Självstudie: Distribuera från GitHub till Azure Kubernetes Service med Jenkins
Viktigt!
Många Azure-tjänster har Jenkins-plugin-program. Vissa av dessa plugin-program kommer att vara utan stöd från och med den 29 februari 2024. Azure CLI är det för närvarande rekommenderade sättet att integrera Jenkins med Azure-tjänster. Mer information finns i artikeln Jenkins-plugin-program för Azure.
Den här självstudien distribuerar en exempelapp från GitHub till ett AKS-kluster (Azure Kubernetes Service) genom att konfigurera kontinuerlig integrering (CI) och kontinuerlig distribution (CD) i Jenkins.
I den här självstudien får du utföra följande uppgifter:
- Distribuera en Azure-exempelröstapp till ett AKS-kluster.
- Skapa ett grundläggande Jenkins-projekt.
- Konfigurera autentiseringsuppgifter för Jenkins för att interagera med ACR.
- Skapa ett Jenkins-byggjobb och GitHub-webhook för automatiserade versioner.
- Testa CI/CD-pipelinen för att uppdatera ett program i AKS baserat på GitHub-kodincheckningar.
Förutsättningar
För att slutföra den här självstudien behöver du följande objekt:
Grundläggande förståelse för Kubernetes-, Git-, CI/CD- och containeravbildningar
Ett AKS-kluster och
kubectlkonfigurerat med autentiseringsuppgifterna för AKS-klustret.Ett ACR-register (Azure Container Registry), namnet på ACR-inloggningsservern och AKS-klustret som konfigurerats för att autentisera med ACR-registret.
En Jenkins-kontrollant distribuerad till en virtuell Azure-dator.
Azure CLI version 2.0.46 eller senare har installerats och konfigurerats. Kör
az --versionför att hitta versionen. Om du behöver installera eller uppgradera kan du läsa Installera Azure CLI.Docker installerat i ditt utvecklingssystem
Ett GitHub-konto, en personlig GitHub-åtkomsttoken och En Git-klient som är installerad i ditt utvecklingssystem
Om du anger en egen Jenkins-instans i stället för det här skriptexemplet för att distribuera Jenkins behöver Jenkins-instansen Docker installerat och konfigurerat och kubectl.
Förbereda din app
I den här artikeln använder du ett Azure-exempelröstprogram som innehåller ett webbgränssnitt och Redis för tillfällig datalagring.
Innan du integrerar Jenkins och AKS för automatiserade distributioner måste du först manuellt förbereda och distribuera Azure-röstprogrammet till ditt AKS-kluster. Med den här manuella distributionen kan du se programmet i praktiken.
Kommentar
Exempelprogrammet för Azure-omröstning använder en Linux-podd som är schemalagd att köras på en Linux-nod. Flödet som beskrivs i den här artikeln fungerar också för en Windows Server-podd som schemalagts på en Windows Server-nod.
Förgrena följande GitHub-lagringsplats för exempelprogrammet – https://github.com/Azure-Samples/azure-voting-app-redis. Om du vill förgrena lagringsplatsen till ditt eget GitHub-konto väljer du knappen Fork (Förgrening) i det övre högra hörnet.
Klona förgreningen till ditt utvecklingssystem. Se till att du använder URL:en för din förgrening när du klonar den här lagringsplatsen:
git clone https://github.com/<your-github-account>/azure-voting-app-redis.git
Ändra till katalogen för din klonade förgrening:
cd azure-voting-app-redis
Om du vill skapa de containeravbildningar som behövs för exempelprogrammet använder du filen docker-compose.yaml med docker-compose:
docker-compose up -d
De nödvändiga basavbildningarna hämtas och programcontainrarna skapas. Du kan sedan använda kommandot docker images för att se den skapade avbildningen. Tre avbildningar har hämtats eller skapats. azure-vote-front-avbildningen innehåller programmet och använder nginx-flask-avbildningen som bas. Avbildningen redis används för att starta en Redis-instans:
$ docker images
REPOSITORY TAG IMAGE ID CREATED SIZE
azure-vote-front latest 9cc914e25834 40 seconds ago 694MB
redis latest a1b99da73d05 7 days ago 106MB
tiangolo/uwsgi-nginx-flask flask 788ca94b2313 9 months ago 694MB
Logga in på ditt Azure-containerregister.
az acr login -n <acrLoginServer>
Ersätt <acrLoginServer> med din ACR-inloggningsserver.
