调查“Microsoft Defender for Endpoint设备”列表中的设备
适用于:
希望体验 Defender for Endpoint? 注册免费试用版。
调查在特定设备上引发的警报的详细信息,以确定可能与该警报或潜在违规范围相关的其他行为或事件。
注意
作为调查或响应过程的一部分,可以从设备收集调查包。 方法如下: 从设备收集调查包。
每当在门户中看到受影响的设备时,都可以选择它们,以打开有关该设备的详细报告。 受影响的设备在以下方面进行标识:
调查特定设备时,会看到:
- 设备详细信息
- 响应操作
- 选项卡 (概述、警报、时间线、安全建议、软件清单、发现的漏洞、缺少 KB)
- 卡片 (活动警报、登录用户、安全评估、设备运行状况)
注意
由于产品限制,在确定“上次查看”时间范围时,设备配置文件不会考虑所有网络证据, (如设备页面上以及) 所示。 例如,即使计算机时间线中提供了较新的警报或数据,“设备”页中的“上次看到”值也可能显示较旧的时间范围。
设备详细信息
设备详细信息部分提供设备的域、OS 和运行状况状态等信息。 如果设备上有可用的调查包,则会看到一个链接,用于下载包。
响应操作
响应操作沿着特定设备页的顶部运行,包括:
- 在地图中查看
- 设备值
- 设置严重性
- 管理标签
- 隔离设备
- 限制应用执行
- 运行防病毒扫描
- 收集调查程序包
- 启动实时响应会话
- 启动自动调查
- 咨询威胁专家
- 操作中心
可以在操作中心、特定设备页或特定文件页中执行响应操作。
有关如何在设备上执行操作的详细信息,请参阅 在设备上执行响应操作。
有关详细信息,请参阅 调查用户实体。
注意
在地图中查看和设置严重性是 Microsoft 曝光管理的功能,目前以公共预览版提供。
选项卡
选项卡提供与设备相关的安全和威胁防护信息。 在每个选项卡中,可以通过从列标题上方的栏中选择“ 自定义列 ”来自定义显示的列。
概述
“ 概述 ”选项卡显示活动警报、登录用户和安全评估的 卡片 。
事件和警报
“ 事件和警报 ”选项卡提供与设备关联的事件和警报的列表。 此列表是 警报队列的筛选版本,显示事件、警报、严重性 (高、中、低、信息性) 、队列中的状态 (新、正在进行、已解决) 、分类 (未设置、false 警报、真实警报) 、调查状态、警报类别、谁正在处理警报以及最后一个活动。 还可以筛选警报。
选择警报后,将显示一个浮出控件。 在此面板中,可以管理警报并查看更多详细信息,例如事件编号和相关设备。 一次可以选择多个警报。
若要查看警报的全页视图,请选择警报的标题。
日程表
“ 时间线 ”选项卡提供设备上观察到的事件和关联警报的时间顺序视图。 这可以帮助你关联与设备相关的任何事件、文件和 IP 地址。
使用时间线还可以有选择地向下钻取给定时间段内发生的事件。 可以查看在所选时间段内设备上发生的事件的时态序列。 若要进一步控制视图,可以按事件组进行筛选或自定义列。
某些功能包括:
- 特定事件的搜索
- 使用搜索栏查找特定时间线事件。
- 筛选特定日期的事件
