Enable per-user Microsoft Entra multifactor authentication to secure sign-in events
To secure user sign-in events in Microsoft Entra ID, you can require multifactor authentication. Enabling Microsoft Entra multifactor authentication using Conditional Access policies is the recommended approach to protect users. Conditional Access is a Microsoft Entra ID P1 or P2 feature that lets you apply rules to require MFA as needed in certain scenarios. To get started using Conditional Access, see Tutorial: Secure user sign-in events with Microsoft Entra multifactor authentication.
For Microsoft Entra ID Free tenants without Conditional Access, you can use security defaults to protect users. Users are prompted for MFA as needed, but you can't define your own rules to control the behavior.
If needed, you can instead enable each account for per-user Microsoft Entra multifactor authentication. When users are enabled individually, they perform multifactor authentication each time they sign in (with some exceptions, such as when they sign in from trusted IP addresses or when the remember MFA on trusted devices feature is turned on).
Changing user states isn't recommended unless your Microsoft Entra ID licenses don't include Conditional Access and you don't want to use security defaults. For more information on the different ways to enable MFA, see Features and licenses for Microsoft Entra multifactor authentication.
Important
This article details how to view and change the status for per-user Microsoft Entra multifactor authentication. If you use Conditional Access or security defaults, you don't review or enable user accounts using these steps.
Enabling Microsoft Entra multifactor authentication through a Conditional Access policy doesn't change the state of the user. Don't be alarmed if users appear disabled. Conditional Access doesn't change the state.
Don't enable or enforce per-user Microsoft Entra multifactor authentication if you use Conditional Access policies.
Microsoft Entra multifactor authentication user states
A user's state reflects whether an admin has enrolled them in per-user Microsoft Entra multifactor authentication. User accounts in Microsoft Entra multifactor authentication have the following three distinct states:
| State | Description | Legacy authentication affected | Browser apps affected | Modern authentication affected |
|---|---|---|---|---|
| Disabled | The default state for a user not enrolled in per-user Microsoft Entra multifactor authentication. | No | No | No |
| Enabled | The user is enrolled in per-user Microsoft Entra multifactor authentication, but can still use their password for legacy authentication. If the user hasn't yet registered MFA authentication methods, they receive a prompt to register the next time they sign in using modern authentication (such as via a web browser). | No. Legacy authentication continues to work until the registration process is completed. | Yes. After the session expires, Microsoft Entra multifactor authentication registration is required. | Yes. After the access token expires, Microsoft Entra multifactor authentication registration is required. |
| Enforced | The user is enrolled per-user in Microsoft Entra multifactor authentication. If the user hasn't yet registered authentication methods, they receive a prompt to register the next time they sign in using modern authentication (such as via a web browser). Users who complete registration while in the Enabled state are automatically moved to the Enforced state. | Yes. Apps require app passwords. | Yes. Microsoft Entra multifactor authentication is required at sign-in. | Yes. Microsoft Entra multifactor authentication is required at sign-in. |
All users start out Disabled. When you enroll users in per-user Microsoft Entra multifactor authentication, their state changes to Enabled. When enabled users sign in and complete the registration process, their state changes to Enforced. Administrators may move users between states, including from Enforced to Enabled or Disabled.
Note
If per-user MFA is re-enabled on a user and the user doesn't re-register, their MFA state doesn't transition from Enabled to Enforced in MFA management UI. The administrator must move the user directly to Enforced.
View the status for a user
Tip
Steps in this article might vary slightly based on the portal you start from.
To view and manage user states, complete the following steps:
- Sign in to the Microsoft Entra admin center as at least an Authentication Administrator.
- Browse to Identity > Users > All users.
- Select Per-user MFA.
