向助手添加最终用户身份验证
重要提示
继在生成式人工智能的重大投资和跨 Microsoft Copilot 的增强集成之后,Power Virtual Agents 功能和特性现已成为 Microsoft Copilot Studio 的一部分。
在我们更新文档和培训内容时,一些文章和截图可能会参考 Power Virtual Agents。
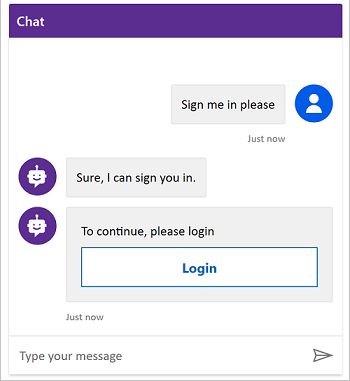
可以直接在助手对话内启用用户身份验证。 用户身份验证意味着您可以在变量中获取用户的基本属性(如名称和 ID),还可以提示用户使用身份验证节点登录、检索该用户的用户令牌,然后使用该令牌从后端系统检索用户的信息。
备注
在 Web 应用和 Microsoft Teams 中创建的助手将身份验证预先配置为使用仅用于 Teams 和 Power Apps 身份验证。
您还可以配置单一登录 (SSO),让您的用户无需手动登录。 有关详细信息,请参阅为 Web 配置 SSO。
先决条件
向主题添加用户身份验证,以便允许客户直接在对话中登录。 然后,您可以使用用户变量个性化对话,或代表用户访问后端系统。
使用 Microsoft Entra ID 配置手动身份验证
在您的主题中使用身份验证之前,您需要使用 Microsoft Entra ID 配置用户身份验证。
- 按照使用 Microsoft Entra ID 配置用户身份验证中的说明进行操作。
- 返回到本文。
使用“登录系统”主题添加用户身份验证
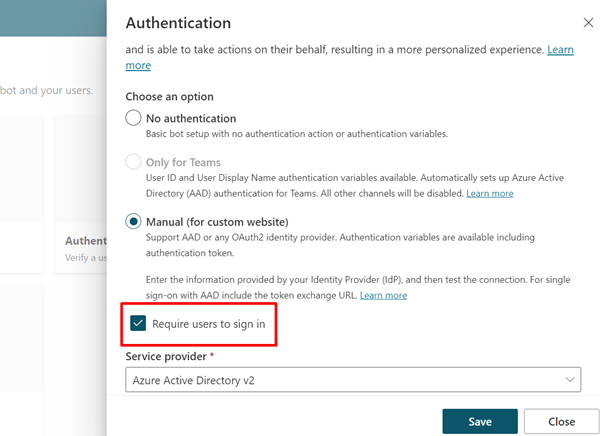
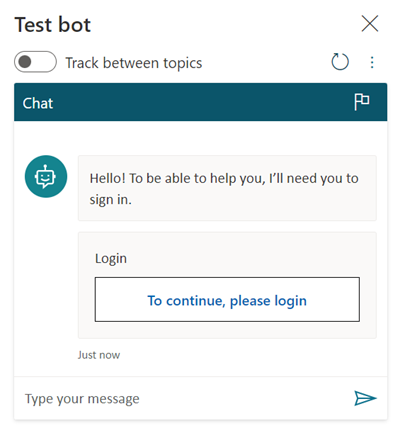
当您创建助手时,Microsoft Copilot Studio 会自动添加一个名为登录的系统主题。 若要使用,您必须将您的助手身份验证设置为手动,并且要求用户登录。 当客户开始与助手对话时,登录主题会触发,并提示用户登录。 您可以酌情针对您的助手自定义登录主题。
在导航菜单中的设置下面,选择安全性。
选择身份验证磁贴。
选择手动(对于自定义网站),然后选择要求用户登录。
向自定义主题添加用户身份验证
