Events
Apr 9, 3 PM - Apr 10, 12 PM
Code the Future with AI and connect with Java peers and experts at JDConf 2025.
Register NowThis browser is no longer supported.
Upgrade to Microsoft Edge to take advantage of the latest features, security updates, and technical support.
In this article, you learn how to integrate Confluence SAML SSO by Microsoft with Microsoft Entra ID. When you integrate Confluence SAML SSO by Microsoft with Microsoft Entra ID, you can:
Use your Microsoft Entra account with Atlassian Confluence server to enable single sign-on. This way all your organization users can use the Microsoft Entra credentials to sign in into the Confluence application. This plugin uses SAML 2.0 for federation.
The scenario outlined in this article assumes that you already have the following prerequisites:
Note
To test the steps in this article, we don't recommend using a production environment of Confluence. Test the integration first in development or staging environment of the application and then use the production environment.
Note
This integration is also available to use from Microsoft Entra US Government Cloud environment. You can find this application in the Microsoft Entra US Government Cloud Application Gallery and configure it in the same way as you do from public cloud.
To get started, you need the following items:
Note
For the information on application proxy configuration for Confluence, please refer this article.
As of now, following versions of Confluence are supported:
Note
Please note that our Confluence Plugin also works on Ubuntu Version 16.04
In this article, you configure and test Microsoft Entra SSO in a test environment.
To configure the integration of Confluence SAML SSO by Microsoft into Microsoft Entra ID, you need to add Confluence SAML SSO by Microsoft from the gallery to your list of managed SaaS apps.
Alternatively, you can also use the Enterprise App Configuration Wizard. In this wizard, you can add an application to your tenant, add users/groups to the app, assign roles, and walk through the SSO configuration as well. Learn more about Microsoft 365 wizards.
Configure and test Microsoft Entra SSO with Confluence SAML SSO by Microsoft using a test user called B.Simon. For SSO to work, you need to establish a link relationship between a Microsoft Entra user and the related user in Confluence SAML SSO by Microsoft.
To configure and test Microsoft Entra SSO with Confluence SAML SSO by Microsoft, perform the following steps:
Follow these steps to enable Microsoft Entra SSO.
Sign in to the Microsoft Entra admin center as at least a Cloud Application Administrator.
Browse to Identity > Applications > Enterprise applications > Confluence SAML SSO by Microsoft > Single sign-on.
On the Select a single sign-on method page, select SAML.
On the Set up single sign-on with SAML page, select the pencil icon for Basic SAML Configuration to edit the settings.
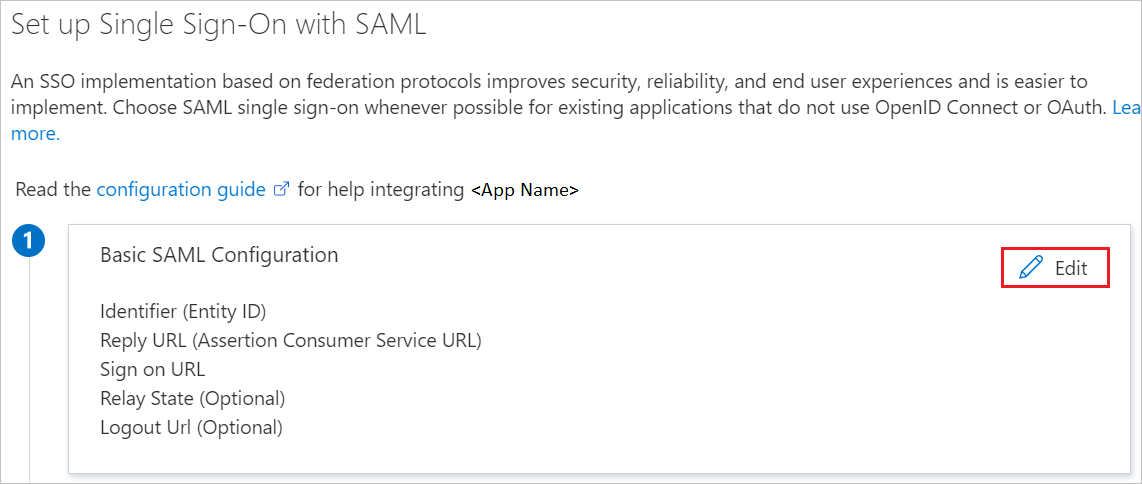
On the Basic SAML Configuration section, perform the following steps:
a. In the Identifier box, type a URL using the following pattern:
https://<DOMAIN:PORT>/
b. In the Reply URL text box, type a URL using the following pattern:
https://<DOMAIN:PORT>/plugins/servlet/saml/auth
c. In the Sign-on URL text box, type a URL using the following pattern:
https://<DOMAIN:PORT>/plugins/servlet/saml/auth
Note
These values aren't real. Update these values with the actual Identifier, Reply URL, and Sign-on URL. Port is optional in case it’s a named URL. These values are received during the configuration of Confluence plugin, which is explained later in the article.
