Tutorial: Load balance multiple IP configurations using the Azure portal
To host multiple websites, you can use another network interface associated with a virtual machine. Azure Load Balancer supports deployment of load-balancing to support the high availability of the websites.
In this tutorial, you learn how to:
- Create and configure a virtual network, subnet, and NAT gateway.
- Create two Windows server virtual machines
- Create a secondary NIC and network configurations for each virtual machine
- Create two Internet Information Server (IIS) websites on each virtual machine
- Bind the websites to the network configurations
- Create and configure an Azure Load Balancer
- Test the load balancer
Prerequisites
- An Azure account with an active subscription. Create an account for free.
Create a virtual network and bastion host
In this section, you create a virtual network with a resource subnet, an Azure Bastion subnet, and an Azure Bastion host.
Important
Hourly pricing starts from the moment that Bastion is deployed, regardless of outbound data usage. For more information, see Pricing and SKUs. If you're deploying Bastion as part of a tutorial or test, we recommend that you delete this resource after you finish using it.
In the portal, search for and select Virtual networks.
On the Virtual networks page, select + Create.
On the Basics tab of Create virtual network, enter or select the following information:
Setting Value Project details Subscription Select your subscription. Resource group Select Create new.
Enter load-balancer-rg in Name.
Select OK.Instance details Name Enter lb-vnet. Region Select East US. 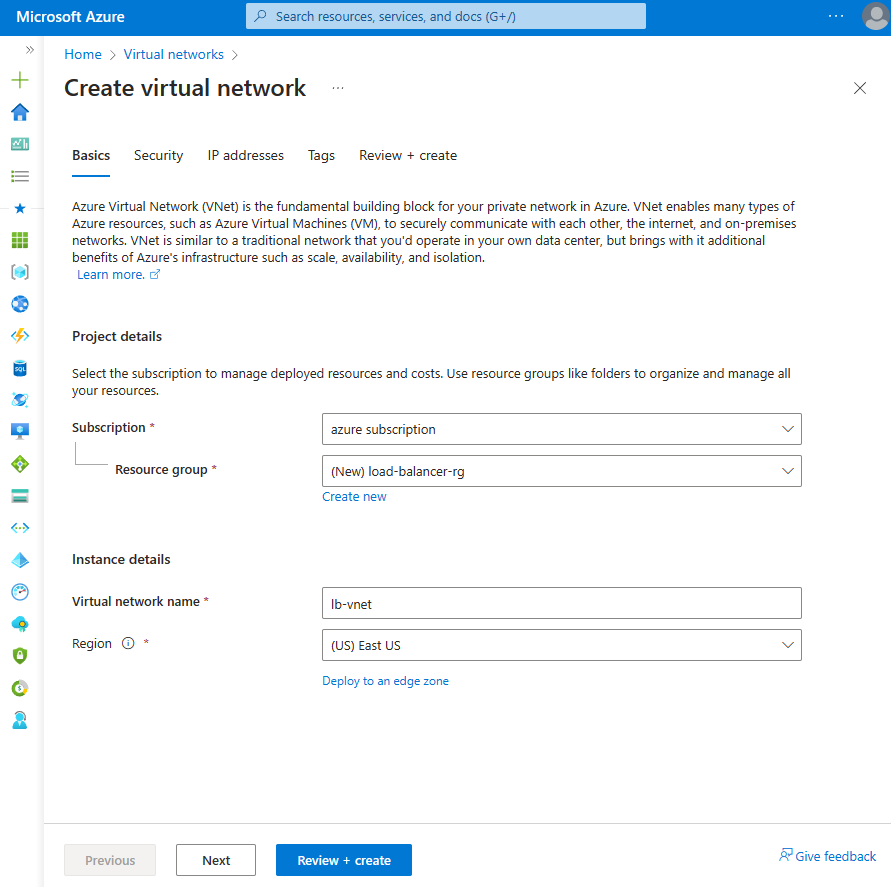
Select the Security tab or Next button at the bottom of the page.
Under Azure Bastion, enter or select the following information:
Setting Value Azure Bastion Enable Azure Bastion Select checkbox. Azure Bastion host name Enter lb-bastion. Azure Bastion public IP address Select Create new.
Enter lb-bastion-ip in Name.
Select OK.Select the IP addresses tab, or Next at the bottom of the page.
On Create virtual network page, enter or select the following information:
Setting Value Add IPv4 address space IPv4 address space Enter 10.0.0.0/16 (65,356 addresses). Subnets Select the default subnet link to edit. Subnet template Leave the default Default. Name Enter backend-subnet. Starting address Enter 10.0.0.0. Subnet size Enter /24(256 addresses). Security NAT Gateway Select lb-nat-gateway. 
Select Save.
Select Review + create at the bottom of the screen, and when validation passes, select Create.
