Ask Learn
PreviewPlease sign in to use this experience.
Sign inThis browser is no longer supported.
Upgrade to Microsoft Edge to take advantage of the latest features, security updates, and technical support.
Environments are containers that administrators can use to manage apps, flows, connections, and other assets, along with permissions to allow organization users controlled access to the environment and its resources.
Apps in Microsoft Power Apps and Microsoft Power Automate flows do not provide users with access to data assets that they don't already have access to. Users should only have access to data that they require access to.
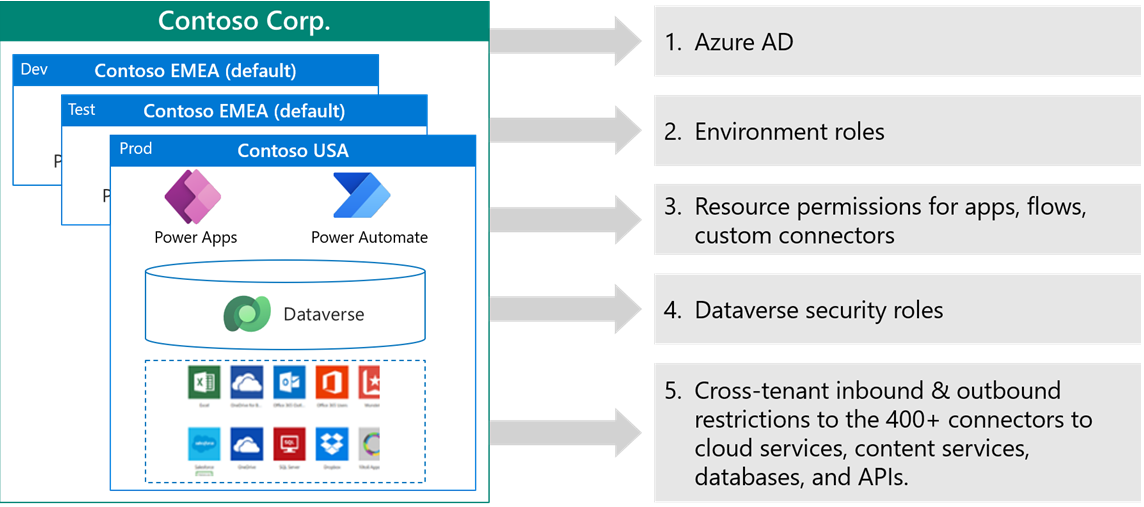
Access to environments is multilayered. Environments are contained within a Microsoft Entra ID tenant. Access to the environment is authenticated by Microsoft Entra ID. Users must have a user account in Microsoft Entra ID to access any environment, and they must have a license to use Microsoft Power Platform. To access an individual environment, the user will need a Microsoft 365 role if a Microsoft Dataverse database is not available, and they'll need a Dataverse security role if a Dataverse database is available. Users also need to be given permission on resources in an environment such as apps, flows, and connectors.
An administrator can also control access to environments from other Microsoft Entra ID tenants in business-to-business (B2B) scenarios.
Microsoft Power Platform uses Microsoft Entra ID to authenticate users.
Microsoft Entra ID has several features that Microsoft Power Platform can use:
Other features of Microsoft Entra ID that are not currently supported with Microsoft Power Platform:
An organization is likely to have chosen how it implements Microsoft Entra ID and a Microsoft Power Platform solution, and it is unlikely to change this fundamentally. However, Microsoft Power Platform might provide access to users who have never had IT app access previously, such as mobile frontline workers, business partners, and external contractors who don't have identities in Microsoft Entra ID. Therefore, you might need to consider Conditional access, B2B, and guest user access.