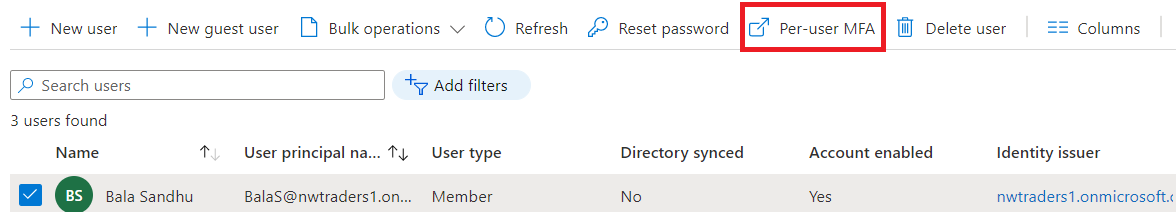
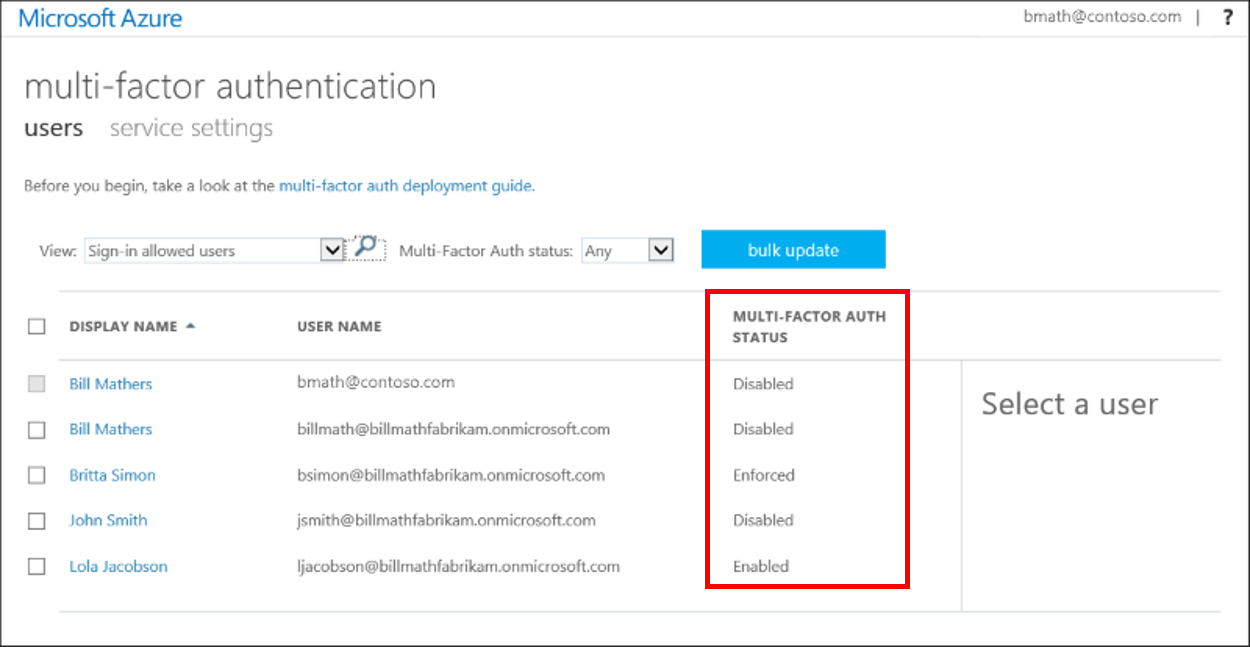
- A new page opens that displays the user state, as shown in the following example.
Change the status for a user
To change the per-user Microsoft Entra multifactor authentication state for a user, complete the following steps:
Use the previous steps to view the status for a user to get to the Microsoft Entra multifactor authentication users page.
Find the user you want to enable for per-user Microsoft Entra multifactor authentication. You might need to change the view at the top to users.