Important
Hourly pricing starts from the moment that Bastion is deployed, regardless of outbound data usage. For more information, see Pricing and SKUs. If you're deploying Bastion as part of a tutorial or test, we recommend that you delete this resource after you finish using it.
Create NAT gateway
In this section, you'll create a NAT gateway for outbound internet access for resources in the virtual network. For other options for outbound rules, check out Network Address Translation (SNAT) for outbound connections
Sign in to the Azure portal.
In the search box at the top of the portal, enter NAT gateway. Select NAT gateways in the search results.
Select + Create.
In the Basics tab of Create network address translation (NAT) gateway enter or select the following information:
Setting Value Project details Subscription Select your subscription. Resource group Select Create new.
Enter load-balancer-rg in Name.
Select OK.Instance details NAT gateway name Enter lb-nat-gateway. Region Select East US. Availability zone Select None. Idle timeout (minutes) Enter 15. 
Select the Outbound IP tab or select the Next: Outbound IP button at the bottom of the page.
Select Create a new public IP address under Public IP addresses.
Enter nat-gw-public-ip in Name in Add a public IP address.
Select OK.
Select the blue Review + create button at the bottom of the page, or select the Review + create tab.
Select Create.
Create virtual machines
In this section, you create two virtual machines to host the IIS websites.
In the search box at the top of the portal, enter Virtual machine. Select Virtual machines in the search results.
In Virtual machines, select + Create then Azure virtual machine.
In Create virtual machine, enter or select the following information:
Setting Value Project Details Subscription Select your Azure subscription Resource Group Select load-balancer-rg Instance details Virtual machine name Enter myVM1 Region Select (US) East US Availability Options Select Availability zones Availability zone Select 1 Security type Leave the default of Standard. Image Select Windows Server 2022 Datacenter - Gen2 Size Choose VM size or take default setting Administrator account Username Enter a username Password Enter a password Confirm password Reenter password Inbound port rules Public inbound ports Select None Select the Networking tab, or select Next: Disks, then Next: Networking.
In the Networking tab, select or enter:
Setting Value Network interface Virtual network Select myVNet. Subnet Select backend-subnet(10.1.0.0/24) Public IP Select None. NIC network security group Select Advanced Configure network security group Select Create new.
In Create network security group, enter myNSG in Name.
In Inbound rules, select +Add an inbound rule.
In Service, select HTTP.
In Priority, enter 100.
In Name, enter myNSGrule
Select Add
Select OKSelect Review + create.
Review the settings, and then select Create.
Follow the steps 1 to 7 to create another VM with the following values and all the other settings the same as myVM1:
Setting VM 2 Name myVM2 Availability zone 2 Network security group Select the existing myNSG
Note
Azure provides a default outbound access IP for VMs that either aren't assigned a public IP address or are in the backend pool of an internal basic Azure load balancer. The default outbound access IP mechanism provides an outbound IP address that isn't configurable.
The default outbound access IP is disabled when one of the following events happens:
- A public IP address is assigned to the VM.
- The VM is placed in the backend pool of a standard load balancer, with or without outbound rules.
- An Azure NAT Gateway resource is assigned to the subnet of the VM.
VMs that you create by using virtual machine scale sets in flexible orchestration mode don't have default outbound access.
For more information about outbound connections in Azure, see Default outbound access in Azure and Use Source Network Address Translation (SNAT) for outbound connections.
Create secondary network configurations
In this section, you change the private IP address of the existing NIC of each virtual machine to Static. Next, you add a new NIC resource to each virtual machine with a Static private IP address configuration.
For more information on configuring floating IP in the virtual machine configuration, see Floating IP Guest OS configuration.
In the search box at the top of the portal, enter Virtual machine. Select Virtual machines in the search results.
Select myVM1.
Stop the virtual machine if it's running.
Select Networking in Settings.
In Networking, select the name of the network interface next to Network interface. The network interface begins with the name of the VM and has a random number assigned. In this example, myVM1266.