Använd docker-taggkommandot för att tagga avbildningen med namnet på ACR-inloggningsservern och versionsnumret v1. Använd ditt eget <acrLoginServer> namn som erhölls i föregående steg:
docker tag azure-vote-front <acrLoginServer>/azure-vote-front:v1
Slutligen push-överför du avbildningen azure-vote-front till ditt ACR-register. <acrLoginServer> Ersätt återigen med inloggningsservernamnet för ditt eget ACR-register, till exempel myacrregistry.azurecr.io:
docker push <acrLoginServer>/azure-vote-front:v1
Distribuera exempelprogrammet till AKS
Om du vill distribuera exempelprogrammet till ditt AKS-kluster kan du använda Kubernetes-manifestfilen i roten på lagringsplatsen för Azure-röstlagringsplatsen. azure-vote-all-in-one-redis.yaml Öppna manifestfilen med en redigerare som vi. Ersätt microsoft med namnet på din ACR-inloggningsserver. Det här värdet finns på rad 60 i manifestfilen:
containers:
- name: azure-vote-front
image: azuredocs/azure-vote-front
Använd sedan kommandot kubectl apply för att distribuera programmet till ditt AKS-kluster:
kubectl apply -f azure-vote-all-in-one-redis.yaml
En Kubernetes-lastbalanserare har skapats för att exponera programmet för Internet. Den här processen kan ta några minuter. Om du vill övervaka förloppet för distributionen av lastbalanseraren använder du kommandot kubectl get service med --watch argumentet . När EXTERNAL-IP-adressen har ändrats från pending till en IP-adress använder du Control + C för att stoppa kubectl-övervakningsprocessen.
$ kubectl get service azure-vote-front --watch
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
azure-vote-front LoadBalancer 10.0.215.27 <pending> 80:30747/TCP 22s
azure-vote-front LoadBalancer 10.0.215.27 40.117.57.239 80:30747/TCP 2m
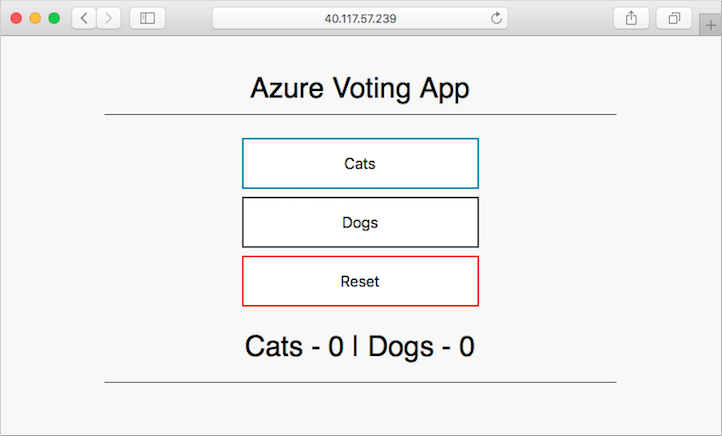
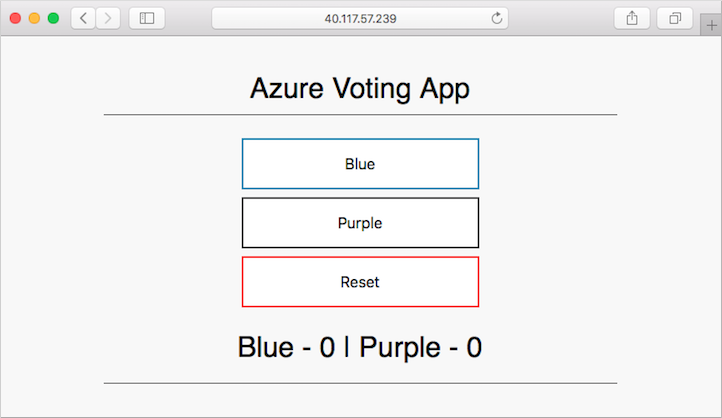
Om du vill se programmet i praktiken öppnar du en webbläsare till tjänstens externa IP-adress. Azure vote-programmet visas, som du ser i följande exempel:
Konfigurera Jenkins-styrenhet
Använd följande ändringar för att aktivera AKS-distributioner från Jenkins-kontrollanten:
Öppna inkommande port 80 .
