個人用アクセス トークンを使用する
Azure DevOps Services | Azure DevOps Server 2022 - Azure DevOps Server 2019
個人用アクセス トークン (PAT) を代替パスワードとして使用して、Azure DevOps に対する認証を行うことができます。 この記事では、Azure DevOps の AT を作成、使用、変更、取り消す方法について説明します。
次のビデオでは、PAT を作成して使用する方法を示します。
PAT について
個人用アクセス トークンには、Azure DevOps のセキュリティ資格情報が含まれています。 PAT は、ユーザーとそのユーザーがアクセスできる組織、アクセスのスコープを識別します。 その意味でパスワードと変わらないほどの重要性があるため、同じように扱う必要があります。
Microsoft のツール内で作業している場合、Microsoft アカウント (MSA) または Microsoft Entra ID は、その条件を満たしており、十分に信頼できるアプローチです。 ただし、Microsoft アカウントも Microsoft Entra アカウントもサポートしないサードパーティのツールを使用している場合、つまり、主要な資格情報をツールに与えたくない場合は、PAT を使用してリスクを制限してください。
PAT の作成と管理は、次のいずれかの方法で行えます。
Microsoft 以外のツール用に PAT を設定するには、Git 資格情報マネージャーを使用するか、手動で作成します。 正しい認証メカニズムの選択に役立つ認証ガイダンスを確認することをお勧めします。 プロジェクトの規模が比較的小さく、ソリューションに堅牢性がさほど求められなければ、PAT で手軽に代用できます。 ユーザーは、資格情報マネージャーを使用していない限り、毎回資格情報を入力する必要があります。
PAT の作成
組織にサインインします (
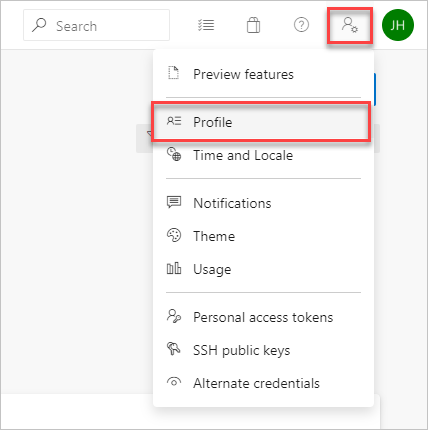
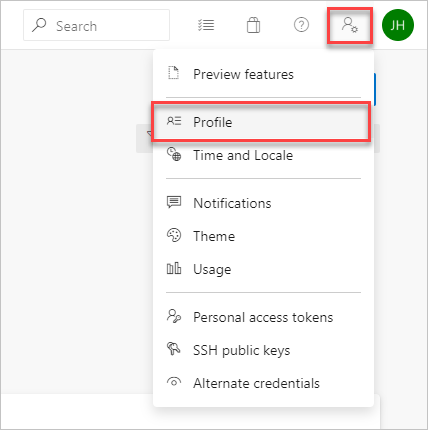
https://dev.azure.com/{yourorganization})。ホーム ページからユーザー設定
 を開き、[個人用アクセス トークン] を選択します。
を開き、[個人用アクセス トークン] を選択します。![選択した [個人用アクセス トークン] を示すスクリーンショット。](../../repos/git/media/select-personal-access-tokens.jpg?view=azure-devops)
[+ New Token] を選択します。
![選択した [新しいトークン] を示すスクリーンショット。](../../repos/git/media/select-new-token.png?view=azure-devops)
トークンに名前を付け、トークンを使用する組織を選択し、設定した日数後にトークンの有効期限が自動的に切れるよう設定します。
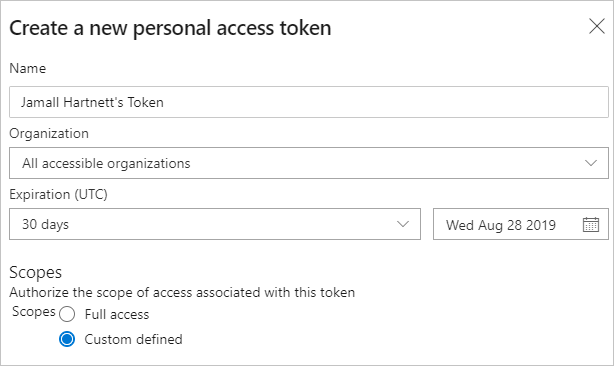
このトークンのスコープを選択して、特定のタスクを承認します。
たとえば、ビルド エージェントとリリース エージェントが Azure DevOps Services に対して認証できるようにするトークンを作成するには、トークンのスコープをエージェント プール (読み取りおよび管理) に制限します。 監査ログ イベントを読み取り、ストリームを管理および削除するには、[監査ログの読み取り] を選択し、[作成] を選択します。

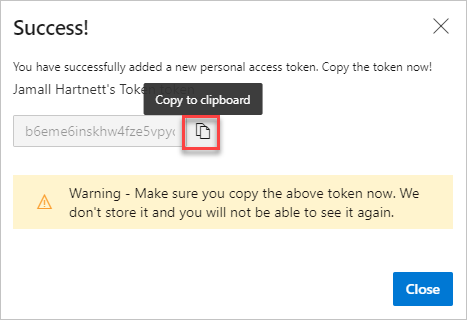
完了したら、トークンをコピーし、安全な場所に格納します。 セキュリティ上、再び表示されることはありません。
警告
パスワードのように PAT を扱って使用し、秘密のままにしておいてください。
Azure DevOps での認証にユーザー資格情報が必要な任意の場所で PAT を使用します。
重要
Microsoft Entra ID によってサポートされている組織の場合、新しい PAT を使用してサインインするまで 90 日が必要です。それ以外の場合は非アクティブと見なされます。 詳細については、「条件付きアクセスのユーザー サインイン頻度」を参照してください。
通知
ユーザーは PAT の有効期間中に 2 つの通知を受け取ります。1 つは作成時に、もう 1 つは有効期限の 7 日前です。
PAT を作成すると、次の例のような通知が表示されます。 この通知は、PAT が組織に追加されたことを確認します。

次の図は、PAT の有効期限が切れる前の 7 日間の通知の例を示しています。

詳細については、「SMTP サーバーを構成し、アラートとフィードバック要求の電子メールをカスタマイズする」を参照してください。
予期しない通知
