Events
Apr 9, 3 PM - Apr 10, 12 PM
Code the Future with AI and connect with Java peers and experts at JDConf 2025.
Register NowThis browser is no longer supported.
Upgrade to Microsoft Edge to take advantage of the latest features, security updates, and technical support.
Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
In this article, you learn how to integrate Workplace by Meta with Microsoft Entra ID. When you integrate Workplace by Meta with Microsoft Entra ID, you can:
The scenario outlined in this article assumes that you already have the following prerequisites:
Note
Meta has two products, Workplace Standard (free) and Workplace Premium (paid). Any Workplace Premium tenant can configure SCIM and SSO integration with no other implications to cost or licenses required. SSO and SCIM aren't available in Workplace Standard instances.
In this article, you configure and test Microsoft Entra SSO in a test environment.
To configure the integration of Workplace by Meta into Microsoft Entra ID, you need to add Workplace by Meta from the gallery to your list of managed SaaS apps.
Alternatively, you can also use the Enterprise App Configuration Wizard. In this wizard, you can add an application to your tenant, add users/groups to the app, assign roles, and walk through the SSO configuration as well. Learn more about Microsoft 365 wizards.
Configure and test Microsoft Entra SSO with Workplace by Meta using a test user called B.Simon. For SSO to work, you need to establish a link relationship between a Microsoft Entra user and the related user in Workplace by Meta.
To configure and test Microsoft Entra SSO with Workplace by Meta, perform the following steps:
Follow these steps to enable Microsoft Entra SSO.
Sign in to the Microsoft Entra admin center as at least a Cloud Application Administrator.
Browse to Identity > Applications > Enterprise applications > Workplace by Meta application integration page, find the Manage section and select Single sign-on.