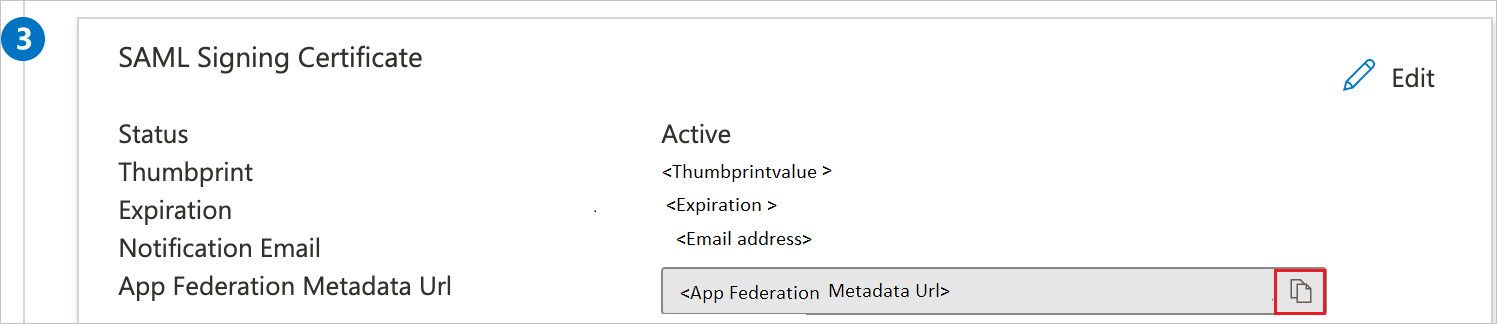
On the Set up single sign-on with SAML page, In the SAML Signing Certificate section, select copy button to copy App Federation Metadata Url and save it on your computer.
Follow the guidelines in the create and assign a user account quickstart to create a test user account called B.Simon.
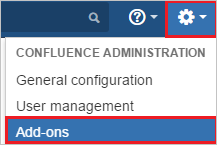
In a different web browser window, sign in to your Confluence instance as an administrator.
Hover on cog and select the Add-ons.
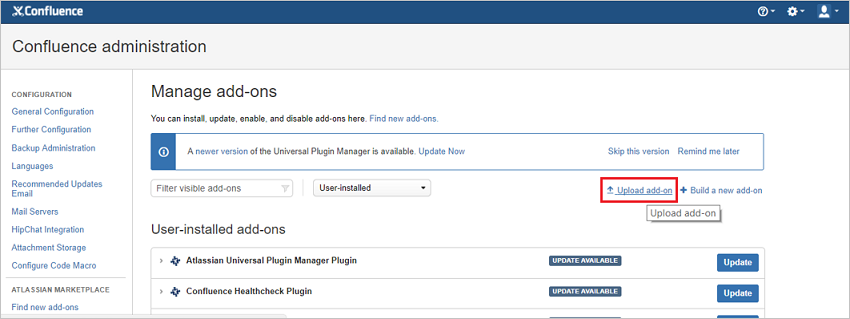
Download the plugin from Microsoft Download Center. Manually upload the plugin provided by Microsoft using Upload add-on menu. The download of plugin is covered under Microsoft Service Agreement.