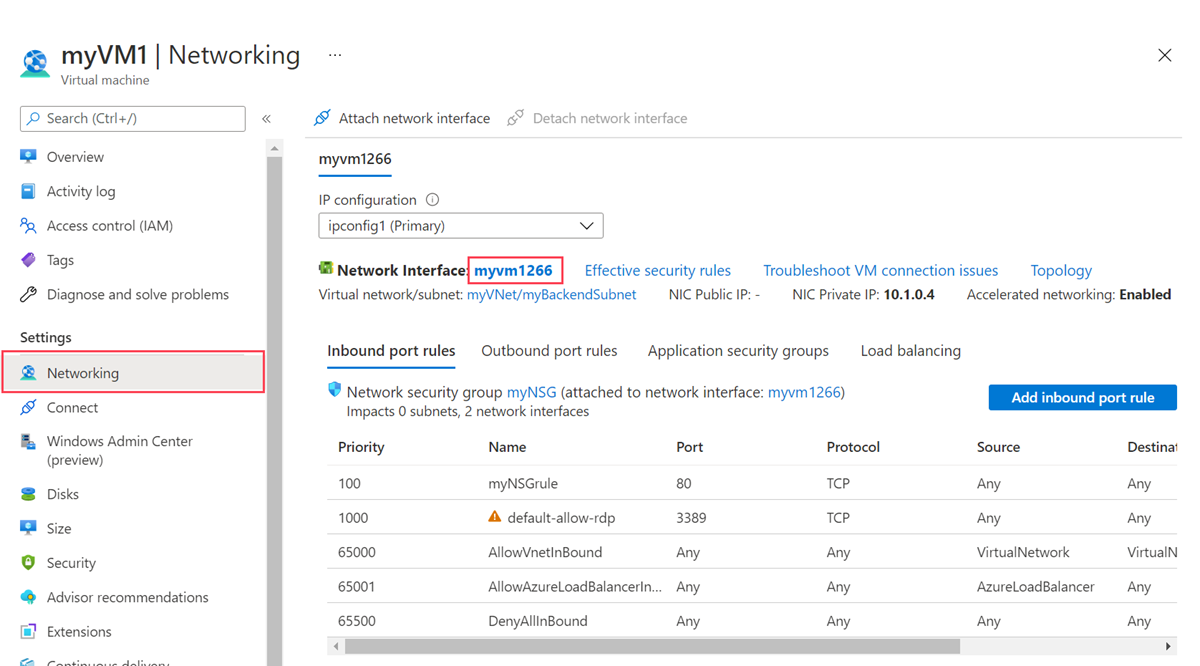
In the network interface page, select IP configurations in Settings.
In IP configurations, select ipconfig1.
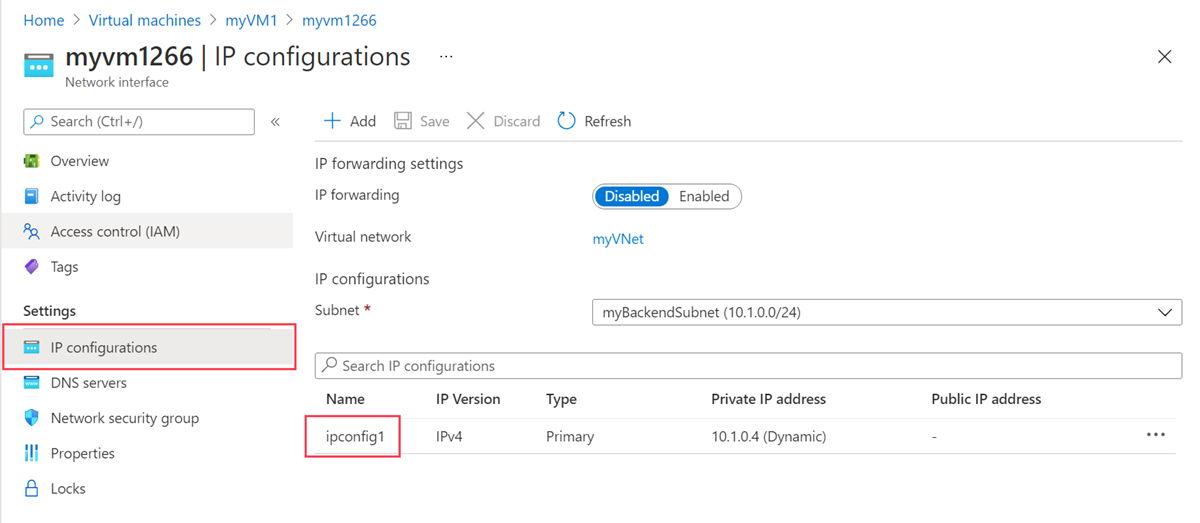
Select Static in Assignment in the ipconfig1 configuration.
Select Save.
Return to the Overview page of myVM1.
Select Networking in Settings.
In the Networking page, select Attach network interface.