az vm open-port \
--resource-group <Resource_Group_name> \
--name <Jenkins_Controller_VM> \
--port 80 --priority 1020
Ersätt <Resource_Group_name> och <Jenkins_Controller_VM> med lämpliga värden.
SSH till Jenkins-kontrollanten
ssh azureuser@<PublicIPAddres>
Ersätt <PublicIPAddress> med IP-adressen för Jenkins-kontrollanten.
Installera och logga in på AzCLI
curl -L https://aka.ms/InstallAzureCli | bash
az login
Kommentar
Om du vill installera AzCLI manuellt följer du de här anvisningarna.
Installera Docker
sudo apt-get install apt-transport-https ca-certificates curl software-properties-common -y;
curl -fsSL https://download.docker.com/linux/ubuntu/gpg | sudo apt-key add -;
sudo apt-key fingerprint 0EBFCD88;
sudo add-apt-repository "deb [arch=amd64] https://download.docker.com/linux/ubuntu $(lsb_release -cs) stable";
sudo apt-get update;
sudo apt-get install docker-ce -y;
Installera Kubectl och Anslut till AKS
sudo az aks install-cli
sudo az aks get-credentials --resource-group <Resource_Group> --name <AKS_Name>
Ersätt <Resource_Group> och <AKS_Name> med lämpliga värden.
Konfigurera åtkomst
sudo usermod -aG docker jenkins;
sudo usermod -aG docker azureuser;
sudo touch /var/lib/jenkins/jenkins.install.InstallUtil.lastExecVersion;
sudo service jenkins restart;
sudo cp ~/.kube/config /var/lib/jenkins/.kube/
sudo chmod 777 /var/lib/jenkins/
sudo chmod 777 /var/lib/jenkins/config
Skapa en Jenkins-miljövariabel
En Jenkins-miljövariabel används för att lagra namnet på ACR-inloggningsservern. Den här variabeln refereras under Jenkins-byggjobbet. Utför följande steg för att skapa den här miljövariabeln:
Till vänster i Jenkins-portalen väljer du Hantera Jenkins>Konfigurera system
Under Globala egenskaper väljer du Miljövariabler. Lägg till en variabel med namnet
ACR_LOGINSERVERoch värdet för din ACR-inloggningsserver.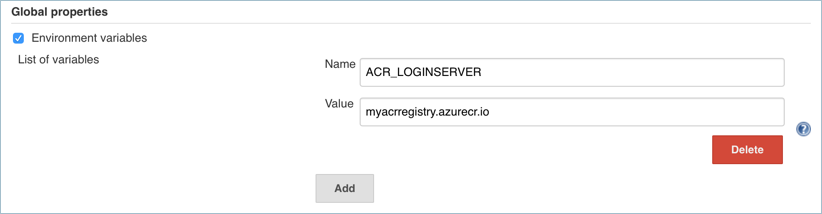
När du är klar väljer du Spara längst ned på sidan.
Skapa en Jenkins-autentiseringsuppgift för ACR
Under CI/CD-processen skapar Jenkins nya containeravbildningar baserat på programuppdateringar och måste sedan skicka dessa avbildningar till ACR-registret.
Om du vill att Jenkins ska kunna skicka uppdaterade containeravbildningar till ACR måste du ange autentiseringsuppgifter för ACR.
För uppdelning av roller och behörigheter konfigurerar du ett huvudnamn för tjänsten för Jenkins med deltagarbehörighet till ditt ACR-register.