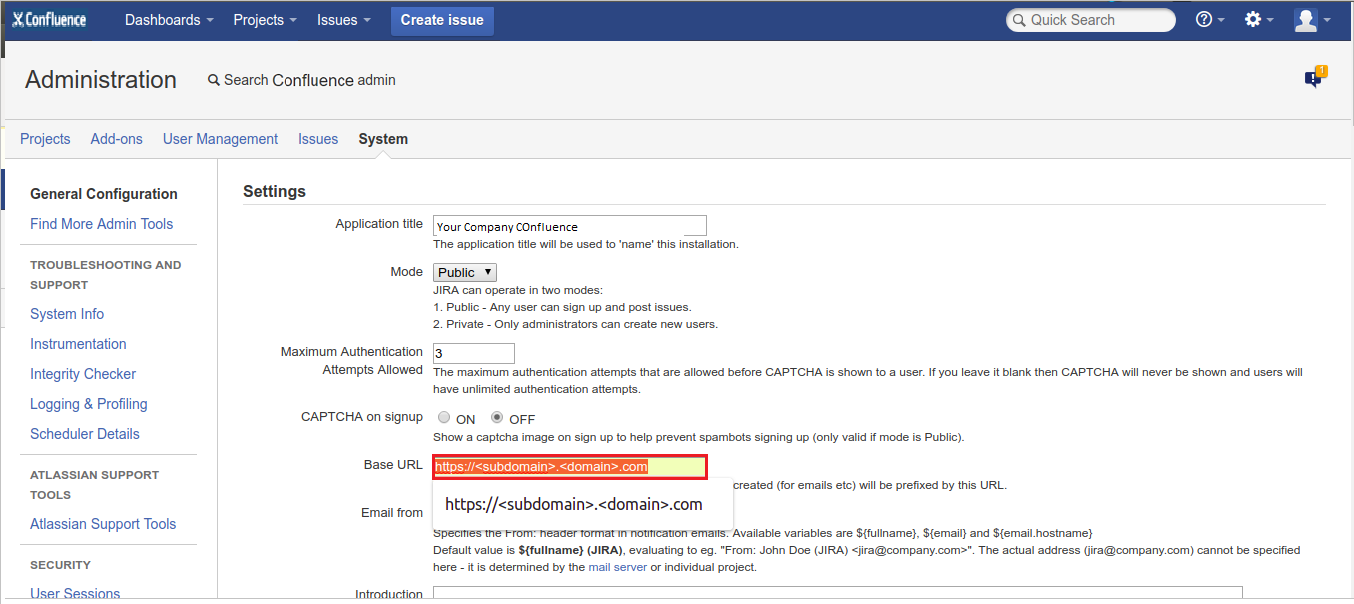
For running the Confluence reverse proxy scenario or load balancer scenario perform the following steps:
Note
You should be configuring the server first with the below instructions and then install the plugin.
a. Add below attribute in connector port in server.xml file of JIRA server application.
scheme="https" proxyName="<subdomain.domain.com>" proxyPort="<proxy_port>" secure="true"

b. Change Base URL in System Settings according to proxy/load balancer.
Once the plugin is installed, it appears in User Installed add-ons section of Manage Add-on section. Select Configure to configure the new plugin.
Perform following steps on configuration page:
Tip
Ensure that there is only one certificate mapped against the app so that there is no error in resolving the metadata. If there are multiple certificates, admin gets an error upon resolving the metadata.

In the Metadata URL textbox, paste App Federation Metadata Url value which you have copied and select the Resolve button. It reads the IdP metadata URL and populates all the fields information.
