在 Azure 虚拟机(经典)上配置 SQL Server 的 Azure Key Vault 集成
概述
SQL Server 加密功能多种多样,包括透明数据加密 (TDE)、列级加密 (CLE) 和备份加密。 这些加密形式要求管理和存储用于加密的加密密钥。 Azure Key Vault (AKV) 服务专用于在一个高度可用的安全位置改进这些密钥的安全性和管理。 SQL Server 连接器 使 SQL Server 能够使用 Azure 密钥保管库中的这些密钥。
重要
Azure 具有用于创建和处理资源的两个不同的部署模型:资源管理器部署模型和经典部署模型。 本文介绍如何使用经典部署模型。 Microsoft 建议大多数新部署使用资源管理器模型。
如果在本地计算机上运行 SQL Server,请按照此处提供的步骤通过本地 SQL Server 计算机访问 Azure Key Vault。 但对于 Azure VM 中的 SQL Server,可以通过使用 Azure 密钥保管库集成 功能节省时间。 通过使用几个 Azure PowerShell cmdlet 来启用此功能,可以自动为 SQL VM 进行必要的配置以便访问密钥保管库。
启用此功能后,它会自动安装 SQL Server 连接器、配置 EKM 提供程序以访问 Azure 密钥保管库,并创建凭据以使你能够访问保管库。 在前面提到的本地文档列出的步骤中,可以看到此功能自动完成步骤 2 和步骤 3。 仍需手动执行的唯一操作是创建密钥保管库和密钥。 之后,自动进行 SQL VM 的整个设置。 在此功能完成设置后,可以执行 T-SQL 语句,以按照通常的方式加密数据库或备份。
准备 AKV 集成
若要使用 Azure Key Vault 集成来配置 SQL Server VM,有以下几个先决条件:
以下各节描述了这些先决条件,以及稍后运行 PowerShell cmdlet 需要收集的信息。
注意
建议使用 Azure Az PowerShell 模块与 Azure 交互。 请参阅安装 Azure PowerShell 以开始使用。 若要了解如何迁移到 Az PowerShell 模块,请参阅 将 Azure PowerShell 从 AzureRM 迁移到 Az。
安装 Azure PowerShell
请确保已安装最新的 Azure PowerShell 模块。 有关详细信息,请参阅如何安装和配置 Azure PowerShell。
将应用程序注册到 Azure Active Directory
首先,订阅中需要有 Azure Active Directory (AAD)。 其优点之一是允许为特定用户和应用程序授予对密钥保管库的权限。
然后,将应用程序注册到 AAD。 这会提供一个服务主体帐户,使你有权访问 VM 所需的密钥保管库。 在 Azure Key Vault 文章中,用户可以在将应用程序注册到 Azure Active Directory 部分中找到这些步骤,或者可以在此博客文章的获取应用程序的标识部分中看到这些步骤以及屏幕截图。 在完成这些步骤之前,需要在注册期间收集以下信息,之后在 SQL VM 上启用 Azure Key Vault 集成时需要这些信息。
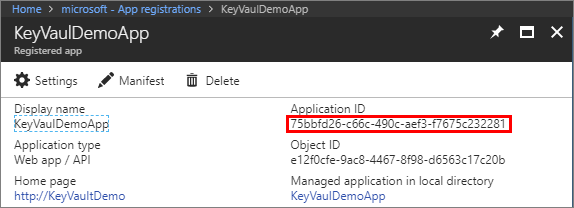
添加应用程序后,在“已注册应用”边栏选项卡上找到“应用程序 ID”(也称为 AAD ClientID 或 AppID) 。 稍后会将该应用程序 ID 分配给 PowerShell 脚本中的 $spName(服务主体名称)参数,以启用 Azure 密钥保管库集成 。
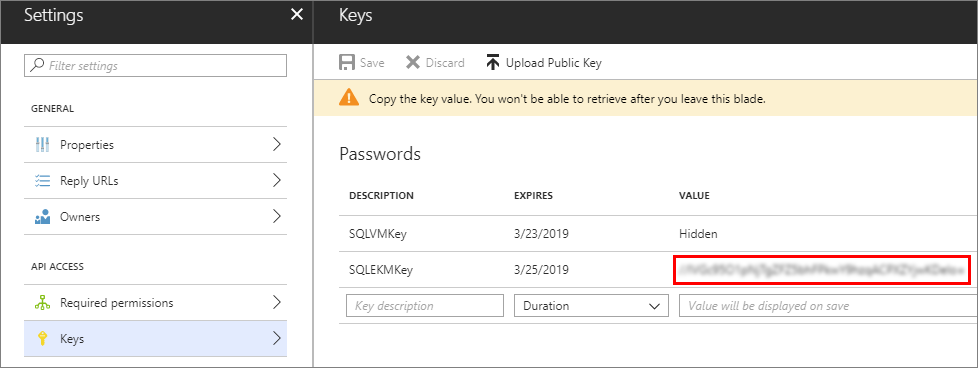
在执行这些步骤期间,请在创建密钥时复制密钥的密码,如下面的屏幕截图中所示。 稍后会将此密钥密码分配给 PowerShell 脚本中的 $spSecret(服务主体密码)参数 。
应用程序 ID 和机密将还可用于在 SQL Server 中创建凭据。
必须为此新的应用程序 ID(或客户端 ID)授予以下访问权限:get、wrapKey、unwrapKey 。 可通过 Set-AzKeyVaultAccessPolicy cmdlet 实现此操作。 有关详细信息,请参阅 Azure 密钥保管库概述。
创建密钥保管库
若要使用 Azure Key Vault 来存储将用于在 VM 中加密的密钥,将需要对密钥保管库的访问权限。 如果尚未设置密钥保管库,请按照开始使用 Azure Key Vault 一文中的步骤创建一个。 在完成这些步骤之前,需要在设置期间收集一些信息,之后在 SQL VM 上启用 Azure Key Vault 集成时需要这些信息。
New-AzKeyVault -VaultName 'ContosoKeyVault' -ResourceGroupName 'ContosoResourceGroup' -Location 'East Asia'