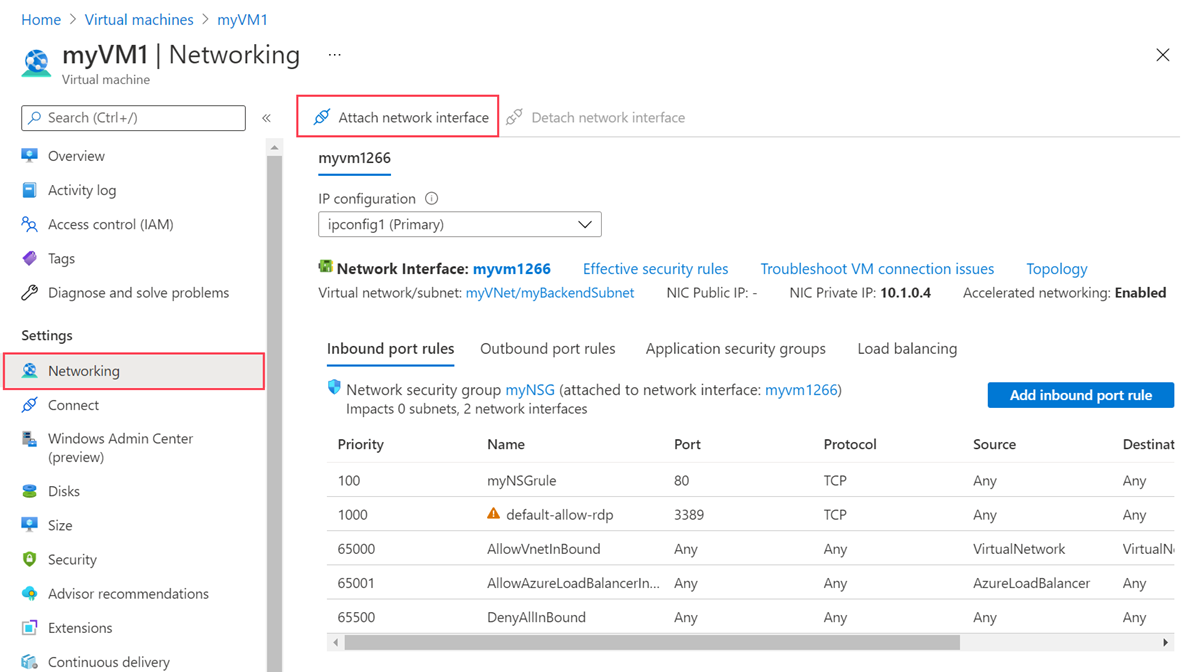
In Attach network interface, select Create and attach network interface.
In Create network interface, enter or select the following information:
Setting Value Project details Resource group Select load-balancer-rg. Network interface Name Enter myVM1NIC2 Subnet Select backend-subnet (10.1.0.0/24). NIC network security group Select Advanced. Configure network security group Select myNSG. Private IP address assignment Select Static. Private IP address Enter 10.1.0.6. Select Create.
Start the virtual machine.
Repeat steps 1 through 16 for myVM2, replacing the following information:
Setting myVM2 Name myVM2NIC2 Private IP address 10.1.0.7
Configure virtual machines
You connect to myVM1 and myVM2 with Azure Bastion and configure the secondary network configuration in this section. You add a route for the gateway for the secondary network configuration. Then you install IIS on each virtual machine and customize the websites to display the hostname of the virtual machine.
In the search box at the top of the portal, enter Virtual machine. Select Virtual machines in the search results.
Select myVM1.
Start myVM1.
In Overview, select Connect then Bastion.
Enter the username and password you entered when you created the virtual machine.
Select Allow for Bastion to use the clipboard.
On the server desktop, navigate to Start > Windows Administrative Tools > Windows PowerShell > Windows PowerShell.
In the PowerShell window, execute the
route printcommand, which returns output similar to the following output for a virtual machine with two attached network interfaces:=========================================================================== Interface List 4...60 45 bd 9c c7 00 ......Microsoft Hyper-V Network Adapter 11...60 45 bd 8d 44 fa ......Microsoft Hyper-V Network Adapter #3 1...........................Software Loopback Interface 1 =========================================================================== IPv4 Route Table =========================================================================== Active Routes: Network Destination Netmask Gateway Interface Metric 0.0.0.0 0.0.0.0 10.1.0.1 10.1.0.4 10 10.1.0.0 255.255.255.0 On-link 10.1.0.4 266 10.1.0.0 255.255.255.0 On-link 10.1.0.6 266 10.1.0.4 255.255.255.255 On-link 10.1.0.4 266 10.1.0.6 255.255.255.255 On-link 10.1.0.6 266 10.1.0.255 255.255.255.255 On-link 10.1.0.4 266 10.1.0.255 255.255.255.255 On-link 10.1.0.6 266 127.0.0.0 255.0.0.0 On-link 127.0.0.1 331 127.0.0.1 255.255.255.255 On-link 127.0.0.1 331 127.255.255.255 255.255.255.255 On-link 127.0.0.1 331 168.63.129.16 255.255.255.255 10.1.0.1 10.1.0.4 11 169.254.169.254 255.255.255.255 10.1.0.1 10.1.0.4 11 224.0.0.0 240.0.0.0 On-link 127.0.0.1 331 224.0.0.0 240.0.0.0 On-link 10.1.0.4 266 224.0.0.0 240.0.0.0 On-link 10.1.0.6 266 255.255.255.255 255.255.255.255 On-link 127.0.0.1 331 255.255.255.255 255.255.255.255 On-link 10.1.0.4 266 255.255.255.255 255.255.255.255 On-link 10.1.0.6 266 =========================================================================== Persistent Routes: None IPv6 Route Table =========================================================================== Active Routes: If Metric Network Destination Gateway 1 331 ::1/128 On-link 4 266 fe80::/64 On-link 11 266 fe80::/64 On-link 11 266 fe80::382:8783:5d2:f71e/128 On-link 4 266 fe80::1575:ced8:3e94:f23a/128 On-link 1 331 ff00::/8 On-link 4 266 ff00::/8 On-link 11 266 ff00::/8 On-link =========================================================================== Persistent Routes: NoneIn this example, Microsoft Hyper-V Network Adapter #3 (interface 13) is the secondary network interface that doesn't have a default gateway assigned to it.
