What is Azure Application Gateway?
Azure Application Gateway is a web traffic (OSI layer 7) load balancer that enables you to manage traffic to your web applications. Traditional load balancers operate at the transport layer (OSI layer 4 - TCP and UDP) and route traffic based on source IP address and port, to a destination IP address and port.
Application Gateway can make routing decisions based on additional attributes of an HTTP request, for example URI path or host headers. For example, you can route traffic based on the incoming URL. So if /images is in the incoming URL, you can route traffic to a specific set of servers (known as a pool) configured for images. If /video is in the URL, that traffic is routed to another pool that's optimized for videos.
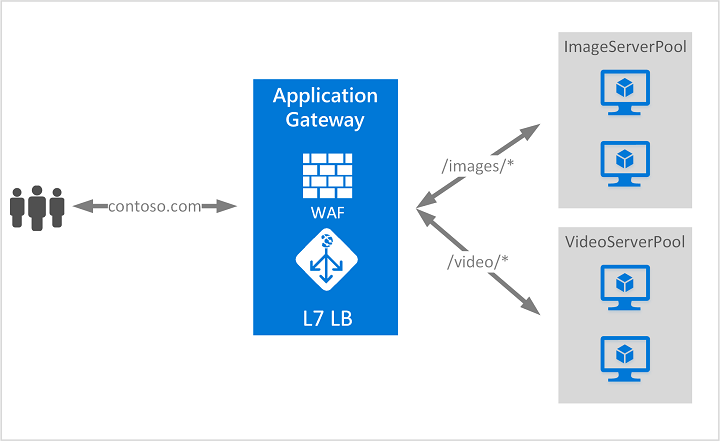
This type of routing is known as application layer (OSI layer 7) load balancing. Azure Application Gateway can do URL-based routing and more.
Note
Azure provides a suite of fully managed load-balancing solutions for your scenarios.
- If you're looking to do DNS based global routing and do not have requirements for Transport Layer Security (TLS) protocol termination ("SSL offload"), per-HTTP/HTTPS request or application-layer processing, review Traffic Manager.
- If you need to optimize global routing of your web traffic and optimize top-tier end-user performance and reliability through quick global failover, see Front Door.
- To do transport layer load balancing, review Load Balancer.
Your end-to-end scenarios may benefit from combining these solutions as needed. For an Azure load-balancing options comparison, see Overview of load-balancing options in Azure.
Features
To learn about Application Gateway features, see Azure Application Gateway features.
Infrastructure
To learn about Application Gateway infrastructure, see Azure Application Gateway infrastructure configuration.
Security
Protect your applications against L7 layer DDoS protection using WAF. For more information, see Application DDoS protection.
Protect your apps from malicious actors with Bot manager rules based on Microsoft’s own Threat Intelligence.
Secure applications against L3 and L4 DDoS attacks with Azure DDoS Protection plan.
Privately connect to your backend behind Application Gateway with Private Link and embrace a zero-trust access model.
Eliminate risk of data exfiltration and control privacy of communication from within the virtual network with a fully Private-only Application Gateway deployment.
Provide a centralized security experience for your application via Azure Policy, Azure Advisor, and Microsoft Sentinel integration that ensures consistent security features across apps.
Pricing and SLA
For Application Gateway pricing information, see Application Gateway pricing.
For Application Gateway SLA information, see Application Gateway SLA.
What's new
To learn what's new with Azure Application Gateway, see Azure updates.
Next steps
Depending on your requirements and environment, you can create a test Application Gateway using either the Azure portal, Azure PowerShell, or Azure CLI.
- Quickstart: Direct web traffic with Azure Application Gateway - Azure portal
- Quickstart: Direct web traffic with Azure Application Gateway - Azure PowerShell
- Quickstart: Direct web traffic with Azure Application Gateway - Azure CLI
- Learn module: Introduction to Azure Application Gateway
- How an application gateway works
- Frequently asked questions about Azure Application Gateway
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for