Training
Module
Azure Key and Certificate Management - Training
In this module, you learn about essential concepts for using encryption keys and digital certificates in Azure to help secure cloud workloads and ensure data sovereignty.
This browser is no longer supported.
Upgrade to Microsoft Edge to take advantage of the latest features, security updates, and technical support.
Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
APPLIES TO:  Azure Data Factory
Azure Data Factory  Azure Synapse Analytics
Azure Synapse Analytics
Tip
Try out Data Factory in Microsoft Fabric, an all-in-one analytics solution for enterprises. Microsoft Fabric covers everything from data movement to data science, real-time analytics, business intelligence, and reporting. Learn how to start a new trial for free!
Azure Data Factory encrypts data at rest, including entity definitions and any data cached while runs are in progress. By default, data is encrypted with a randomly generated Microsoft-managed key that is uniquely assigned to your data factory. For extra security guarantees, you can now enable Bring Your Own Key (BYOK) with customer-managed keys feature in Azure Data Factory. When you specify a customer-managed key (CMK), Data Factory uses both the factory system key and the CMK to encrypt customer data. Missing either would result in Deny of Access to data and factory.
Azure Key Vault is required to store customer-managed keys. You can either create your own keys and store them in a key vault, or you can use the Azure Key Vault APIs to generate keys. Key vault and Data Factory must be in the same Microsoft Entra tenant and in the same region, but they may be in different subscriptions. For more information about Azure Key Vault, see What is Azure Key Vault?
The following diagram shows how Data Factory uses Microsoft Entra ID and Azure Key Vault to make requests using the customer-managed key:
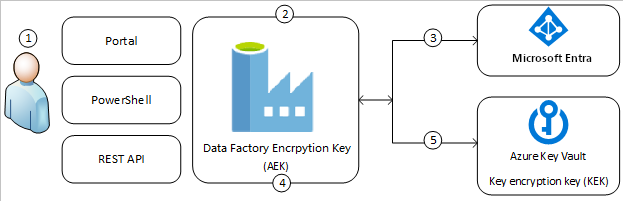
The following list explains the numbered steps in the diagram:
There are two ways of adding Customer Managed Key encryption to data factories. One is during factory creation time in Azure portal, and the other is post factory creation, in Data Factory UI.
Using customer-managed keys with Data Factory requires two properties to be set on the Key Vault, Soft Delete and Do Not Purge. These properties can be enabled using either PowerShell or Azure CLI on a new or existing key vault. To learn how to enable these properties on an existing key vault, see Azure Key Vault recovery management with soft delete and purge protection
If you are creating a new Azure Key Vault through Azure portal, Soft Delete and Do Not Purge can be enabled as follows:

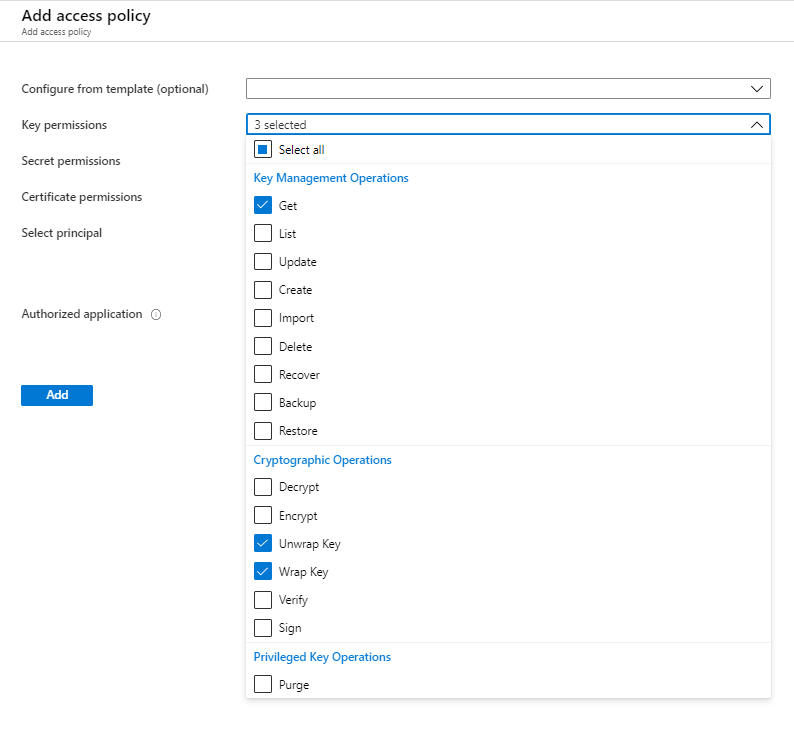
Make sure Azure Key Vault and Azure Data Factory are in the same Microsoft Entra tenant and in the same region. From Azure Key Vault access control, grant data factory following permissions: Get, Unwrap Key, and Wrap Key. These permissions are required to enable customer-managed keys in Data Factory.