In the PowerShell window, execute the
ipconfig /allcommand to see which IP address is assigned to the secondary network interface. In this example, 10.1.0.6 is assigned to interface 13. No default gateway address is returned for the secondary network interface.Connection-specific DNS Suffix . : pbu0t5vjr3sevaritkncspakhd.ax.internal.cloudapp.net Description . . . . . . . . . . . : Microsoft Hyper-V Network Adapter #3 Physical Address. . . . . . . . . : 60-45-BD-A1-75-FB DHCP Enabled. . . . . . . . . . . : Yes Autoconfiguration Enabled . . . . : Yes Link-local IPv6 Address . . . . . : fe80::dfb3:b93e:3516:c5b6%12(Preferred) IPv4 Address. . . . . . . . . . . : 10.1.0.6(Preferred) Subnet Mask . . . . . . . . . . . : 255.255.255.0 Lease Obtained. . . . . . . . . . : Monday, December 12, 2022 7:42:31 PM Lease Expires . . . . . . . . . . : Friday, January 19, 2159 2:17:19 AM Default Gateway . . . . . . . . . : DHCP Server . . . . . . . . . . . : 168.63.129.16 DHCPv6 IAID . . . . . . . . . . . : 207635901 DHCPv6 Client DUID. . . . . . . . : 00-01-00-01-2B-28-C9-C0-60-45-BD-9B-ED-AE DNS Servers . . . . . . . . . . . : 168.63.129.16 NetBIOS over Tcpip. . . . . . . . : EnabledTo route all traffic for addresses outside the subnet to the gateway, execute the following command:
route -p add 0.0.0.0 MASK 0.0.0.0 10.1.0.1 METRIC 5015 IF 13In this example, 10.1.0.1 is the default gateway for the virtual network you created previously.
Execute the following commands or copy and paste the code into the PowerShell window to install and configure IIS and the test websites:
## Install IIS and the management tools. ## Install-WindowsFeature -Name Web-Server -IncludeManagementTools ## Set the binding for the Default website to 10.1.0.4:80. ## $para1 = @{ Name = 'Default Web Site' BindingInformation = '10.1.0.4:80:' Protocol = 'http' } New-IISSiteBinding @para1 ## Remove the default site binding. ## $para2 = @{ Name = 'Default Web Site' BindingInformation = '*:80:' } Remove-IISSiteBinding @para2 ## Remove the default htm file. ## Remove-Item c:\inetpub\wwwroot\iisstart.htm ## Add a new htm file that displays the Contoso website. ## $para3 = @{ Path = 'c:\inetpub\wwwroot\iisstart.htm' Value = $("Hello World from www.contoso.com" + "-" + $env:computername) } Add-Content @para3 ## Create folder to host website. ## $para4 = @{ Path = 'c:\inetpub\' Name = 'fabrikam' Type = 'directory' } New-Item @para4 ## Create a new website and site binding for the second IP address 10.1.0.6. ## $para5 = @{ Name = 'Fabrikam' PhysicalPath = 'c:\inetpub\fabrikam' BindingInformation = '10.1.0.6:80:' } New-IISSite @para5 ## Add a new htm file that displays the Fabrikam website. ## $para6 = @{ Path = 'C:\inetpub\fabrikam\iisstart.htm' Value = $("Hello World from www.fabrikam.com" + "-" + $env:computername) } Add-Content @para6Close the Bastion connection to myVM1.
Repeat steps 1 through 12 for myVM2. Use the following PowerShell code for myVM2 for the IIS install.