Skapa ett tjänsthuvudnamn för Jenkins för att använda ACR
Skapa först ett huvudnamn för tjänsten med kommandot az ad sp create-for-rbac :
az ad sp create-for-rbac
Det här kommandot genererar utdata som liknar följande exempel:
{
"appId": "<app-ID>",
"displayName": "azure-cli-2018-09-28-22-19-34",
"name": "http://azure-cli-2018-09-28-22-19-34",
"password": "<password>",
"tenant": "<tenant-ID>"
}
Anteckna värdena för appId och password. Dessa värden används i följande steg för att konfigurera resursen för autentiseringsuppgifter i Jenkins.
Hämta resurs-ID:t för ditt ACR-register med kommandot az acr show och lagra det som en variabel.
ACR_ID=$(az acr show --resource-group <Resource_Group> --name <acrLoginServer> --query "id" --output tsv)
Ersätt <Resource_Group> och <acrLoginServer> med lämpliga värden.
Skapa en rolltilldelning för att tilldela behörigheten för tjänstens huvudnamn deltagare till ACR-registret.
az role assignment create --assignee <appID> --role Contributor --scope $ACR_ID
Ersätt <appId> med värdet som anges i utdata från det pervious-kommando som används för att skapa tjänstens huvudnamn.
Skapa en autentiseringsresurs i Jenkins för ACR-tjänstens huvudnamn
När rolltilldelningen har skapats i Azure lagrar du nu dina ACR-autentiseringsuppgifter i ett Jenkins-autentiseringsobjekt. Dessa autentiseringsuppgifter refereras under Jenkins-byggjobbet.
På vänster sida av Jenkins-portalen väljer du Hantera Jenkins>Hantera autentiseringsuppgifter>Jenkins Store>Globala autentiseringsuppgifter (obegränsad)>Lägg till autentiseringsuppgifter
Kontrollera att typen av autentiseringsuppgifter är Användarnamn med lösenord och ange följande objekt:
- Användarnamn – appId för tjänstens huvudnamn som skapats för autentisering med ditt ACR-register.
- Lösenord – lösenordet för tjänstens huvudnamn som skapats för autentisering med ditt ACR-register.
- ID – Identifierare för autentiseringsuppgifter, till exempel acr-credentials
När det är klart ser formuläret för autentiseringsuppgifter ut som i följande exempel:
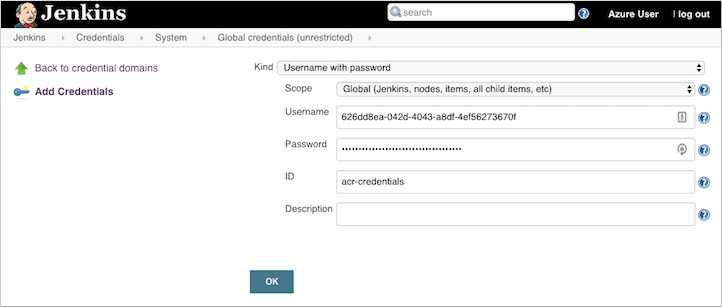
Välj OK och gå tillbaka till Jenkins-portalen.
Skapa ett Jenkins-projekt
På startsidan i Jenkins-portalen väljer du Nytt objekt till vänster:
Ange azure-vote som jobbnamn. Välj Freestyle-projekt och välj sedan OK
Under avsnittet Allmänt väljer du GitHub-projekt och anger din förgrenade lagringsplats-URL, till exempel https://github.com/<your-github-account>/azure-voting-app-redis
Under avsnittet Källkodshantering väljer du Git, anger din förgrenade lagringsplats-URL
.git, till exempel https://github.com/<your-github-account>/azure-voting-app-redis.gitUnder avsnittet Build Triggers (Skapa utlösare) väljer du GitHub-hook-utlösare för GITscm-avsökning
Under Skapa miljö väljer du Använd hemliga texter eller filer
Under Bindningar väljer du Lägg till>användarnamn och lösenord (avgränsat)
Ange
ACR_IDför användarnamnvariabeln ochACR_PASSWORDför lösenordsvariabeln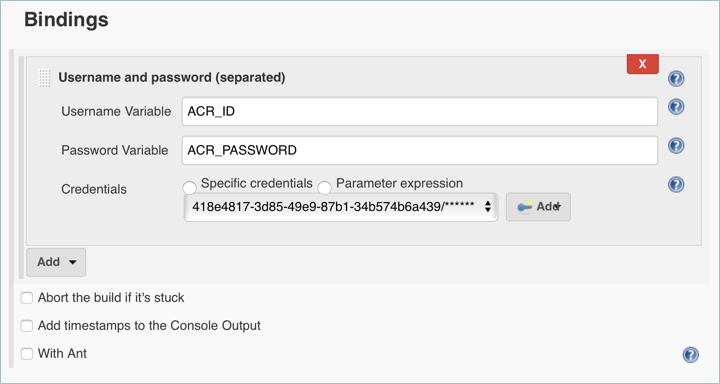
Välj att lägga till ett build-steg av typen Execute shell och använd följande text. Det här skriptet skapar en ny containeravbildning och skickar den till ditt ACR-register.