If you want to add customer managed key encryption after factory creation in Data Factory UI, ensure data factory's managed service identity (MSI) has the three permissions to Key Vault
If you want to add customer managed key encryption during factory creation time in Azure portal, ensure the user-assigned managed identity (UA-MI) has the three permissions to Key Vault
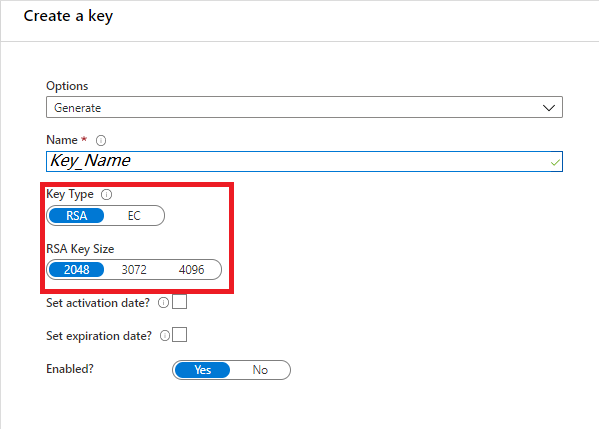
You can either create your own keys and store them in a key vault. Or you can use the Azure Key Vault APIs to generate keys. Only RSA keys are supported with Data Factory encryption. RSA-HSM is also supported. For more information, see About keys, secrets, and certificates.
This section walks through the process to add customer managed key encryption in Data Factory UI, after factory is created.
Note
A customer-managed key can only be configured on an empty data Factory. The data factory can't contain any resources such as linked services, pipelines and data flows. It is recommended to enable customer-managed key right after factory creation.
Important
This approach does not work with managed virtual network enabled factories. Consider the alternative route, if you want to encrypt such factories.
Make sure that data factory's Managed Service Identity (MSI) has Get, Unwrap Key and Wrap Key permissions to Key Vault.
Ensure the Data Factory is empty. The data factory can't contain any resources such as linked services, pipelines, and data flows. For now, deploying customer-managed key to a non-empty factory will result in an error.
To locate the key URI in the Azure portal, navigate to Azure Key Vault, and select the Keys setting. Select the wanted key, then select the key to view its versions. Select a key version to view the settings
Copy the value of the Key Identifier field, which provides the URI

Launch Azure Data Factory portal, and using the navigation bar on the left, jump to Data Factory Management Portal
Select the Customer managed key icon
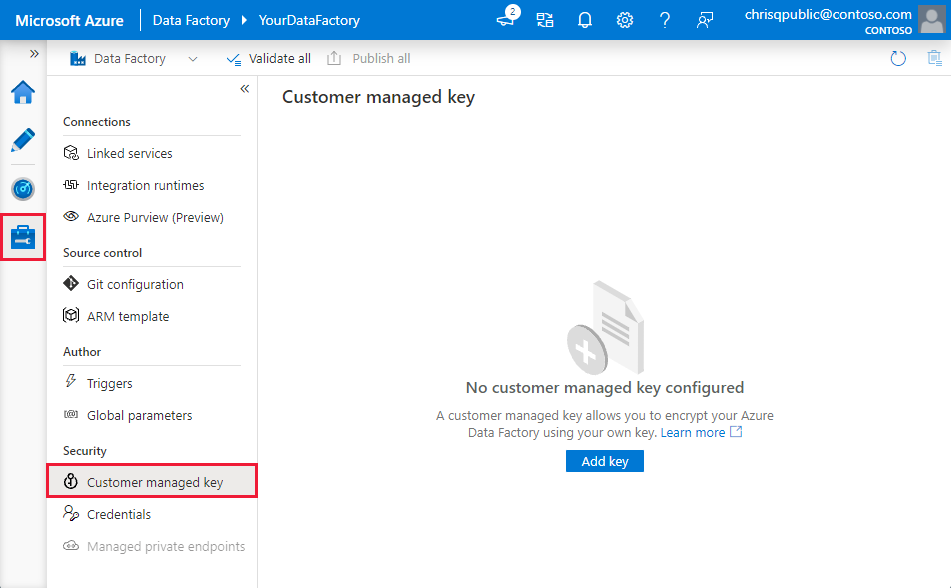
Enter the URI for customer-managed key that you copied before
Select Save and customer-managed key encryption is enabled for Data Factory
This section walks through steps to add customer managed key encryption in Azure portal, during factory deployment.