予期しない PAT 通知を受け取った場合、管理者またはツールがユーザーに代わって PAT を作成している可能性があります。 次の例を参照してください。
- git.exeを使用して Azure DevOps Git リポジトリに接続する場合。 "git:
https://MyOrganization.visualstudio.com/on MyMachine" のような表示名を持つトークンが作成されます。 - ユーザーまたは管理者が Azure アプリ Service Web アプリのデプロイを設定すると、"Service Hooks: : Azure アプリ Service: : Deploy Web app" のような表示名のトークンが作成されます。
- 自分または管理者がパイプラインの一部として Web ロード テストを設定すると、"WebAppLoadTestCDIntToken" のような表示名を持つトークンが作成されます。
- Microsoft Teams 統合メッセージング拡張機能を設定すると、"Microsoft Teams 統合" のような表示名を持つトークンが作成されます。
警告
PAT がエラーで存在すると思われる場合は、PAT を取り消すことが推奨されます。 次に、パスワードを変更します。 Microsoft Entra ユーザーとして、管理者とチェックして、組織が不明なソースまたは場所から使用されたかどうかを確認します。 パブリック GitHub リポジトリへの PAT の誤チェックに関する FAQ も参照してください。
PAT を使用する
PAT は自分の ID であり、パスワードと同様に、それを使用するときにユーザーを表します。
Git
Git の操作にはユーザー名が必要です。これは空の文字列以外の任意のユーザー名です。
HTTP 基本認証で PAT を使用するには、次のコード ブロックに含まれる for を使用Base64-encode$MyPatします。
PowerShell で、次のコードを入力します。
$MyPat = 'yourPat'
$headerValue = "Authorization: Basic " + [Convert]::ToBase64String([System.Text.Encoding]::UTF8.GetBytes(":" + $MyPat))
$env:GIT_AUTH_HEADER = $headerValue
git --config-env=http.extraheader=GIT_AUTH_HEADER clone https://dev.azure.com/yourOrgName/yourProjectName/_git/yourRepoName
トークンの安全性を高めるために、資格情報マネージャーを使用して、毎回資格情報を入力する必要がないようにします。 Git Credential Manager をお勧めします。 Windows 用の Git が必要です。
既存のリポジトリ
既存のリポジトリの場合、ユーザー名を使用して配信元を既に追加している場合は、最初に次のコマンドを実行します。
git remote remove origin
それ以外の場合は、次のコマンドを実行します。
git remote add origin https://<PAT>@<company_machineName>.visualstudio.com:/<path-to-git-repo> path to git repo = <project name>/_git/<repo_name> git push -u origin --all
コードで PAT を使用する
コードで PAT を使用できます。
HTTP ヘッダーを介して PAT を指定する場合は、まずそれを Base64 文字列に変換します。 次の例は、C# を使用して Base64 に変換する方法を示しています。
Authorization: Basic BASE64_USERNAME_PAT_STRING
結果の文字列は、次の形式で HTTP ヘッダーとして指定できます。
次の例では、C# の HttpClient クラス を使用します。
public static async void GetBuilds()
{
try
{
var personalaccesstoken = "PATFROMWEB";
using (HttpClient client = new HttpClient())
{
client.DefaultRequestHeaders.Accept.Add(
new System.Net.Http.Headers.MediaTypeWithQualityHeaderValue("application/json"));
client.DefaultRequestHeaders.Authorization = new AuthenticationHeaderValue("Basic",