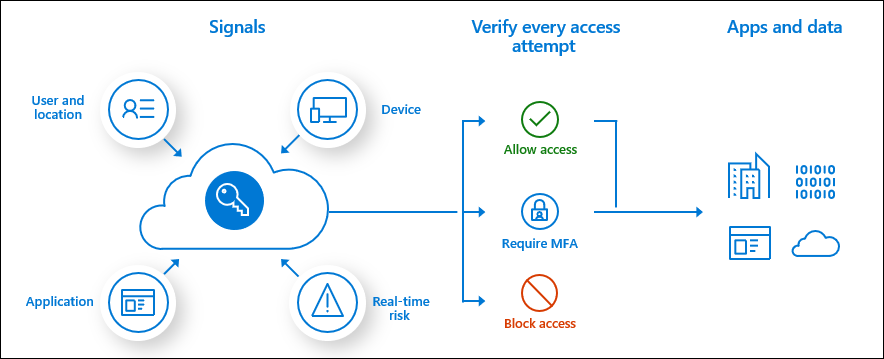
Conditional access requires a Microsoft Entra ID Premium license. Conditional access policies can grant or block access to apps and data based on the following factors:
Microsoft Azure Active Directory B2B (Microsoft Entra ID B2B) collaboration is a feature that lets you invite guest users to collaborate with your organization. You can assign licenses to guest users to run apps that are built with Microsoft Power Platform. Currently, guests can't create or edit Power Apps.
For more information, see Share a canvas app with guest users and About Power Apps per app plans.
In B2B collaboration scenarios, you can more securely share the apps and data in your tenant with a tenant from another source. In the default configuration, each tenant can access the other tenant's resources.
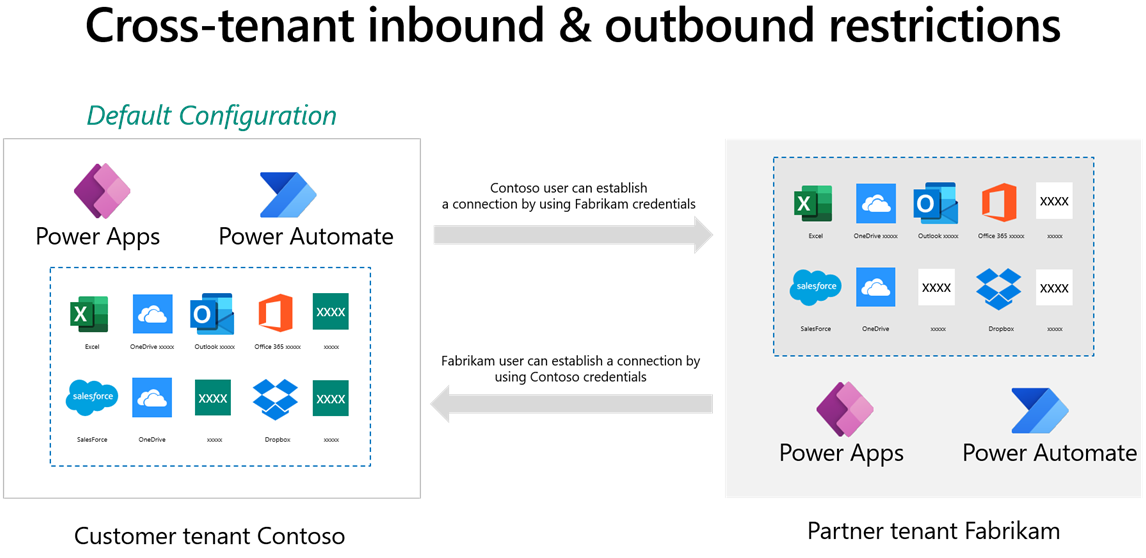
Microsoft Entra ID has a feature called tenant restrictions. With tenant restrictions, organizations can specify the list of tenants that their users are permitted to access. Microsoft Entra ID then only grants access to these permitted tenants. Cross-tenant isolation lets you restrict the other tenants that your users can connect to. Cross-tenant isolation blocks inbound or outbound connections for canvas apps and flows.
Restricting outbound connections means that a user in your tenant is blocked from connecting to a partner or external tenant. Restricting outbound cross-tenant connections can be done by using tenant restrictions that apply to all Microsoft Entra ID cloud apps that would block outbound connections for Power Apps and Power Automate flows.