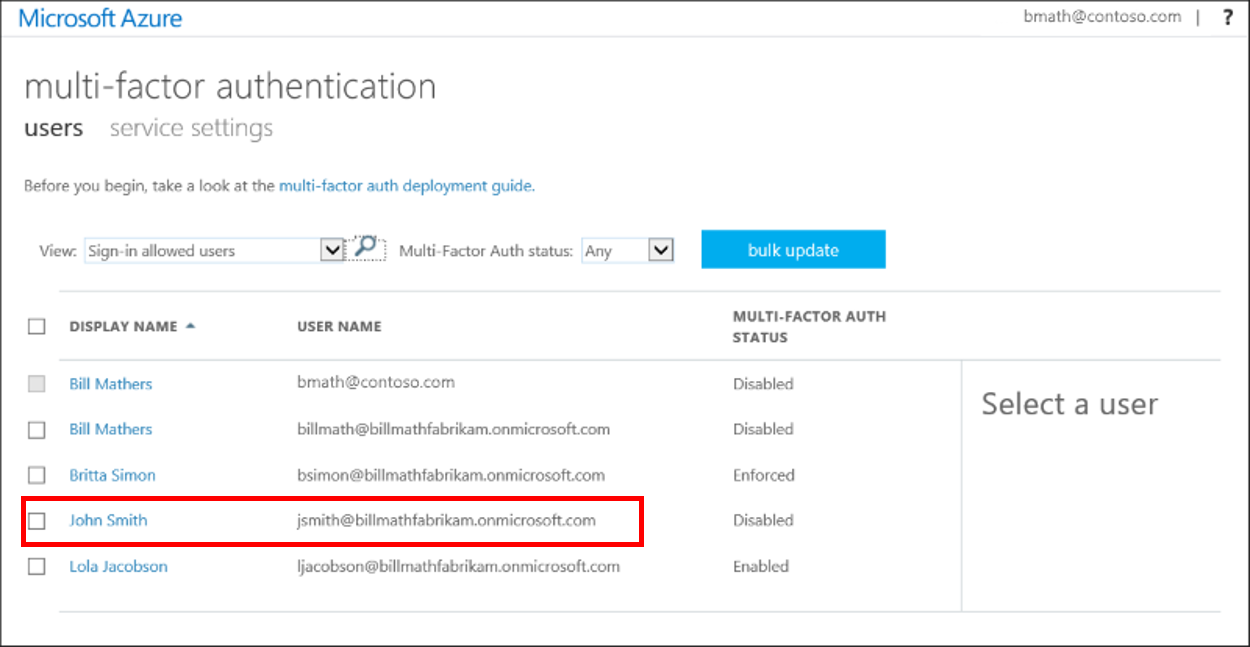
Check the box next to the name(s) of the user(s) to change the state for.
On the right-hand side, under quick steps, choose Enable or Disable. In the following example, the user John Smith has a check next to their name and is being enabled for use:
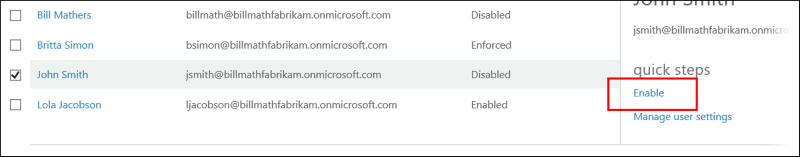
Tip
Enabled users are automatically switched to Enforced when they register for Microsoft Entra multifactor authentication. Don't manually change the user state to Enforced unless the user is already registered or if it is acceptable for the user to experience interruption in connections to legacy authentication protocols.
Confirm your selection in the pop-up window that opens.
After you enable users, notify them via email. Tell the users that a prompt is displayed to ask them to register the next time they sign in. Also, if your organization uses non-browser apps that don't support modern authentication, they need to create app passwords. For more information, see the Microsoft Entra multifactor authentication end-user guide to help them get started.
Next steps
To configure Microsoft Entra multifactor authentication settings, see Configure Microsoft Entra multifactor authentication settings.
To manage user settings for Microsoft Entra multifactor authentication, see Manage user settings with Microsoft Entra multifactor authentication.
To understand why a user was prompted or not prompted to perform MFA, see Microsoft Entra multifactor authentication reports.
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for