登录主题会在对话开始时对用户进行身份验证。 若要允许用户以后登录,可以将身份验证节点添加到任何自定义主题中。
当客户输入其用户名和密码时,可能会提示他们输入验证码。 用户登录后,将不会再次提示他们,即使他们到达另一个身份验证节点也不例外。
在导航菜单中的设置下面,选择安全性。
选择身份验证磁贴。
关闭要求用户登录。
在导航菜单中,选择主题,然后打开您要向其中添加身份验证的主题。
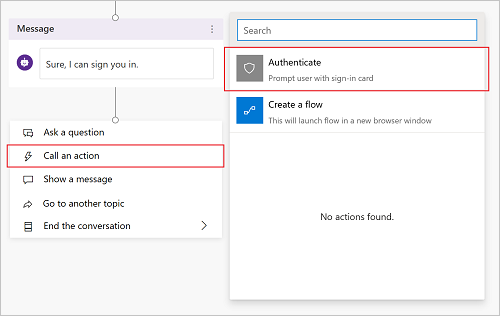
选择添加节点 (+),再选择调用操作,然后选择身份验证。
使用配置有标识提供者的用户测试主题。
提示
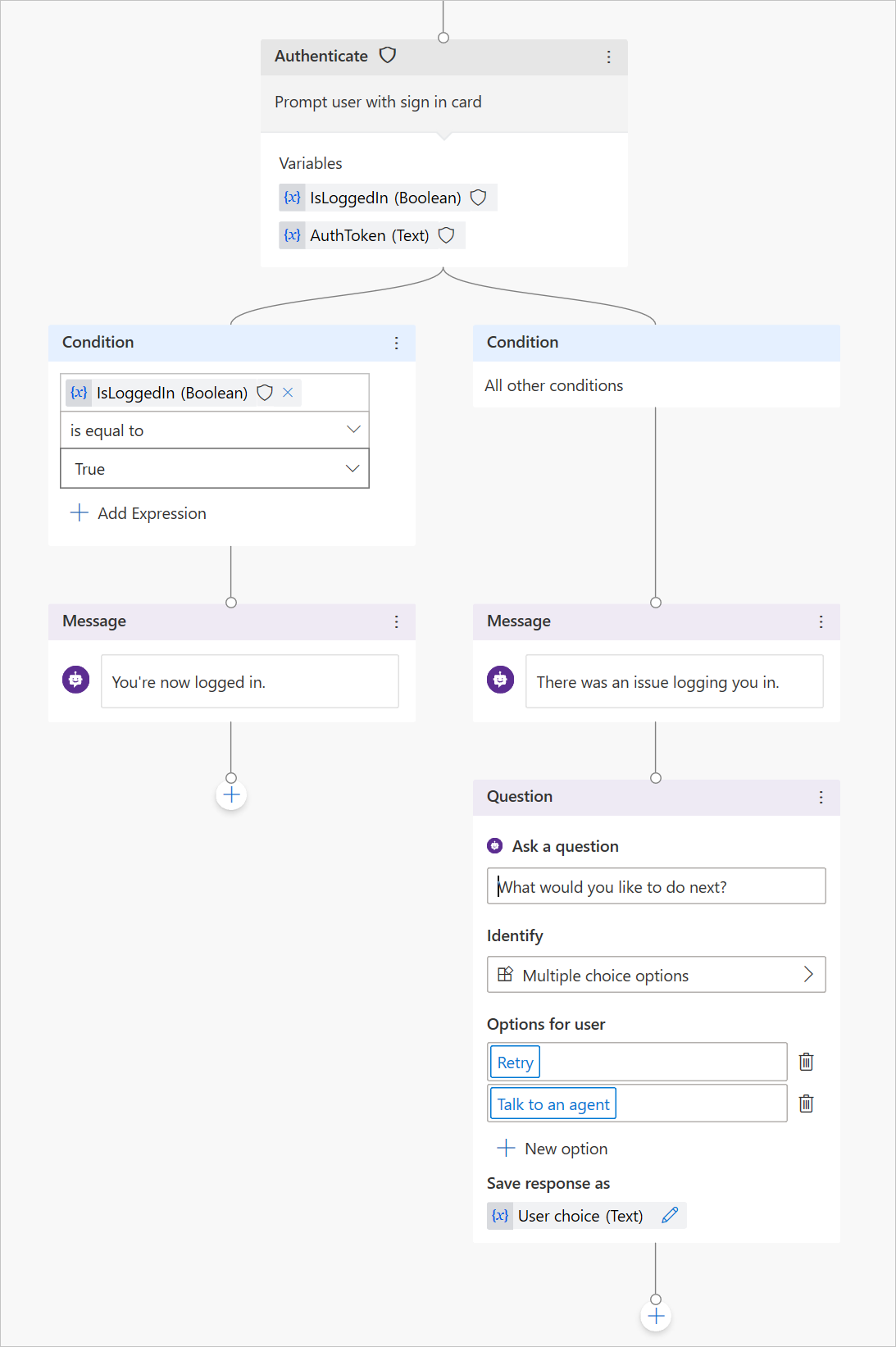
针对登录成功和失败创建登录路径很重要。 登录可能由于多种原因而失败,包括标识提供者的登录体验错误。
身份验证变量
为助手配置用户身份验证后,您可以在主题中使用身份验证变量。 下表根据您选择的身份验证选项比较这些变量的可用性:
| 身份验证变量 | 无身份验证 | 仅适用于 Teams 和 Power Apps | 手动 |
|---|---|---|---|
| User.DisplayName | 不可用 | 空闲 | 空闲 |
| User.FirstName | 不可用 | 空闲 | 空闲 |
| User.LastName | 不可用 | 空闲 | 空闲 |
| User.PrincipalName | 不可用 | 空闲 | 空闲 |
| User.Email | 不可用 | 空闲 | 空闲 |
| User.Id | 不可用 | 空闲 | 空闲 |
| User.IsLoggedIn | 不可用 | 空闲 | 空闲 |
| User.AccessToken | 不可用 | 不可用 | 空闲 |
| SignInReason | 不可用 | 空闲 | 空闲 |
User.DisplayName
警告
不保证此变量包含值。 通过标识提供者的用户进行测试,以确保您的主题可以正确运行。
User.DisplayName 变量包含存储在标识提供者中的显示名称。 请使用此变量来问候或引用最终用户,而无需他们明确告知助手他们的姓名,让对话更加个性化。