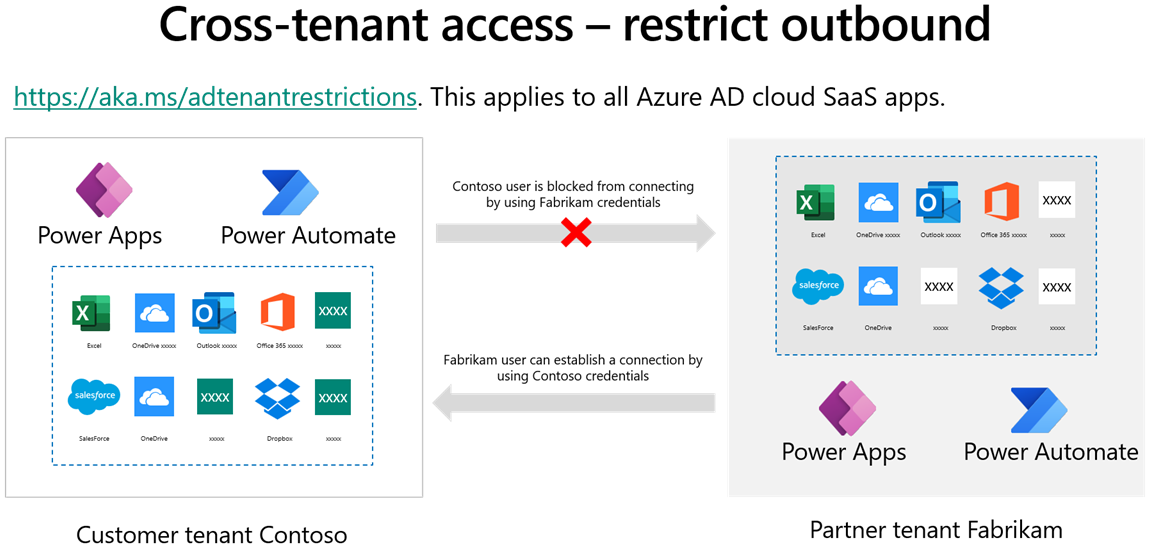
Restricting inbound connections means that a user in a partner or external tenant is blocked from creating a connection to your tenant.
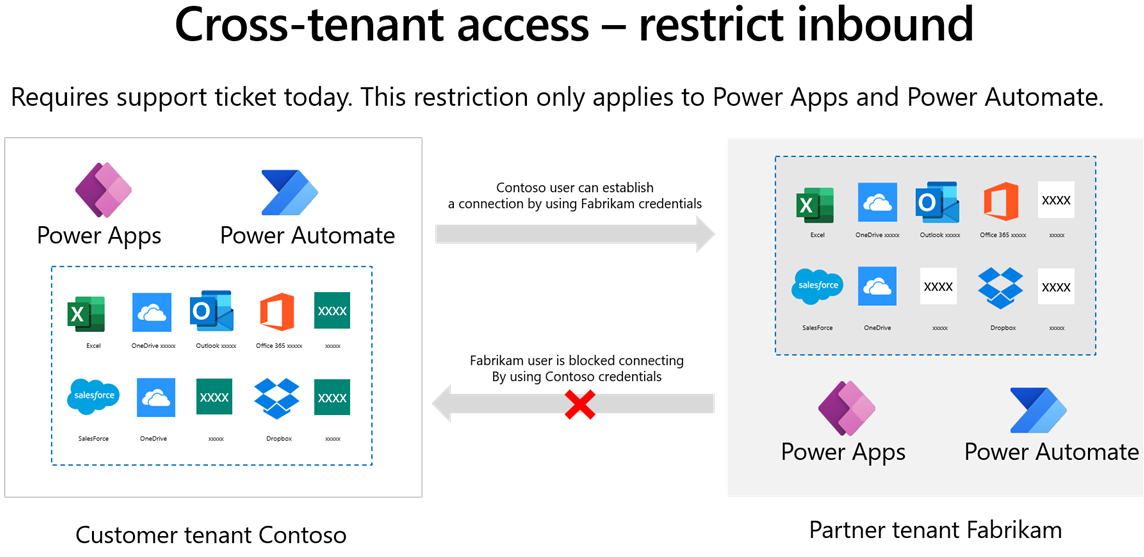
Important
Restricting inbound cross-tenant connections requires a support ticket. Then, this restriction will only apply to Power Apps and Power Automate flows.