# Build new image and push to ACR. WEB_IMAGE_NAME="${ACR_LOGINSERVER}/azure-vote-front:kube${BUILD_NUMBER}" docker build -t $WEB_IMAGE_NAME ./azure-vote docker login ${ACR_LOGINSERVER} -u ${ACR_ID} -p ${ACR_PASSWORD} docker push $WEB_IMAGE_NAMELägg till ytterligare ett build-steg av typen Execute shell och använd följande text. Det här skriptet uppdaterar programdistributionen i AKS med den nya containeravbildningen från ACR.
# Update kubernetes deployment with new image. WEB_IMAGE_NAME="${ACR_LOGINSERVER}/azure-vote-front:kube${BUILD_NUMBER}" kubectl set image deployment/azure-vote-front azure-vote-front=$WEB_IMAGE_NAMENär du är klar klickar du på Spara.
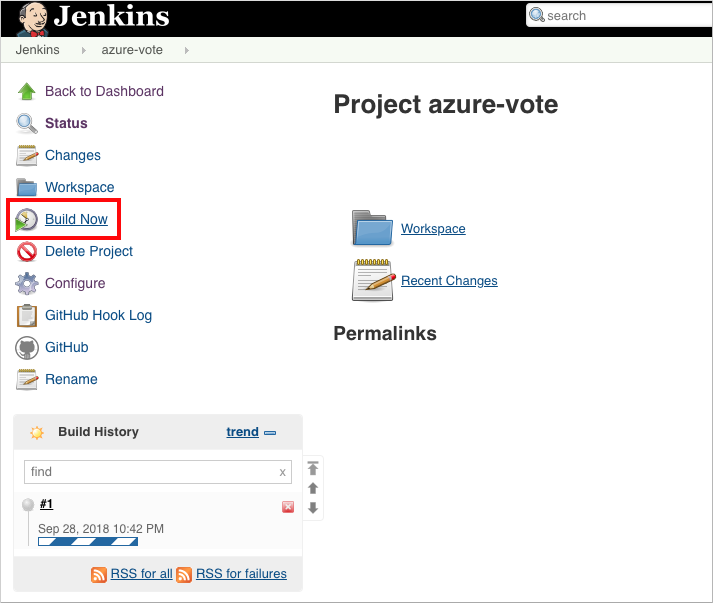
Testa Jenkins-versionen
Innan du automatiserar jobbet baserat på GitHub-incheckningar testar du Jenkins-versionen manuellt.
Den här versionen verifierar att jobbet har konfigurerats korrekt. Den bekräftar att rätt Kubernetes-autentiseringsfil finns på plats och att autentiseringen till ACR fungerar.
På den vänstra menyn i projektet väljer du Skapa nu.
Den första versionen längre när Docker-avbildningsskikten hämtas till Jenkins-servern.
Byggena utför följande uppgifter:
- Klonar GitHub-lagringsplatsen
- Skapar en ny containeravbildning
- Skickar containeravbildningen till ACR-registret
- Uppdateringar avbildningen som används av AKS-distributionen
Eftersom inga ändringar har gjorts i programkoden är webbgränssnittet oförändrat.
När byggjobbet är klart väljer du build #1 under versionshistorik. Välj Konsolutdata och visa utdata från byggprocessen. Den sista raden bör indikera ett lyckat bygge.