## Install IIS and the management tools. ## Install-WindowsFeature -Name Web-Server -IncludeManagementTools ## Set the binding for the Default website to 10.1.0.5:80. ## $para1 = @{ Name = 'Default Web Site' BindingInformation = '10.1.0.5:80:' Protocol = 'http' } New-IISSiteBinding @para1 ## Remove the default site binding. ## $para2 = @{ Name = 'Default Web Site' BindingInformation = '*:80:' } Remove-IISSiteBinding @para2 ## Remove the default htm file. ## Remove-Item C:\inetpub\wwwroot\iisstart.htm ## Add a new htm file that displays the Contoso website. ## $para3 = @{ Path = 'c:\inetpub\wwwroot\iisstart.htm' Value = $("Hello World from www.contoso.com" + "-" + $env:computername) } Add-Content @para3 ## Create folder to host website. ## $para4 = @{ Path = 'c:\inetpub\' Name = 'fabrikam' Type = 'directory' } New-Item @para4 ## Create a new website and site binding for the second IP address 10.1.0.7. ## $para5 = @{ Name = 'Fabrikam' PhysicalPath = 'c:\inetpub\fabrikam' BindingInformation = '10.1.0.7:80:' } New-IISSite @para5 ## Add a new htm file that displays the Fabrikam website. ## $para6 = @{ Path = 'C:\inetpub\fabrikam\iisstart.htm' Value = $("Hello World from www.fabrikam.com" + "-" + $env:computername) } Add-Content @para6
Create load balancer
You create a zone redundant load balancer that load balances virtual machines in this section.
With zone-redundancy, one or more availability zones can fail and the data path survives as long as one zone in the region remains healthy.
During the creation of the load balancer, you configure:
- Two frontend IP addresses, one for each website.
- Backend pools
- Inbound load-balancing rules
In the search box at the top of the portal, enter Load balancer. Select Load balancers in the search results.
In the Load balancer page, select Create.
In the Basics tab of the Create load balancer page, enter, or select the following information:
Setting Value Project details Subscription Select your subscription. Resource group Select load-balancer-rg. Instance details Name Enter myLoadBalancer Region Select East US. SKU Leave the default Standard. Type Select Public. Tier Leave the default Regional. Select Next: Frontend IP configuration.
In Frontend IP configuration, select + Add a frontend IP configuration.
Enter or select the following information in Add frontend IP configuration:
Setting Value Name Enter Frontend-contoso. IP version Select IPv4. IP type Select IP address. Public IP address Select Create new.
Enter myPublicIP-contoso for Name
Select Zone-redundant in Availability zone.
Leave the default of Microsoft Network for Routing preference.
Select OK.Note
IPv6 isn't currently supported with Routing Preference or Cross-region load-balancing (Global Tier).
For more information on IP prefixes, see Azure Public IP address prefix.
In regions with Availability Zones, you have the option to select no-zone (default option), a specific zone, or zone-redundant. The choice will depend on your specific domain failure requirements. In regions without Availability Zones, this field won't appear.
For more information on availability zones, see Availability zones overview.Select Add.
Select + Add a frontend IP configuration.
Enter or select the following information in Add frontend IP configuration:
Setting Value Name Enter Frontend-fabrikam. IP version Select IPv4. IP type Select IP address. Public IP address Select Create new.
Enter myPublicIP-fabrikam for Name
Select Zone-redundant in Availability zone.
Leave the default of Microsoft Network for Routing preference.
Select OK.Select Add.
Select Next: Backend pools.
In the Backend pools tab, select + Add a backend pool.
Enter or select the following information in Add a backend pool:
Setting Value Name Enter myBackendPool-contoso. Virtual network Select myVNet. Backend Pool Configuration Select NIC. In IP configurations, select + Add.
Select myVM1 and myVM2 that correspond with ipconfig1 (10.1.0.4) and ipconfig1 (10.1.0.5).
Select Add.
Select Save.
Select + Add a backend pool.
Enter or select the following information in Add a backend pool:
Setting Value Name Enter myBackendPool-fabrikam. Virtual network Select myVNet. Backend Pool Configuration Select NIC. In IP configurations, select + Add.
Select myVM1 and myVM2 that correspond with ipconfig1 (10.1.0.6) and ipconfig1 (10.1.0.7).
Select Add.
Select Save.
Select Next: Inbound rules.
In Load balancing rule in the Inbound rules tab, select + Add a load balancing rule.
In Add load balancing rule, enter or select the following information:
Setting Value Name Enter myHTTPRule-contoso IP Version Select IPv4. Frontend IP address Select Frontend-contoso. Backend pool Select myBackendPool-contoso. Protocol Select TCP. Port Enter 80. Backend port Enter 80. Health probe Select Create new.
In Name, enter myHealthProbe-contoso.
Select TCP in Protocol.
Leave the rest of the defaults, and select OK.Session persistence Select None. Idle timeout (minutes) Enter or select 15. TCP reset Select Enabled. Floating IP Select Disabled. Outbound source network address translation (SNAT) Leave the default of (Recommended) Use outbound rules to provide backend pool members access to the internet. Select Add.
Select Add a load balancing rule.