By default, a user with a Power Apps license can potentially access all environments in a tenant, and you will be able to see all licensed users in the user table in an environment. Microsoft Entra ID security groups can be used to limit access to environments. This feature has the added advantage of keeping the user table streamlined to only the users of the environment.
A security group can be associated with an environment when the environment is created, or it can be linked to the environment. In the following screenshot, a security group for the developers has been associated with the development environment.

The previous screenshot shows that the following behavior is observed:
Note
Distribution groups and Microsoft Office 365 groups can't be associated with environments.
Managing environments and performing some administration activities requires one or more of these administrative roles:
Note
The Microsoft Dynamics 365 admin role is deprecated. A user with the Dynamics 365 admin role can create environments and manage environments, but only if the user belongs to the security group for that environment. A user with the Dynamics 365 admin role will have the System Administrator security role in those environments.
These roles are not the same as security roles in an environment. Non-administrative users can be assigned a role for an environment. The roles that are used differ, depending on whether the environment contains a Dataverse database or not.
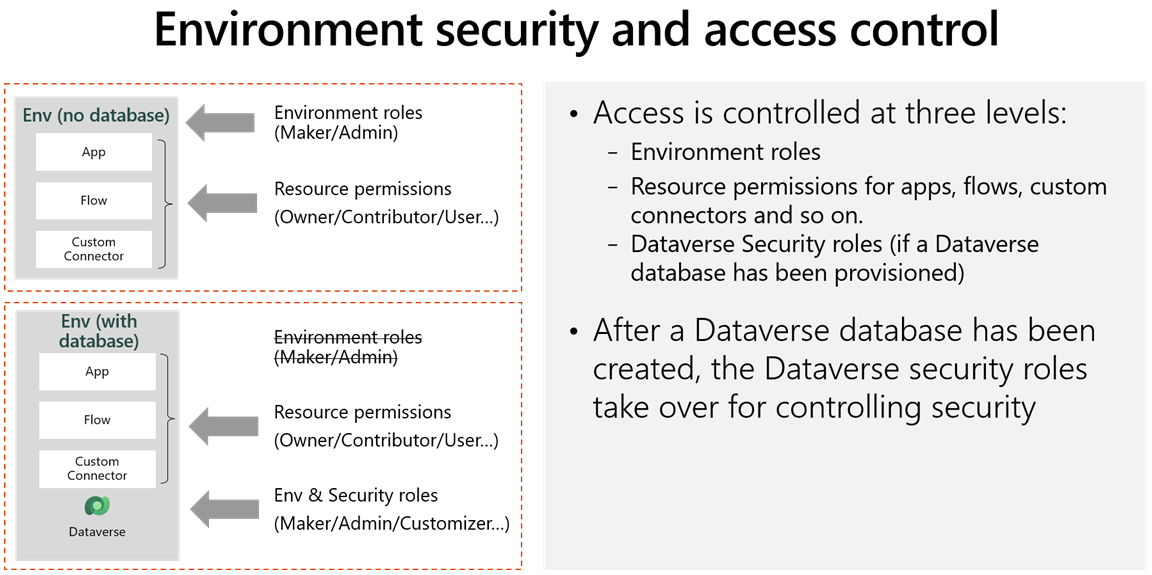
The Environment admin role is only used when a Dataverse database is not present. The Environment admin for a specific environment can allow the user with the role to add and remove users with the Environment Maker role. The Environment Maker role allows a user to create apps in that environment.
When a Dataverse database is added to the environment, a user with the Environment admin role is given the System Administrator security role in the Dataverse database, and a user with the Environment Maker role is given the Basic User security role.
Having an issue? We can help!
Please sign in to use this experience.
Sign in