Use deterministic outbound IPs
In this guide, learn how to activate deterministic outbound IP support used by Azure Managed Grafana to communicate with data sources, disable public access and set up a firewall rule to allow inbound requests from your Grafana instance.
Note
The deterministic outbound IPs feature is only accessible for customers with a Standard plan. For more information about plans, go to pricing plans.
Prerequisites
- An Azure account with an active subscription. Create an account for free.
- A data source. For example, an Azure Data Explorer database.
Enable deterministic outbound IPs
Deterministic outbound IP support is disabled by default in Azure Managed Grafana. You can enable this feature during the creation of the instance, or you can activate it on an existing instance.
Create an Azure Managed Grafana workspace with deterministic outbound IPs enabled
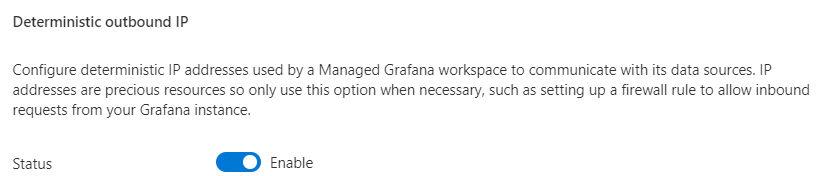
When creating an instance, select the Standard pricing plan and then in the Advanced tab, set Deterministic outbound IP to Enable.
For more information about creating a new instance, go to Quickstart: Create an Azure Managed Grafana instance.
Activate deterministic outbound IPs on an existing Azure Managed Grafana instance
In the Azure portal, under Settings select Configuration, and then under General settings > Deterministic outbound IP, select Enable.
Select Save to confirm the activation of deterministic outbound IP addresses.
Select Refresh to display the list of IP addresses under Static IP address.
Disable public access to a data source and allow Azure Managed Grafana IP addresses
This example demonstrates how to disable public access to Azure Data Explorer and set up private endpoints. This process is similar for other Azure data sources.
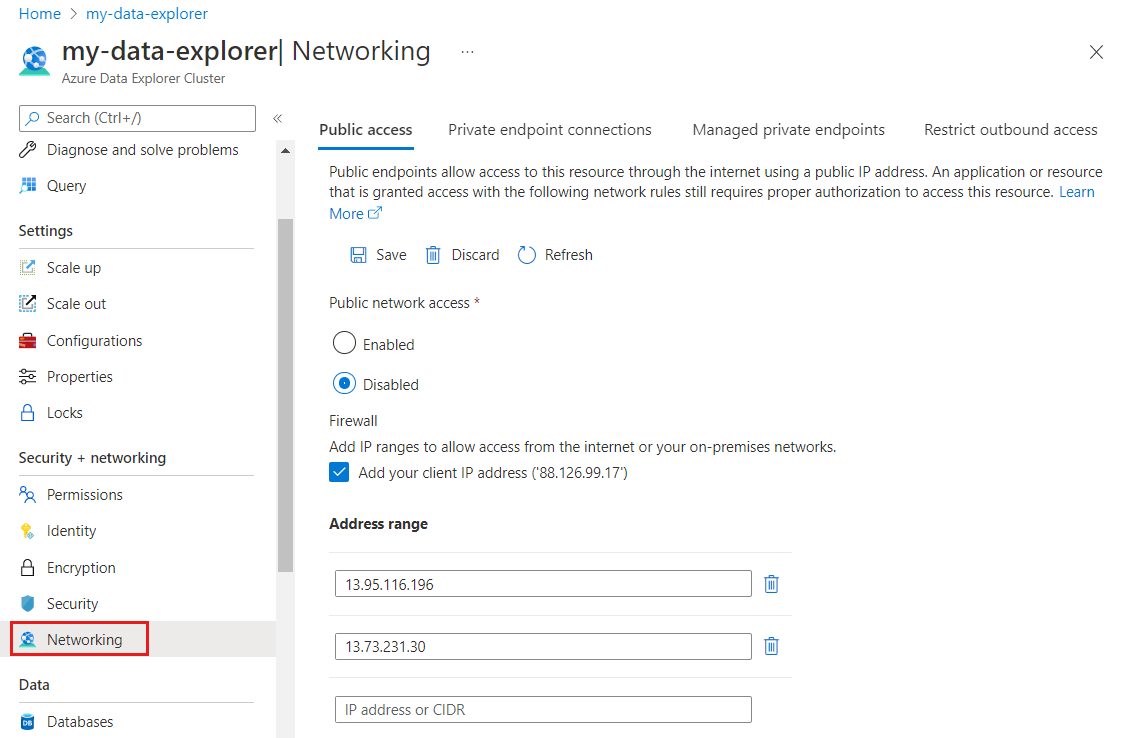
Open an Azure Data Explorer Cluster instance in the Azure portal, and under Settings, select Networking.
In the Public Access tab, select Disabled to disable public access to the data source.
Under Firewall, check the box Add your client IP address ('88.126.99.17') and under Address range, enter the IP addresses found in your Azure Managed Grafana workspace.
Select Save to finish adding the Azure Managed Grafana outbound IP addresses to the allowlist.
You have limited access to your data source by disabling public access, activating a firewall and allowing access from Azure Managed Grafana IP addresses.
Check access to the data source
Check if the Azure Managed Grafana endpoint can still access your data source.
In the Azure portal, go to your instance's Overview page and select the Endpoint URL.
Go to Configuration > Data Source > Azure Data Explorer Datasource > Settings and at the bottom of the page, select Save & test:
- If the message "Success" is displayed, Azure Managed Grafana can access your data source.
- If the following error message is displayed, Azure Managed Grafana can't access the data source:
Post "https://<Azure-Data-Explorer-URI>/v1/rest/query": dial tcp 13.90.24.175:443: i/o timeout. Make sure that you've entered the IP addresses correctly in the data source firewall allowlist.
Next steps
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for