To encrypt the factory, Data Factory needs to first retrieve customer-managed key from Key Vault. Since factory deployment is still in progress, Managed Service Identity (MSI) isn't available yet to authenticate with Key Vault. As such, to use this approach, customer needs to assign a user-assigned managed identity (UA-MI) to data factory. We will assume the roles defined in the UA-MI and authenticate with Key Vault.
To learn more about user-assigned managed identity, see Managed identity types and Role assignment for user assigned managed identity.
Make sure that User-assigned Managed Identity (UA-MI) has Get, Unwrap Key and Wrap Key permissions to Key Vault
Under Advanced tab, check the box for Enable encryption using a customer managed key
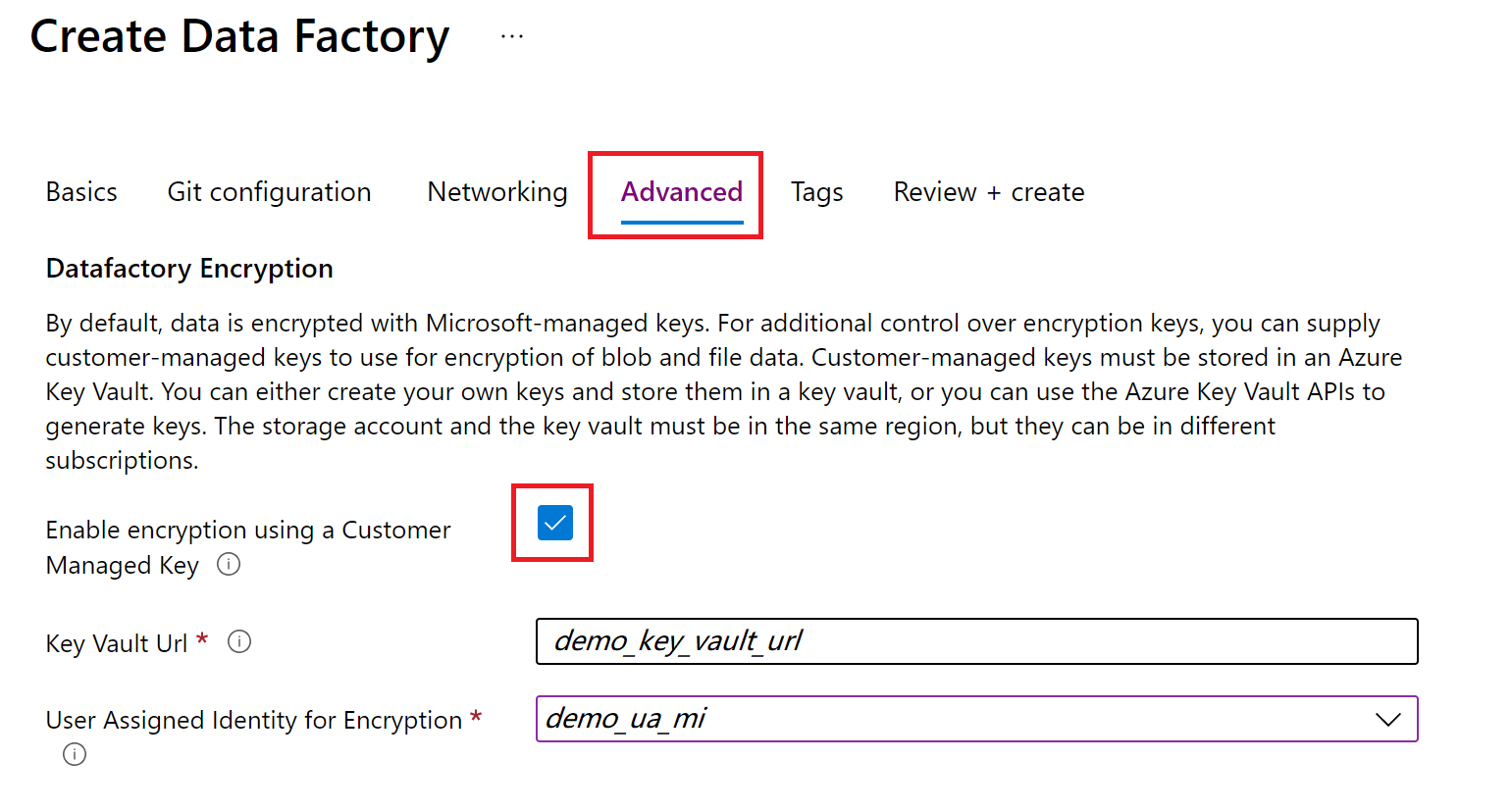
Provide the url for the customer managed key stored in Key Vault
Tip
If you don't pass the key version in the URL after the final '/' (for example: https://mykeyvault.vault.azure.net/keys/cmk/), the version will always default to the latest if the key is updated in the future.