- 选择表格左上角的日历图标以显示过去一天、一周、30 天或自定义范围内的事件。 默认情况下,设备时间线设置为显示过去 30 天内的事件。
- 使用时间线通过突出显示 节跳转到特定时刻。 时间线上的箭头可精确定位自动调查
- 导出详细的设备时间线事件
- 为当前日期或指定日期范围导出设备时间线,最长为 7 天。
有关某些事件的更多详细信息,请参阅 其他信息 部分。 这些详细信息因事件类型而异,例如:
- 由 应用程序防护 包含 - Web 浏览器事件受隔离容器限制
- 检测到活动威胁 - 威胁检测是在威胁运行时发生的
- 修正失败 - 尝试修正检测到的威胁已调用,但失败
- 修正成功 - 检测到的威胁已停止并清理
- 用户绕过警告 - Windows Defender SmartScreen 警告已被用户消除并重写
- 检测到可疑脚本 - 发现正在运行的潜在恶意脚本
- 警报类别 - 如果事件导致生成警报,则警报类别 (横向移动,例如提供)
事件详情
选择事件以查看有关该事件的相关详细信息。 将显示一个面板以显示常规事件信息。 如果适用且数据可用,则还会显示显示相关实体及其关系的关系图。
若要进一步检查事件和相关事件,可以通过选择“搜寻相关事件”来快速运行高级搜寻查询。 该查询返回所选事件以及同一终结点上大约同时发生的其他事件的列表。
安全建议
安全建议是从 Microsoft Defender for Endpoint 的漏洞管理功能生成的。 选择建议会显示一个面板,你可以在其中查看相关详细信息,例如建议的说明以及与未实施建议相关的潜在风险。 有关详细信息 ,请参阅安全建议 。
安全策略
“ 安全策略 ”选项卡显示设备上应用的终结点安全策略。 可以看到策略、类型、状态和上次检查时间的列表。 选择策略名称会转到策略详细信息页,可在其中查看策略设置状态、已应用设备和已分配的组。
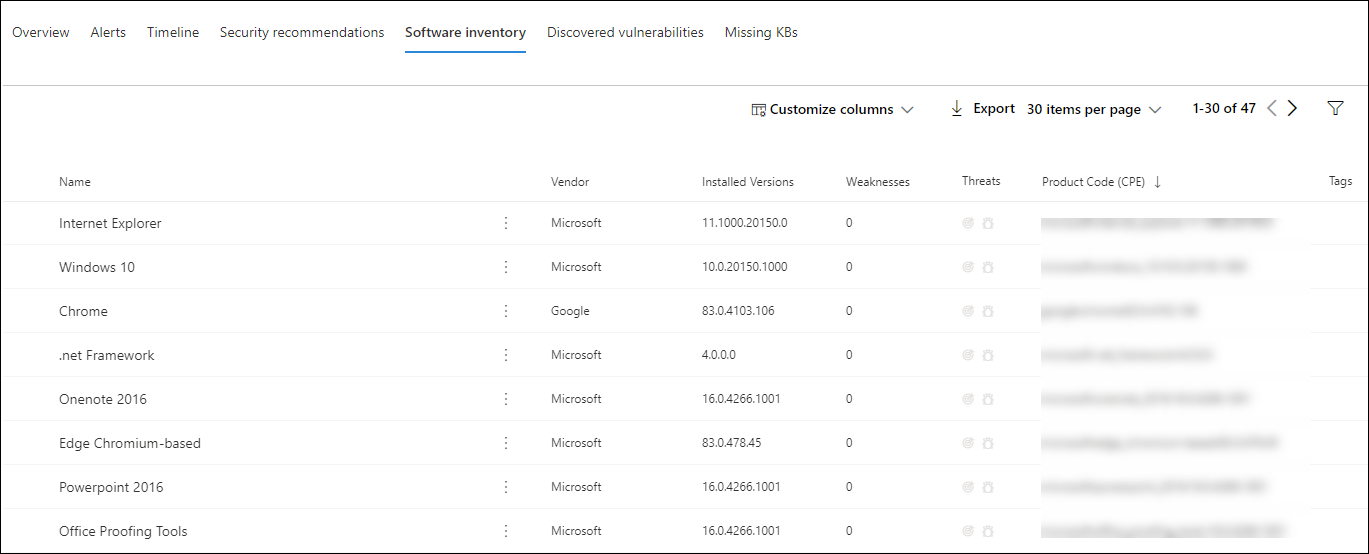
软件清单
使用“ 软件清单 ”选项卡,可以查看设备上的软件以及任何弱点或威胁。 选择软件名称可转到软件详细信息页,可在其中查看安全建议、发现的漏洞、已安装设备和版本分发。 有关详细信息,请参阅 软件清单 。
发现的漏洞
“ 发现漏洞 ”选项卡显示设备上发现漏洞的名称、严重性和威胁见解。 如果选择特定漏洞,则会看到说明和详细信息。
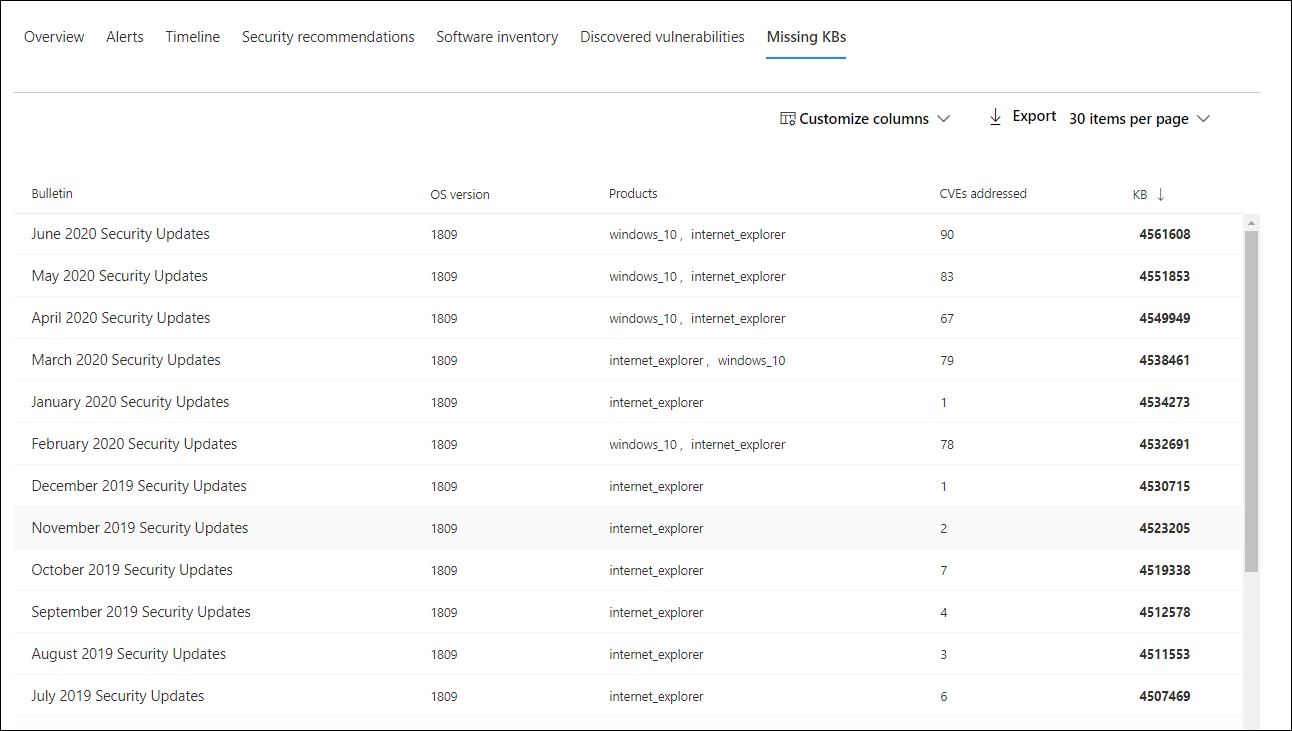
缺少 KB
“ 缺少 KB ”选项卡列出了设备缺少的安全更新。
卡片
活动警报
Azure 高级威胁防护卡显示与设备及其风险级别相关的警报的高级概述(如果使用Microsoft Defender for Identity功能),并且存在任何活动警报。 有关详细信息,请参阅 警报 向下钻取。
注意
需要同时在 Microsoft Defender for Identity 和 Defender for Endpoint 上启用集成才能使用此功能。 在 Defender for Endpoint 中,可以在高级功能中启用此功能。 有关如何启用高级功能的详细信息,请参阅 启用高级功能。
