Events
Apr 29, 2 PM - Apr 30, 7 PM
Join the ultimate Windows Server virtual event April 29-30 for deep-dive technical sessions and live Q&A with Microsoft engineers.
Sign up nowThis browser is no longer supported.
Upgrade to Microsoft Edge to take advantage of the latest features, security updates, and technical support.
You can use Microsoft Entra Domain Services in your Remote Desktop Services deployment in the place of Windows Server Active Directory. Microsoft Entra Domain Services lets you use your existing Microsoft Entra identities in with classic Windows workloads.
With Microsoft Entra Domain Services you can:
When you finish integrating Microsoft Entra Domain Services into your Remote Desktop deployment, your architecture will look something like this:
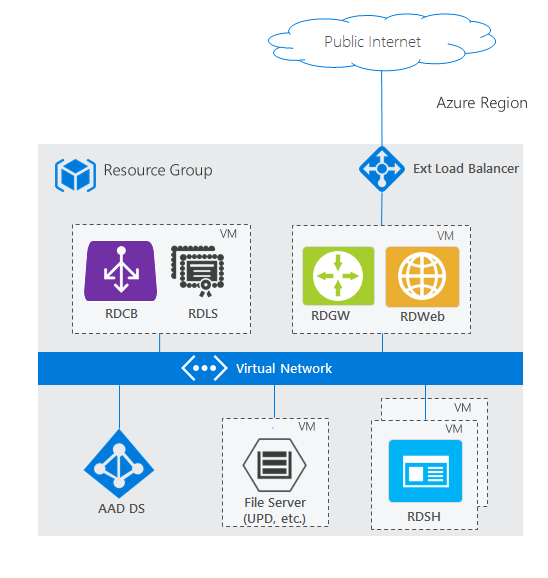
To see how this architecture compares with other RDS deployment scenarios, check out Remote Desktop Services architectures.
To get a better understanding of Microsoft Entra Domain Services, check out the Microsoft Entra Domain Services overview and How to decide if Microsoft Entra Domain Services is right for your use-case.
Use the following information to deploy Microsoft Entra Domain Services with RDS.
Before you can bring your identities from Microsoft Entra ID to use in an RDS deployment, configure Microsoft Entra ID to save the hashed passwords for your users' identities. Born-in-the-cloud organizations don't need to make any additional changes in their directory; however, on-premises organizations need to allow password hashes to be synchronized and stored in Microsoft Entra ID, which may not be permissible to some organizations. Users will have to reset their passwords after making this configuration change.
Use the following steps to deploy Microsoft Entra Domain Services and RDS.
Enable Microsoft Entra Domain Services. Note that the linked article does the following:
Set up RDS. You can either use an Azure template or deploy RDS manually.
Use the Existing AD template. Make sure to customize the following:
Settings
Resource group: Use the resource group where you want to create the RDS resources.
Note
Right now this has to be the same resource group where the Azure resource manager virtual network exists.
Dns Label Prefix: Enter the URL that you want users to use to access RD Web.
Ad Domain Name: Enter the full name of your Microsoft Entra instance, for example, "contoso.onmicrosoft.com" or "contoso.com".
Ad Vnet Name and Ad Subnet Name: Enter the same values that you used when you created the Azure resource manager virtual network. This is the subnet to which the RDS resources will connect.
Admin Username and Admin Password: Enter the credentials for an admin user that's a member of the AAD DC Administrators group in Microsoft Entra ID.
Template
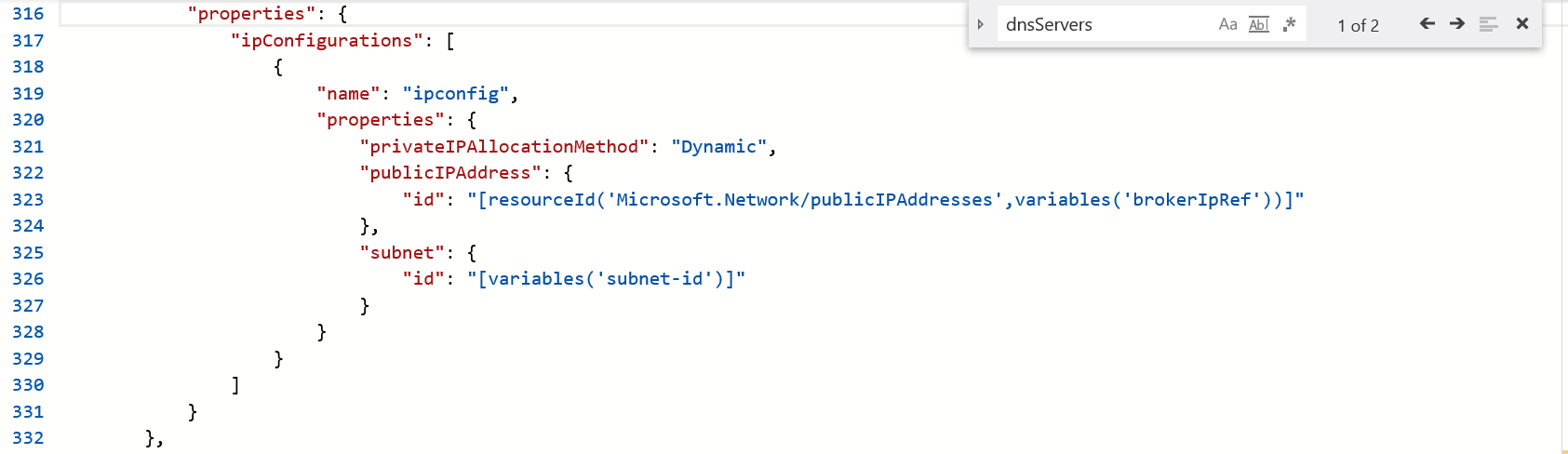
Remove all properties of dnsServers: after selecting Edit template from the Azure quickstart template page, search for "dnsServers" and remove the property.
For example, before removing the dnsServers property:

And here's the same file after removing the property:
Events
Apr 29, 2 PM - Apr 30, 7 PM
Join the ultimate Windows Server virtual event April 29-30 for deep-dive technical sessions and live Q&A with Microsoft engineers.
Sign up now