In Add load balancing rule, enter or select the following information:
Setting Value Name Enter myHTTPRule-fabrikam IP Version Select IPv4. Frontend IP address Select Frontend-fabrikam. Backend pool Select myBackendPool-fabrikam. Protocol Select TCP. Port Enter 80. Backend port Enter 80. Health probe Select Create new.
In Name, enter myHealthProbe-fabrikam.
Select TCP in Protocol.
Leave the rest of the defaults, and select OK.Session persistence Select None. Idle timeout (minutes) Enter or select 15. TCP reset Select Enabled. Floating IP Select Disabled. Outbound source network address translation (SNAT) Leave the default of (Recommended) Use outbound rules to provide backend pool members access to the internet. Select Add.
Select the blue Review + create button at the bottom of the page.
Select Create.
Note
In this example we created a NAT gateway to provide outbound Internet access. The outbound rules tab in the configuration is bypassed as it's optional isn't needed with the NAT gateway. For more information on Azure NAT gateway, see What is Azure Virtual Network NAT? For more information about outbound connections in Azure, see Source Network Address Translation (SNAT) for outbound connections
Test load balancer
In this section, you discover the public IP address for each website. You enter the IP into a browser to test the websites you created earlier.
In the search box at the top of the portal, enter Public IP. Select Public IP addresses in the search results.
Select myPublicIP-contoso.
Copy the IP address in the overview page of myPublicIP-contoso.
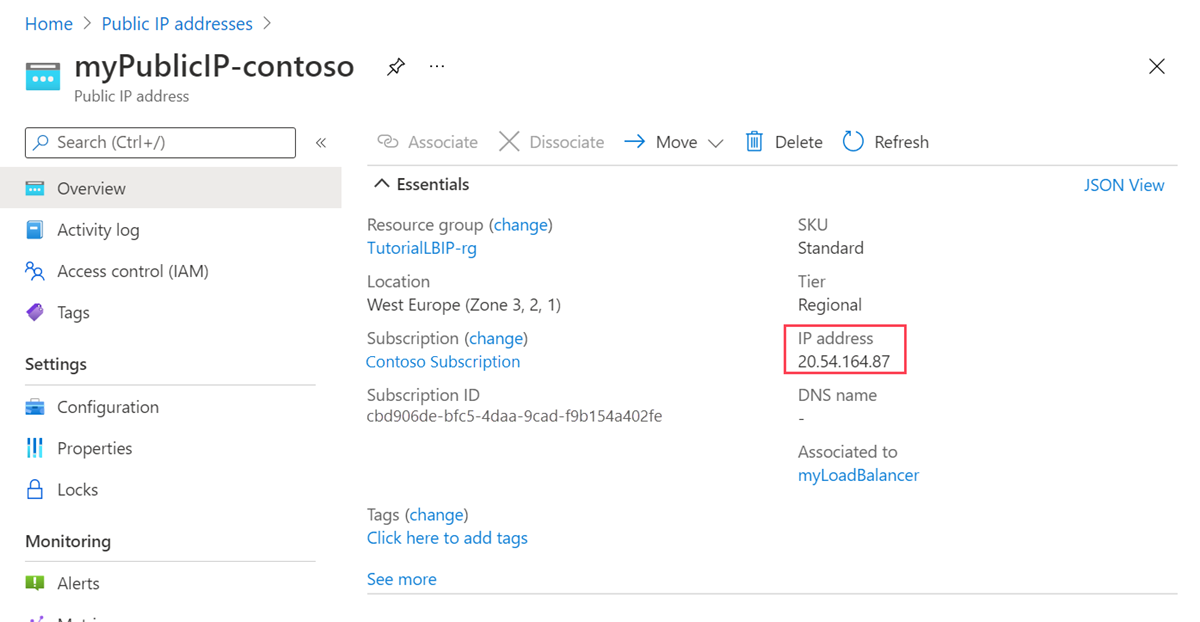
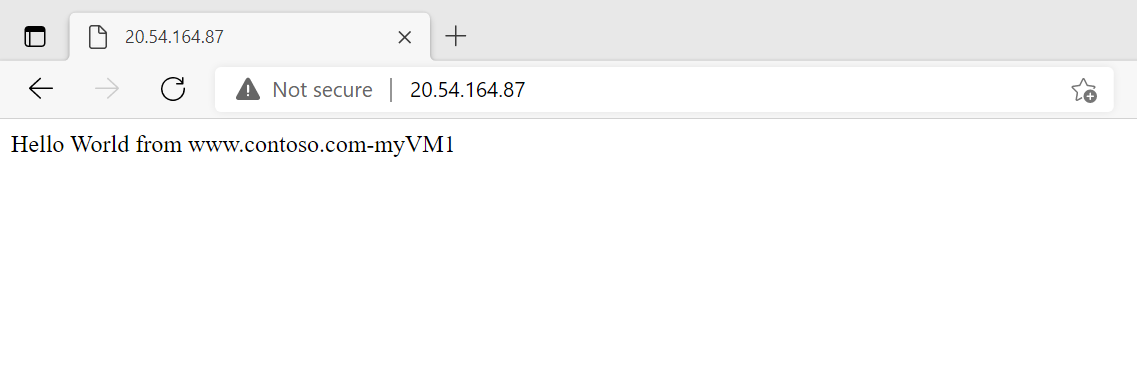
Open a web browser and paste the public IP address into the address bar.