On the Select a Single sign-on method page, select SAML.
On the Set up Single Sign-On with SAML page, select the pencil icon for Basic SAML Configuration to edit the settings.
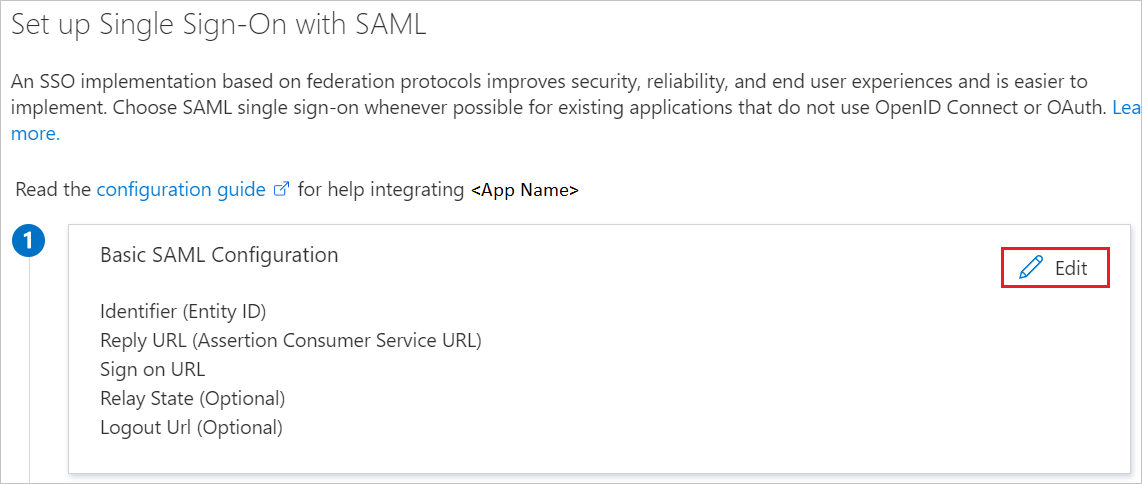
On the Basic SAML Configuration section, enter the values for the following fields:
a. In the Sign on URL (found in WorkPlace as the Recipient URL) text box, type a URL using the following pattern:
https://.workplace.com/work/saml.php
b. In the Identifier (Entity ID) (found in WorkPlace as the Audience URL) text box, type a URL using the following pattern:
https://www.workplace.com/company/
c. In the Reply URL (found in WorkPlace as the Assertion Consumer Service) text box, type a URL using the following pattern:
https://.workplace.com/work/saml.php
Note
These values aren't the real. Update these values with the actual Sign-On URL, Identifier and Reply URL. See the Authentication page of the Workplace Company Dashboard for the correct values for your Workplace community, this is explained later in the article.
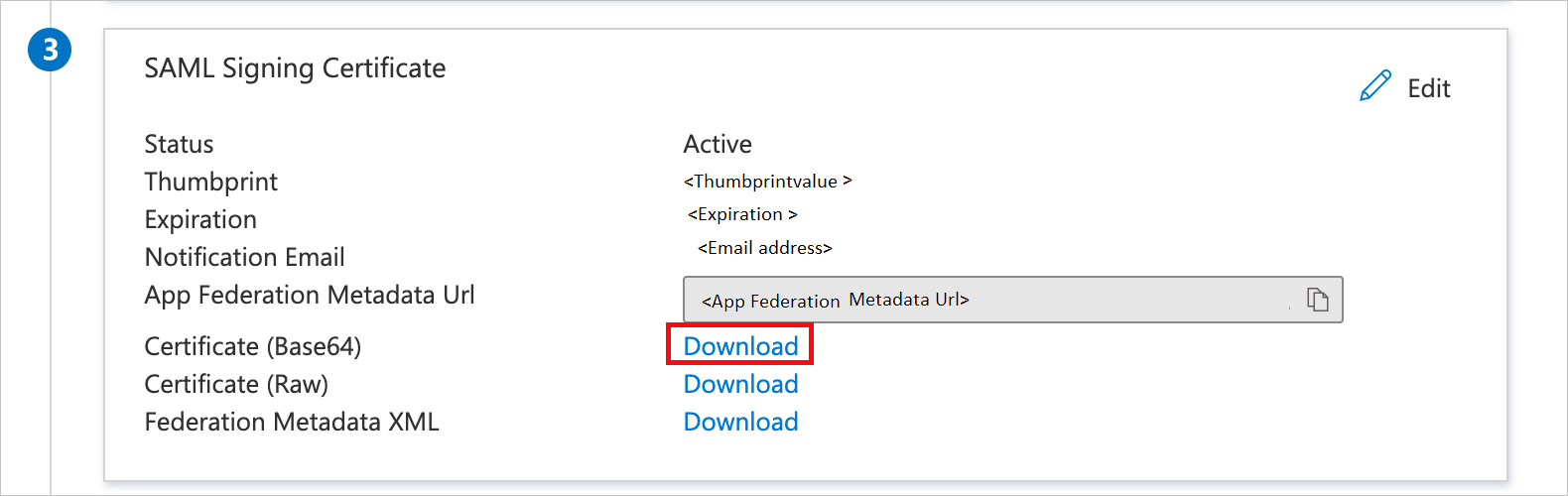
On the Set up Single Sign-On with SAML page, in the SAML Signing Certificate section, find Certificate (Base64) and select Download to download the certificate and save it on your computer.
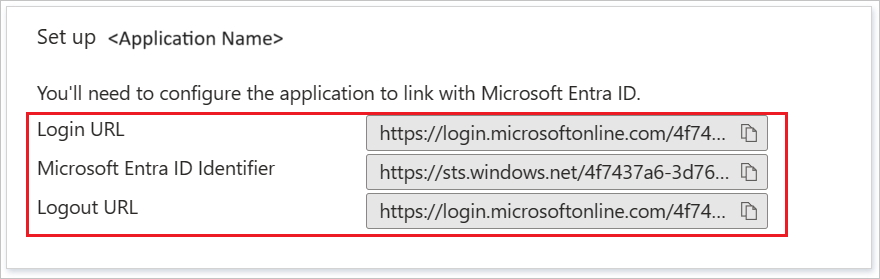
On the Set up Workplace by Meta section, copy the appropriate URL(s) based on your requirement.
Follow the guidelines in the create and assign a user account quickstart to create a test user account called B.Simon.
In a different web browser window, sign in to your Workplace by Meta company site as an administrator
Note
As part of the SAML authentication process, Workplace may utilize query strings of up to 2.5 kilobytes in size in order to pass parameters to Microsoft Entra ID.
Navigate to Admin Panel > Security > Authentication tab.