只要在配置手动身份验证时定义了 profile 范围,Microsoft Copilot Studio 就会根据标识提供者提供的 name 声明自动设置 User.DisplayName 的值。 有关范围的更多信息,请参阅使用 Microsoft Entra ID 配置用户身份验证。
User.Id
警告
不保证此变量包含值。 通过标识提供者的用户进行测试,以确保您的主题可以正确运行。
User.Id 变量包含存储在标识提供者中的 userID。 使用 Power Automate 流中的此变量调用将 UserID 作为值的 API。
Microsoft Copilot Studio 将根据标识提供者提供的 sub 声明自动设置 User.DisplayName 的值。
User.IsLoggedIn
User.IsLoggedIn 是一个存储用户的登录状态的布尔型变量。 true 的值指示用户已登录。 可使用此变量在主题中创建分支逻辑来检查成功登录,或仅在用户已登录时获取用户信息。
User.AccessToken
警告
务必将 User.AccessToken 变量仅传递到可信源。 其中包含用户身份验证信息,如果受到威胁,可能伤害用户。
User.AccessToken 变量中包含用户登录后获取的用户令牌。 可以将此变量传递到 Power Automate 流,以使其连接到后端 API 并获取用户信息,或代表用户执行操作。
请勿在消息节点内或您不信任的流中使用 User.AccessToken。
SignInReason
SignInReason是一个选择类型变量,指示用户何时必须登录。 它有两个可能的值:
SignInRequired指示用户必须在开始对话时使用登录系统主题登录。 要求用户登录必须打开。Initializer表示如果用户尚未登录,并且他们在对话中达到使用身份验证变量的时刻,则会提示他们登录。
相关主题
您还可以配置单一登录 (SSO),让您的用户无需手动登录。 有关详细信息,请参阅为 Web 配置 SSO。
反馈
即将发布:在整个 2024 年,我们将逐步淘汰作为内容反馈机制的“GitHub 问题”,并将其取代为新的反馈系统。 有关详细信息,请参阅:https://aka.ms/ContentUserFeedback。
提交和查看相关反馈