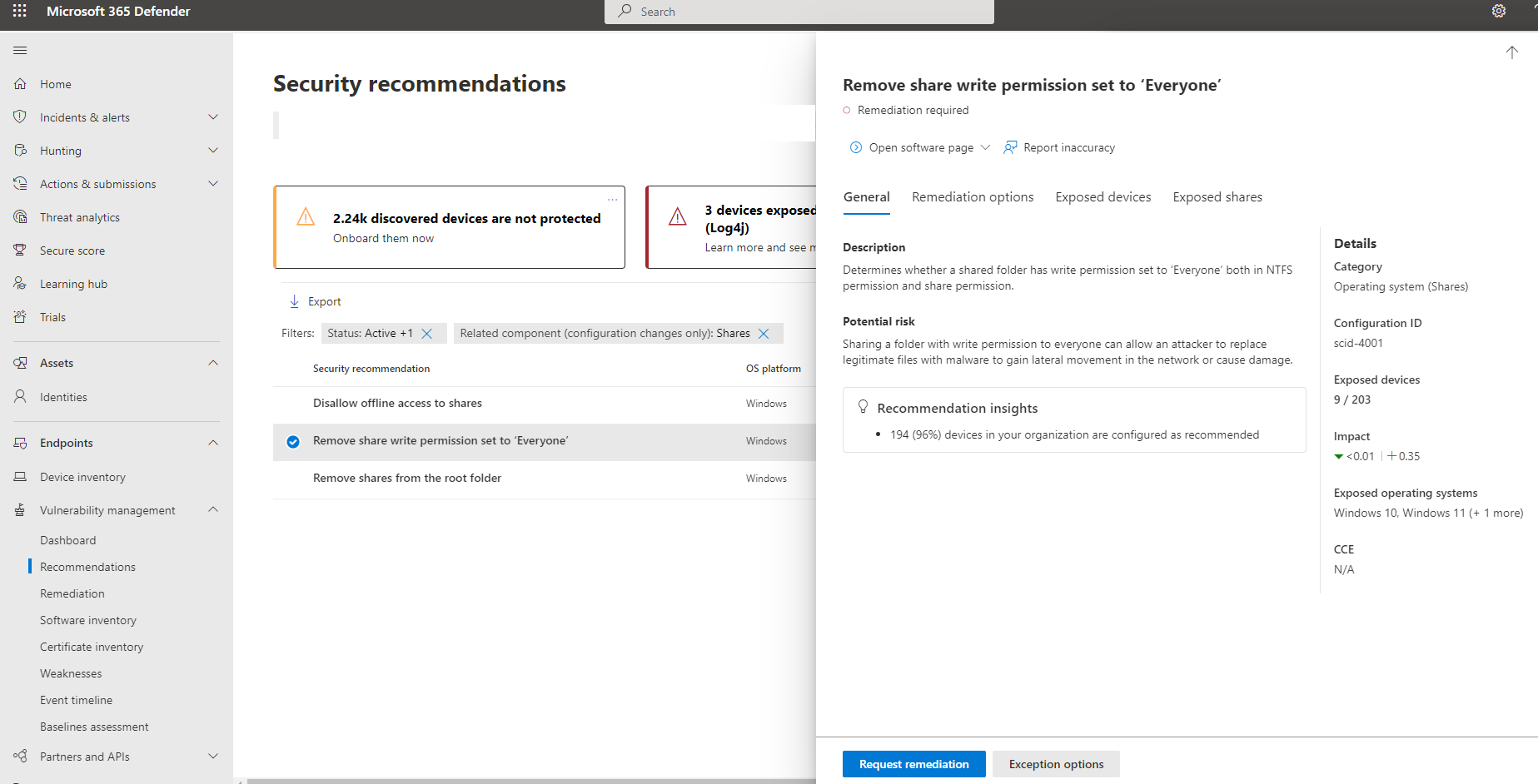
Select a recommendation to see a flyout with information on the vulnerable network share configuration:
Explore the Exposed devices and Exposed shares tabs for details of the exposed entities in your organization.
Request remediation for the network share configuration
You can view and submit a remediation request from the remediation options tab:
View configuration remediation activities
Go to Vulnerability management > Remediation and filter by the remediation type, "configuration change" to see the activity item related to this change.
Related articles
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for