Convert.ToBase64String(
System.Text.ASCIIEncoding.ASCII.GetBytes(
string.Format("{0}:{1}", "", personalaccesstoken))));
using (HttpResponseMessage response = client.GetAsync(
"https://dev.azure.com/{organization}/{project}/_apis/build/builds?api-version=5.0").Result)
{
response.EnsureSuccessStatusCode();
string responseBody = await response.Content.ReadAsStringAsync();
Console.WriteLine(responseBody);
}
}
}
catch (Exception ex)
{
Console.WriteLine(ex.ToString());
}
}
ヒント
変数を使用している場合は、次の例のように、文字列の先頭に a を追加 $ します。
public static async void GetBuilds()
{
try
{
var personalaccesstoken = "PATFROMWEB";
using (HttpClient client = new HttpClient())
{
client.DefaultRequestHeaders.Accept.Add(
new System.Net.Http.Headers.MediaTypeWithQualityHeaderValue("application/json"));
client.DefaultRequestHeaders.Authorization = new AuthenticationHeaderValue("Basic",
Convert.ToBase64String(
System.Text.ASCIIEncoding.ASCII.GetBytes(
string.Format("{0}:{1}", "", personalaccesstoken))));
using (HttpResponseMessage response = client.GetAsync(
$"https://dev.azure.com/{organization}/{project}/_apis/build/builds?api-version=5.0").Result)
{
response.EnsureSuccessStatusCode();
string responseBody = await response.Content.ReadAsStringAsync();
Console.WriteLine(responseBody);
}
}
}
catch (Exception ex)
{
Console.WriteLine(ex.ToString());
}
}
コードが動作している場合は、基本認証 から OAuth に切り替えるのが良い時期です。
AT の使用方法の詳細と例については、次の記事を参照してください。
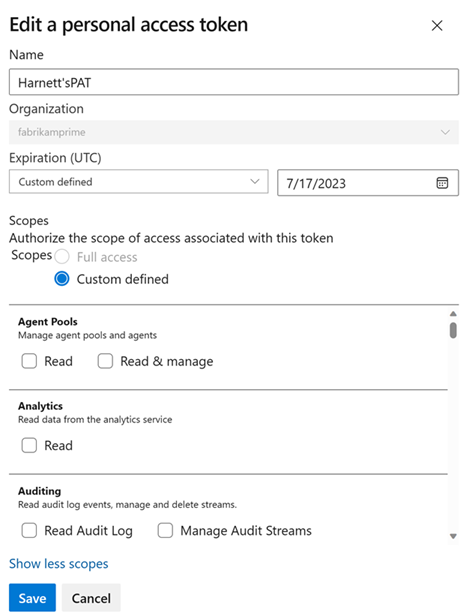
PAT を変更する
PAT を再生成または拡張し、そのスコープを変更できます。 再生成後、以前の PAT は承認されなくなります。
ホーム ページでユーザー設定を開き、[プロファイル] を選択 します。
[セキュリティ] で、[個人用アクセス トークン] を選択 します。 変更するトークンを選択し、[編集] を選択します。
![PAT を変更するために強調表示された [編集] ボタンを示すスクリーンショット。](/ja-jp/azure/devops/repos/git/media/select-edit-pat-current-view.png)
トークン名、トークンの有効期限、またはトークンに関連付けられているアクセスのスコープを編集し、[保存] を選択 します。
PAT を取り消す
さまざまな理由で、いつでも PAT を取り消すことができます。
ホーム ページでユーザー設定を開き、[プロファイル] を選択 します。
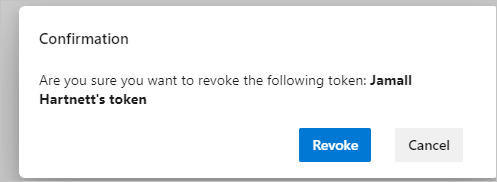
[セキュリティ] で、[個人用アクセス トークン] を選択 します。 アクセスを取り消すトークンを選択し、[取り消し] を選択します。

確認ダイアログで [取り消し] を選択します。
関連記事
- セキュリティ、認証、承認について
- Azure DevOps の既定のアクセス許可とアクセス
- ユーザーの AT を取り消す (管理者向け)
- Azure DevOps でサービス プリンシパルとマネージド ID を管理する
よく寄せられる質問
Q: ユーザー アカウントが無効になっている場合、PAT はどうなりますか?