进行创建密钥保管库的步骤时,请注意返回的 vaultUri 属性,它是密钥保管库 URL 。 下面显示了该步骤中提供的示例,其中的密钥保管库名称是 ContosoKeyVault,因此密钥保管库 URL 为 https://contosokeyvault.vault.azure.net/ 。
稍后会将该密钥保管库 URL 分配给 PowerShell 脚本中的 $akvURL 参数,以启用 Azure Key Vault 集成 。
创建密钥保管库后,需要向密钥保管库添加密钥,稍后在 SQL Server 中创建非对称密钥时,会引用此密钥。
配置 AKV 集成
使用 PowerShell 来配置 Azure 密钥保管库集成。 以下各节概述了所需的参数,并提供了一个示例 PowerShell 脚本。
安装 SQL Server IaaS 扩展
了解输入参数
下表列出在下一节中运行 PowerShell 脚本所需的参数。
| 参数 | 说明 | 示例 |
|---|---|---|
| $akvURL | 密钥保管库 URL | "https://contosokeyvault.vault.azure.net/" |
| $spName | 服务主体名称 | “fde2b411-33d5-4e11-af04eb07b669ccf2” |
| $spSecret | 服务主体密码 | “9VTJSQwzlFepD8XODnzy8n2V01Jd8dAjwm/azF1XDKM =” |
| $credName | 凭据名称:AKV 集成在 SQL Server 内创建一个凭据,使 VM 具有对密钥保管库的访问权限。 为此凭据选择一个名称。 | “mycred1” |
| $vmName | 虚拟机名称:以前创建的 SQL VM 的名称。 | “myvmname” |
| $serviceName | 服务名称:与 SQL VM 关联的云服务名称。 | “mycloudservicename” |
使用 PowerShell 启用 AKV 集成
New-AzureVMSqlServerKeyVaultCredentialConfig cmdlet 为 Azure 密钥保管库集成功能创建配置对象。 Set-AzureVMSqlServerExtension 通过 KeyVaultCredentialSettings 参数配置此集成。 以下步骤显示如何使用这些命令。
在 Azure PowerShell 中,首先使用特定的值配置输入参数,如本主题前面各节中所述。 下面的脚本就是一个示例。
$akvURL = "https:\//contosokeyvault.vault.azure.net/" $spName = "fde2b411-33d5-4e11-af04eb07b669ccf2" $spSecret = "9VTJSQwzlFepD8XODnzy8n2V01Jd8dAjwm/azF1XDKM=" $credName = "mycred1" $vmName = "myvmname" $serviceName = "mycloudservicename"然后使用以下脚本来配置和启用 AKV 集成。
$secureakv = $spSecret | ConvertTo-SecureString -AsPlainText -Force $akvs = New-AzureVMSqlServerKeyVaultCredentialConfig -Enable -CredentialName $credname -AzureKeyVaultUrl $akvURL -ServicePrincipalName $spName -ServicePrincipalSecret $secureakv Get-AzureVM -ServiceName $serviceName -Name $vmName | Set-AzureVMSqlServerExtension -KeyVaultCredentialSettings $akvs | Update-AzureVM
SQL IaaS 代理扩展会使用此新配置来更新 SQL VM。
后续步骤
启用 Azure Key Vault 集成之后,可以在 SQL VM 上启用 SQL Server 加密。 首先,需要在密钥保管库内创建一个非对称密钥,并在 VM 上的 SQL Server 中创建一个对称密钥。 然后,将能够执行 T-SQL 语句,启用对数据库和备份的加密。
可以利用以下几种形式的加密:
以下 Transact-SQL 脚本提供针对每个区域的示例。
先决条件示例
每个示例基于两个先决条件:密钥保管库中名为 CONTOSO_KEY 的非对称密钥,以及由 AKV 集成功能创建的名为 Azure_EKM_cred 的凭据 。 以下 Transact-SQL 命令设置这些运行示例所需的先决条件。
USE master;
GO
--create credential
--The <<SECRET>> here requires the <Application ID> (without hyphens) and <Secret> to be passed together without a space between them.