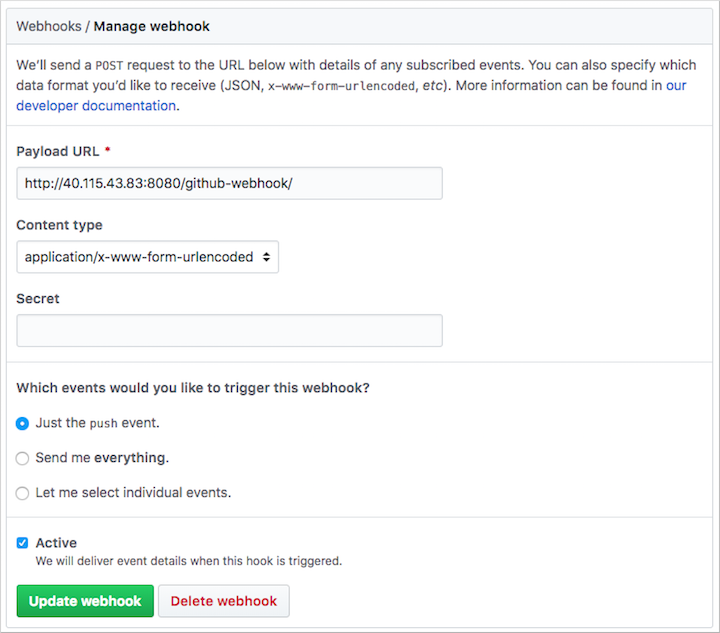
Skapa en GitHub-webhook
Nu när en manuell version har slutförts integrerar du GitHub i Jenkins-versionen. Använd en webhook för att köra Jenkins-byggjobbet varje gång koden checkas in på GitHub.
Utför följande steg för att skapa GitHub-webhooken:
Bläddra till din förgrenade GitHub-lagringsplats i en webbläsare.
Välj Inställningar och sedan Webhooks på vänster sida.
Välj lägg till webhook. För payload-URL:en anger du
http://<publicIp:8080>/github-webhook/, där<publicIp>är IP-adressen för Jenkins-servern. Se till att inkludera den avslutande/. Lämna de andra standardvärdena för innehållstyp och för att utlösa push-händelser.Välj Lägg till webhook.
Testa den fullständiga CI/CD-pipelinen
Nu kan du testa hela CI/CD-pipelinen. När du skickar en kodincheckning till GitHub sker följande steg:
- GitHub-webhooken meddelar Jenkins.
- Jenkins startar byggjobbet och hämtar den senaste kodincheckningen från GitHub.
- En Docker-version startas med den uppdaterade koden och den nya containeravbildningen taggas med det senaste versionsnumret.
- Den här nya containeravbildningen skickas till Azure Container Registry.
- Ditt program som körs på Azure Kubernetes Service uppdateras med den senaste avbildningen från Azure Container Registry.
Öppna det klonade programmet med en kodredigerare på utvecklingsdatorn. Under katalogen /azure-vote/azure-vote öppnar du filen med namnet config_file.cfg. Uppdatera röstvärdena i den här filen till något annat än katter och hundar, som du ser i följande exempel:
# UI Configurations
TITLE = 'Azure Voting App'
VOTE1VALUE = 'Blue'
VOTE2VALUE = 'Purple'
SHOWHOST = 'false'
När du har uppdaterat filen sparar du filen, checkar in ändringarna och push-överför dem till din förgrening av GitHub-lagringsplatsen. GitHub-webhooken utlöser ett nytt byggjobb i Jenkins. Övervaka byggprocessen på Jenkins-webbinstrumentpanelen. Det tar några sekunder att hämta den senaste koden, skapa och push-överföra den uppdaterade avbildningen och distribuera det uppdaterade programmet i AKS.
När bygget är klart uppdaterar du webbläsaren för azure-exempelprogrammet för omröstning. Ändringarna visas enligt följande exempel:
Nästa steg
Feedback
Kommer snart: Under hela 2024 kommer vi att fasa ut GitHub-problem som feedbackmekanism för innehåll och ersätta det med ett nytt feedbacksystem. Mer information finns i: https://aka.ms/ContentUserFeedback.
Skicka och visa feedback för