A: ユーザーが Azure DevOps から削除されると、PAT は 1 時間以内に無効になります。 組織が Microsoft Entra ID に接続されている場合、PAT はユーザーに属しているため、Microsoft Entra ID でも無効になります。 サービスを実行し続けるために、ユーザーが PAT を別のユーザーまたはサービス アカウントにローテーションすることをお勧めします。
Q: REST API を使用して PAT を更新する方法はありますか。
A: はい。PAT ライフサイクル管理 API を使用して 、PAT を更新、管理、作成する方法があります。 詳細については、 REST API を使用した PAT の管理と FAQ に関するページを 参照してください。
Q: すべての Azure DevOps REST API で基本認証を使用できますか。
A: いいえ。 ほとんどの Azure DevOps REST API で基本認証を使用できますが、組織とプロファイルでは OAuth のみがサポートされています。 詳細については、REST API を使用した PAT の管理に関するページを参照してください。
Q: PAT を GitHub のパブリック リポジトリに誤ってチェックした場合はどうなりますか?
A: Azure DevOps は、GitHub 上のパブリック リポジトリにチェックされた AT をスキャンします。 漏洩したトークンが見つかると、すぐにトークン所有者に詳細な電子メール通知が送信され、イベントが Azure DevOps 組織の 監査ログに記録されます。 漏洩した個人用アクセス トークンの自動取り消しポリシーを無効にした場合を除き、漏洩した PAT は直ちに取り消されます。 影響を受けるユーザーは、漏洩したトークンを取り消して新しいトークンに置き換えることで、直ちに軽減することをお勧めします。
詳細については、「リークした AT を自動的に取り消す」を参照してください。
Q: 個人用アクセス トークンを ApiKey として使用して、dotnet/nuget.exe コマンド ラインを使用して NuGet パッケージを Azure Artifacts フィードに発行することはできますか。
A: いいえ。 Azure Artifacts では、個人用アクセス トークンを ApiKey として渡すことはサポートされていません。 ローカル開発環境を使用する場合は、Azure Artifacts で認証するために Azure Artifacts 資格情報プロバイダーをインストールすることをお勧めします。 詳細については、dotnet、NuGet.exe の次の例を参照してください。 Azure Pipelines を使用してパッケージを発行する場合は、NuGet 認証タスクを使用してフィードの例で認証します。
Q: PAT が機能しなくなったのはなぜですか?
A: PAT 認証では、完全な認証フローを使用して Azure DevOps に定期的にサインインする必要があります。 多くの場合、30 日に 1 回で十分ですが、Microsoft Entra の構成によっては、より頻繁にサインインする必要がある場合があります。 PAT が機能しなくなった場合は、最初に組織にサインインして、完全な認証プロンプトを確認してください。 その後も PAT が機能しない場合は、PAT の有効期限が切れているかどうかを確認チェック。
フィードバック
以下は間もなく提供いたします。2024 年を通じて、コンテンツのフィードバック メカニズムとして GitHub の issue を段階的に廃止し、新しいフィードバック システムに置き換えます。 詳細については、「https://aka.ms/ContentUserFeedback」を参照してください。
フィードバックの送信と表示