a. Check the Single-sign on(SSO) option.
b. Select SSO as default for new users.
c. Select +Add new SSO Provider.
Note
Make sure you check the Password login checkbox too. Admins may need this option for login while doing the certificate rollover in order to stop themselves getting locked out.
In the Single Sign-On (SSO) Setup pop-up window, perform the following steps:

a. In the Name of the SSO Provider, enter the SSO instance name like Azureadsso.
b. In SAML URL textbox, paste the value of Login URL.
c. In SAML Issuer URL textbox, paste the value of Microsoft Entra Identifier.
d. Open the downloaded Certificate (Base64) into Notepad, copy the content of it into your clipboard, and then paste it to the SAML Certificate textbox.
e. Copy the Audience URL for your instance and paste it in Identifier (Entity ID) textbox in Basic SAML Configuration section.
f. Copy the Recipient URL for your instance and paste it in Sign on URL textbox in Basic SAML Configuration section.
g. Copy the ACS (Assertion Consumer Service) URL for your instance and paste it in Reply URL textbox in Basic SAML Configuration section.
h. Scroll to the bottom of the section and select the Test SSO button. This results in a pop-up window appearing with Microsoft Entra login page presented. Enter your credentials in as normal to authenticate.
Troubleshooting: Ensure the email address being returned back from Microsoft Entra ID is the same as the Workplace account you're logged in with.
i. Once the test has been completed successfully, scroll to the bottom of the page and select the Save button.
j. All users using Workplace will now be presented with Microsoft Entra login page for authentication.
SAML Logout Redirect (optional) -
You can choose to optionally configure a SAML Logout URL, which can be used to point at Microsoft Entra ID's logout page. When this setting is enabled and configured, the user will no longer be directed to the Workplace logout page. Instead, the user is redirected to the URL that was added in the SAML Logout Redirect setting.
You can configure Workplace to prompt for a SAML check every day, three days, week, two weeks, month or never.
Note
The minimum value for the SAML check on mobile applications is set to one week.
You can also force a SAML reset for all users using the button: Require SAML authentication for all users now.
In this section, a user called B.Simon is created in Workplace by Meta. Workplace by Meta supports just-in-time provisioning, which is enabled by default.
There's no action for you in this section. If a user doesn't exist in Workplace by Meta, a new one is created when you attempt to access Workplace by Meta.
Note
If you need to create a user manually, Contact Workplace by Meta Client support team.
In this section, you test your Microsoft Entra single sign-on configuration with following options.
Select Test this application, this option redirects to Workplace by Meta Sign-on URL where you can initiate the login flow.
Go to Workplace by Meta Sign-on URL directly and initiate the login flow from there.
You can use Microsoft My Apps. When you select the Workplace by Meta tile in the My Apps, this option redirects to Workplace by Meta Sign-on URL. For more information about the My Apps, see Introduction to the My Apps.
Open Workplace by Meta Mobile application. On the sign in page, select LOG IN.

Enter your business email and select CONTINUE.

Select JUST ONCE.

Select Allow.

Finally after successful sign in, the application homepage is displayed.

Once you configure Workplace by Meta you can enforce Session control, which protects exfiltration and infiltration of your organization's sensitive data in real time. Session control extends from Conditional Access. Learn how to enforce session control with Microsoft Defender for Cloud Apps.
Events
Apr 9, 3 PM - Apr 10, 12 PM
Code the Future with AI and connect with Java peers and experts at JDConf 2025.
Register Now