已登录用户
登录用户卡显示过去 30 天内登录的用户数,以及最常登录和最不频繁的用户。 选择“ 查看所有用户” 链接将打开详细信息窗格,其中显示用户类型、登录类型以及用户首次和上次查看时间等信息。 有关详细信息,请参阅 调查用户实体。
注意
“最频繁”用户值仅根据成功以交互方式登录的用户的证据进行计算。 但是, “所有用户 ”侧窗格计算各种用户登录次数,因此,鉴于这些用户可能不具有交互性,预计在侧窗格中会看到更频繁的用户。
安全评估
安全评估卡显示总体暴露级别、安全建议、已安装的软件和发现的漏洞。 设备的暴露级别由其挂起的安全建议的累积影响决定。
设备运行状况
设备运行状况卡显示特定设备的汇总运行状况报告。 以下消息之一显示在卡顶部,以指示设备的总体状态 (按从高到低) 顺序列出:
- Defender 防病毒未处于活动状态
- 安全智能不是最新的
- 引擎不是最新的
- 快速扫描失败
- 完全扫描失败
- 平台不是最新的
- 安全智能更新状态未知
- 引擎更新状态未知
- 快速扫描状态未知
- 完全扫描状态未知
- 平台更新状态未知
- 设备是最新的
- 状态不适用于 macOS & Linux
卡中的其他信息包括:上次完全扫描、上次快速扫描、安全智能更新版本、引擎更新版本、平台更新版本和 Defender 防病毒模式。
灰色圆圈表示数据未知。
注意
macOS 和 Linux 设备的总体状态消息当前显示为“状态不适用于 macOS & Linux”。 目前,状态摘要仅适用于 Windows 设备。 表中的所有其他信息都是最新的,显示所有受支持平台的每个设备运行状况信号的单独状态。
若要深入了解设备运行状况报告,可以转到 “报告 > 设备运行状况”。 有关详细信息,请参阅 Microsoft Defender for Endpoint 中的设备运行状况和符合性报告。
注意
Defender 防病毒模式的日期和时间当前不可用。
相关文章
- 查看并组织 Microsoft Defender for Endpoint 警报队列
- 管理Microsoft Defender for Endpoint警报
- 调查Microsoft Defender for Endpoint警报
- 调查与 Defender for Endpoint 警报关联的文件
- 调查与 Defender for Endpoint 警报关联的 IP 地址
- 调查与 Defender for Endpoint 警报关联的域
- 在 Defender for Endpoint 中调查用户帐户
- 安全建议
- 软件库存
提示
想要了解更多信息? Engage技术社区中的 Microsoft 安全社区:Microsoft Defender for Endpoint技术社区。
反馈
即将发布:在整个 2024 年,我们将逐步淘汰作为内容反馈机制的“GitHub 问题”,并将其取代为新的反馈系统。 有关详细信息,请参阅:https://aka.ms/ContentUserFeedback。
提交和查看相关反馈