Return to Public IP addresses. Select myPublicIP-fabrikam.
Copy the IP address in the overview page of myPublicIP-fabrikam.
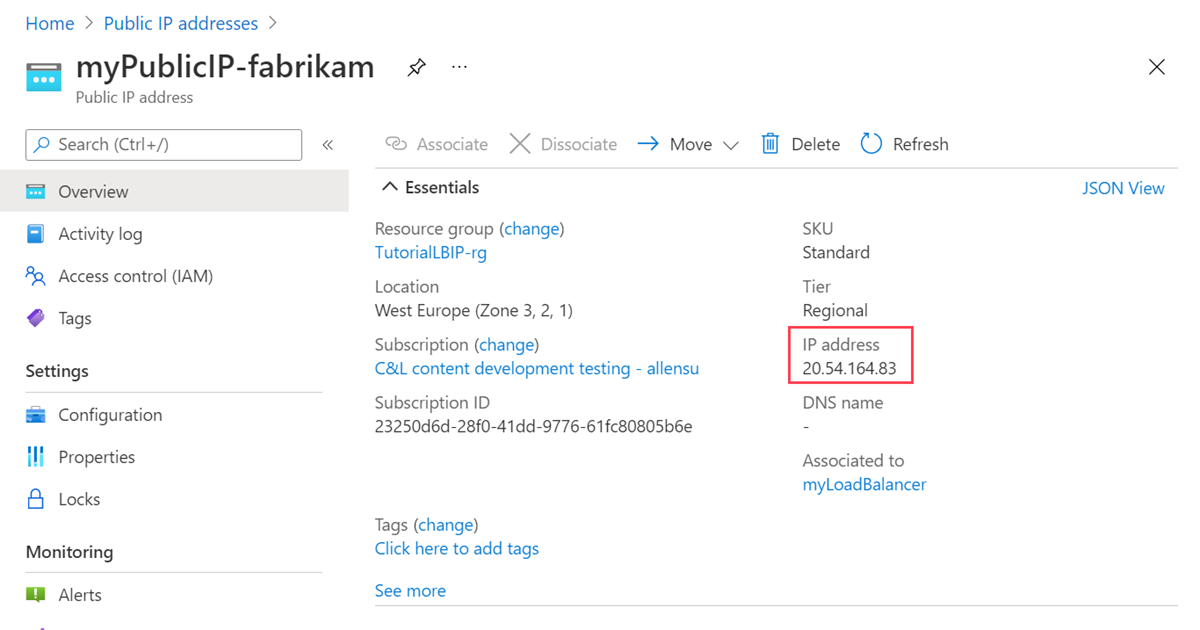
Open a web browser and paste the public IP address into the address bar.
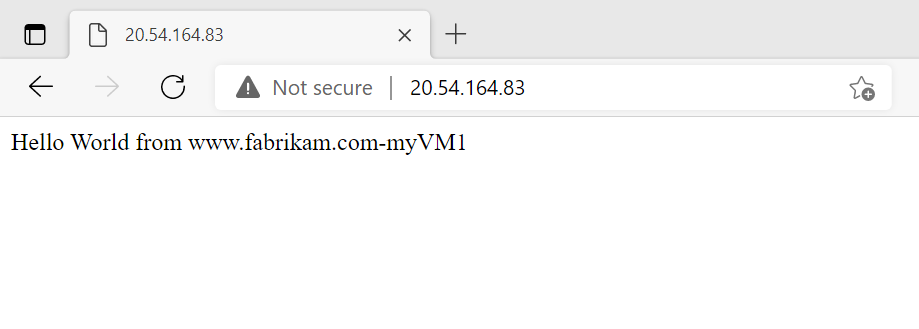
To test the load balancer, refresh the browser or shut down one of the virtual machines.
Clean up resources
If you're not going to continue to use this application, delete the virtual machines and load balancer with the following steps:
In the search box at the top of the portal, enter Resource group. Select Resource groups in the search results.
Select load-balancer-rg in Resource groups.
Select Delete resource group.
Enter load-balancer-rg in TYPE THE RESOURCE GROUP NAME:. Select Delete.
Next steps
Advance to the next article to learn how to create a cross-region load balancer:
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for