[Windbg Script] Tracing MessageBox calls
In the past I worked on a support case where I needed to find out if some MessageBox from a C++ application was displayed and, if positive, what the message was.
I got inconsistent answers whenever I asked the user, so I didn’t know if the MessageBox appeared or what the message was.
It sounded like another perfect scenario where a script might help! J
Actually, it helped me a lot and I hope it helps you, too.
This script maps MessageBox calls and logs the message from the MessageBox onto the Windbg screen and into a text file as well.
After debugging the application you should use “.logclose” to close the log. Then you can search for the string “ß Text from MessageBox” and you’ll get all the MessageBox the application has shown!
You can use DBMon.exe or DebugView.exe to see the messages from the MessageBox windows. I implemented this feature on my original script based on this blog article.
I never tested it on .NET applications, but it should work because MessageBox is called under the hood from some .NET Framework calls.
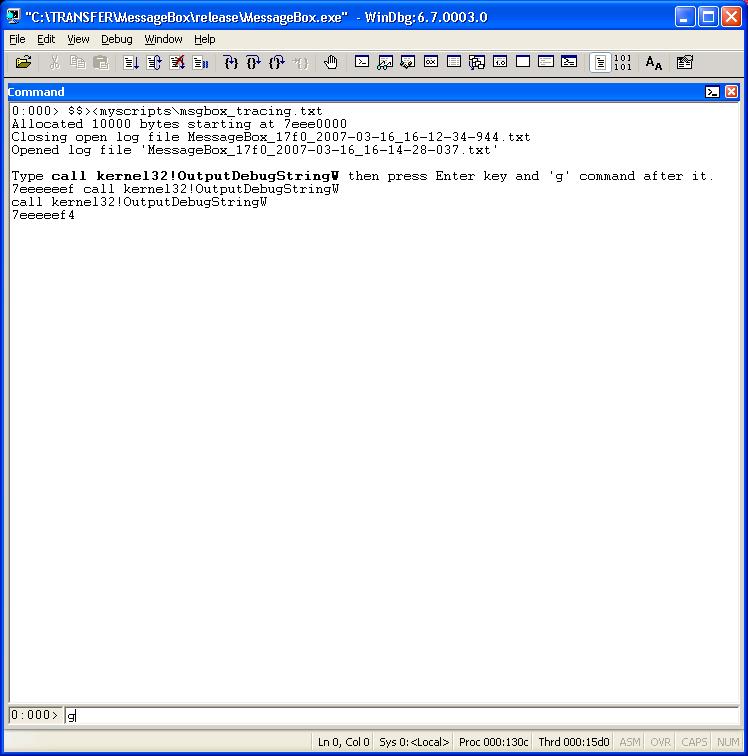
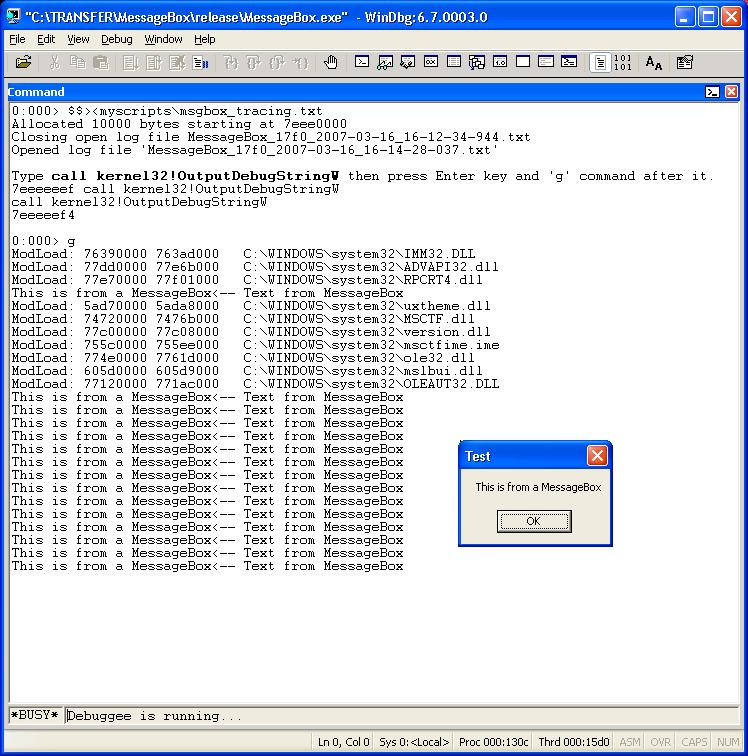
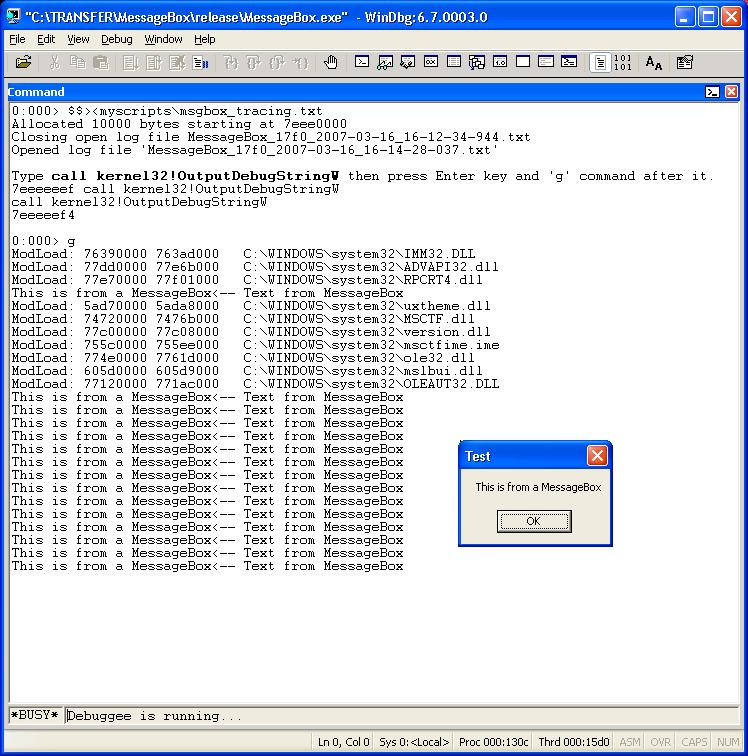
These are the screenshots:
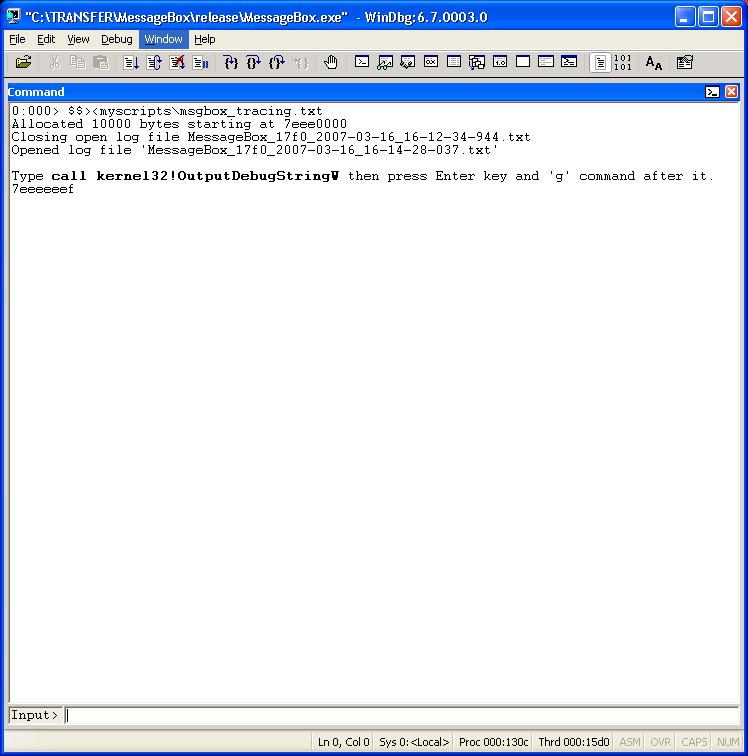
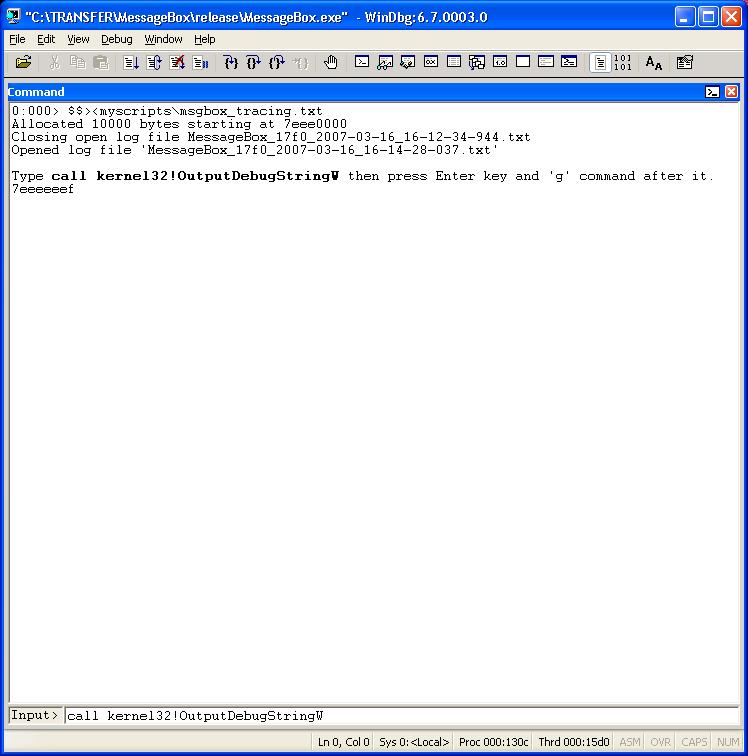
Attention! After the command above press Enter key twice not just once… Yeah, I know… I know… I should fix the screenshot… J
Source code for MSGBOX_TRACING.TXT:
$$
$$ =============================================================================
$$ Log MessageBox messages in a log file.
$$ The log file name starts with MessageBox string.
$$
$$ Compatibility: Win32.
$$
$$ Usage: $$>< to run the script.
$$
$$ Requirements: Public symbols.
$$
$$ Roberto Alexis Farah
$$ Blog: https://blogs.msdn.com/debuggingtoolbox/
$$
$$ All my scripts are provided "AS IS" with no warranties, and confer no rights.
$$ =============================================================================
$$
$$ This location 7EEEEEEE is difficult to be used but
$$ it could be occupied!!!
$$
.dvalloc /b 0x7EEEEEEE 0x400
r @$t0 = 0x7EEEEEEE
eb 0x7EEEEEEE 50
bp user32!MessageBoxExW "r @$t1 = @eip; r @eax = poi(@esp + 0x8); r @eip = @$t0;g"
bp @$t0 + 0x6 ".echo <-- Text from MessageBox; r @$ip = @$t1;g"
.logopen /t /u MessageBox.txt
.printf /D "\nType <b>call kernel32!OutputDebugStringW</b> then press Enter key two times then 'g' command after it.\n"
a 0x7EEEEEEF
$$
$$ ATTENTION! Use .logclose after finishing the debugging session.
$$
$$ =========================
Note: Some of my previous scripts were updated! Whenever I do that I write a small comment about it explaining the update.