Currently this is only supported using the Azure portal.
Select an appropriate user assigned managed identity to authenticate with Azure Key Vault.
Continue with your factory deployment.
When you create a new version of a key, update data factory to use the new version:
Locate the URI for the new key version through Azure Key Vault Portal:
Copy the value of the Key Identifier field, which provides the URI.
Launch Azure Data Factory portal, and using the navigation bar on the left, select the Data Factory Management Portal.
Select the Customer-managed key setting.
Enter the URI for customer-managed key that you copied before.
Select Save and Data Factory will now encrypt with the new key version.
To change key used for Data Factory encryption, you have to manually update the settings in Azure Data Factory:
Locate the URI for the new key version through Azure Key Vault Portal:
Copy the value of the Key Identifier field, which provides the URI.
Launch Azure Data Factory portal, and using the navigation bar on the left, select the Data Factory Management Portal.
Select the Customer-managed key setting.
Enter the URI for select that you copied before.
Select Save and Data Factory will now encrypt with the new key version.
By design, once the select feature is enabled, you can't remove the extra security step. We will always expect a customer provided key to encrypt factory and data.
By default, CMK configuration is not included in the factory Azure Resource Manager (ARM) template. To include the customer managed key encryption settings in ARM template for continuous integration (CI/CD):

The following settings will be added in ARM template. These properties can be parameterized in Continuous Integration and Delivery pipelines by editing the Azure Resource Manager parameters configuration
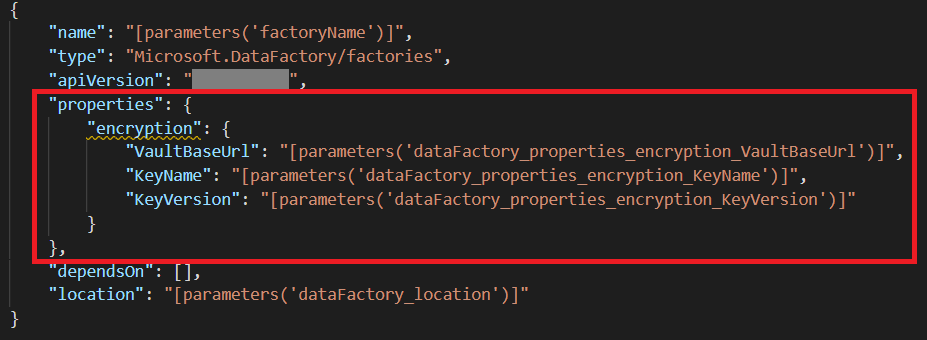
Note
Adding the encryption setting to the ARM templates adds a factory-level setting that will override other factory level settings, such as git configurations, in other environments. If you have these settings enabled in an elevated environment such as UAT or PROD, refer to Global Parameters in CI/CD.
Go through the tutorials to learn about using Data Factory in more scenarios.
Training
Module
Azure Key and Certificate Management - Training
In this module, you learn about essential concepts for using encryption keys and digital certificates in Azure to help secure cloud workloads and ensure data sovereignty.