CREATE CREDENTIAL Azure_EKM_cred
WITH IDENTITY = 'keytestvault', --keyvault
SECRET = '<<SECRET>>'
FOR CRYPTOGRAPHIC PROVIDER AzureKeyVault_EKM_Prov;
--Map the credential to a SQL login that has sysadmin permissions. This allows the SQL login to access the key vault when creating the asymmetric key in the next step.
ALTER LOGIN [SQL_Login]
ADD CREDENTIAL Azure_EKM_cred;
CREATE ASYMMETRIC KEY CONTOSO_KEY
FROM PROVIDER [AzureKeyVault_EKM_Prov]
WITH PROVIDER_KEY_NAME = 'KeyName_in_KeyVault', --The key name here requires the key we created in the key vault
CREATION_DISPOSITION = OPEN_EXISTING;
透明数据加密 (TDE)
创建数据库引擎将用于 TDE 的 SQL Server 登录名,然后向其添加凭据。
USE master; -- Create a SQL Server login associated with the asymmetric key -- for the Database engine to use when it loads a database -- encrypted by TDE. CREATE LOGIN EKM_Login FROM ASYMMETRIC KEY CONTOSO_KEY; GO -- Alter the TDE Login to add the credential for use by the -- Database Engine to access the key vault ALTER LOGIN EKM_Login ADD CREDENTIAL Azure_EKM_cred; GO创建将用于 TDE 的数据库加密密钥。
USE ContosoDatabase; GO CREATE DATABASE ENCRYPTION KEY WITH ALGORITHM = AES_128 ENCRYPTION BY SERVER ASYMMETRIC KEY CONTOSO_KEY; GO -- Alter the database to enable transparent data encryption. ALTER DATABASE ContosoDatabase SET ENCRYPTION ON; GO
加密备份
创建数据库引擎将用于加密备份的 SQL Server 登录名,然后向其添加凭据。
USE master; -- Create a SQL Server login associated with the asymmetric key -- for the Database engine to use when it is encrypting the backup. CREATE LOGIN EKM_Login FROM ASYMMETRIC KEY CONTOSO_KEY; GO -- Alter the Encrypted Backup Login to add the credential for use by -- the Database Engine to access the key vault ALTER LOGIN EKM_Login ADD CREDENTIAL Azure_EKM_cred ; GO备份数据库,同时使用密钥保管库中存储的非对称密钥指定加密。
USE master; BACKUP DATABASE [DATABASE_TO_BACKUP] TO DISK = N'[PATH TO BACKUP FILE]' WITH FORMAT, INIT, SKIP, NOREWIND, NOUNLOAD, ENCRYPTION(ALGORITHM = AES_256, SERVER ASYMMETRIC KEY = [CONTOSO_KEY]); GO
列级加密 (CLE)
此脚本创建一个受密钥保管库中的非对称密钥保护的对称密钥,然后使用该对称密钥对数据库中的数据进行加密。
CREATE SYMMETRIC KEY DATA_ENCRYPTION_KEY
WITH ALGORITHM=AES_256
ENCRYPTION BY ASYMMETRIC KEY CONTOSO_KEY;
DECLARE @DATA VARBINARY(MAX);
--Open the symmetric key for use in this session
OPEN SYMMETRIC KEY DATA_ENCRYPTION_KEY
DECRYPTION BY ASYMMETRIC KEY CONTOSO_KEY;
--Encrypt syntax
SELECT @DATA = ENCRYPTBYKEY(KEY_GUID('DATA_ENCRYPTION_KEY'), CONVERT(VARBINARY,'Plain text data to encrypt'));
-- Decrypt syntax
SELECT CONVERT(VARCHAR, DECRYPTBYKEY(@DATA));
--Close the symmetric key
CLOSE SYMMETRIC KEY DATA_ENCRYPTION_KEY;
其他资源
有关如何使用这些加密功能的详细信息,请参阅将 EKM 用于 SQL Server 加密功能。
请注意,本文中的步骤假定用户已经具有在 Azure 虚拟机上运行的 SQL Server。 如果没有,请参阅在 Azure 中预配 SQL Server 虚拟机。 有关在 Azure VM 中运行 SQL Server 的其他指南,请参阅 Azure 虚拟机上的 SQL Server 概述。