Copy the Identifier, Reply URL and Sign on URL values and paste them in Identifier, Reply URL and Sign on URL textboxes respectively in Basic SAML Configuration section.
In Login Button Name type the name of button your organization wants the users to see on login screen.
In Login Button Description type the description of button your organization wants the users to see on login screen.
In Default Group Select your organization Default Group to assign to new users (Default groups facilitate organized access rights to new user account).
In Auto-create User feature (JIT User Provisioning): It automates user account creation in authorized web applications, without the need for manual provisioning. This reduces administrative workload and increases productivity. Because JIT relies on the login response from Azure AD, enter the SAML-response attribute values, which include the user's email address, last name, and first name.
In SAML User ID Locations, select either User ID is in the NameIdentifier element of the Subject statement or User ID is in an Attribute element. This ID has to be the Confluence user ID. If the user ID isn't matched, then system doesn't allow users to sign in.
Note
Default SAML User ID location is Name Identifier. You can change this to an attribute option and enter the appropriate attribute name.
If you select User ID is in an Attribute element option, then in Attribute name textbox type the name of the attribute where User ID is expected.
If you're using the federated domain (like ADFS, and so on) with Microsoft Entra ID, then select the Enable Home Realm Discovery option and configure the Domain Name.
In Domain Name type the domain name here in case of the ADFS-based login.
Check Enable Single Sign out if you wish to sign out from Microsoft Entra ID when a user signs out from Confluence.
Enable Force Azure Login checkbox, if you wish to sign in through Microsoft Entra credentials only.
Note
To enable the default login form for admin login on the login page when the force azure login is enabled, add the query parameter in the browser URL.
https://<DOMAIN:PORT>/login.action?force_azure_login=false
Enable Use of Application Proxy checkbox, if you have configured your on-premise atlassian application in an application proxy setup. For App proxy setup , follow the steps on the Microsoft Entra application proxy Documentation.
Select Save button to save the settings.
Note
For more information about installation and troubleshooting, visit MS Confluence SSO Connector Admin Guide. There's also an FAQ for your assistance.
To enable Microsoft Entra users to sign in to Confluence on-premises server, they must be provisioned into Confluence SAML SSO by Microsoft. For Confluence SAML SSO by Microsoft, provisioning is a manual task.
To provision a user account, perform the following steps:
Sign in to your Confluence on-premises server as an administrator.
Hover on cog and select the User management.

Under Users section, select Add users tab. On the Add a User dialog page, perform the following steps:

a. In the Username textbox, type the email of user like B.Simon.
b. In the Full Name textbox, type the full name of user like B.Simon.
c. In the Email textbox, type the email address of user like B.Simon@contoso.com.
d. In the Password textbox, type the password for B.Simon.
e. Select Confirm Password reenter the password.
f. Select Add button.
In this section, you test your Microsoft Entra single sign-on configuration with following options.
Select Test this application, this option redirects to Confluence SAML SSO by Microsoft Sign-on URL where you can initiate the login flow.
Go to Confluence SAML SSO by Microsoft Sign-on URL directly and initiate the login flow from there.
You can use Microsoft My Apps. When you select the Confluence SAML SSO by Microsoft tile in the My Apps, this option redirects to Confluence SAML SSO by Microsoft Sign-on URL. For more information about the My Apps, see Introduction to the My Apps.
Once you configure Confluence SAML SSO by Microsoft you can enforce Session control, which protects exfiltration and infiltration of your organization’s sensitive data in real time. Session control extends from Conditional Access. Learn how to enforce session control with Microsoft Defender for Cloud Apps.
Events
Apr 9, 3 PM - Apr 10, 12 PM
Code the Future with AI and connect with Java peers and experts at JDConf 2025.
Register NowTraining
Module
Implement and monitor the integration of enterprise apps for SSO - Training
Deploying and monitoring enterprise applications to Azure solutions can ensure security. Explore how to deploy on-premises and cloud based apps to users.
Certification
Microsoft Certified: Identity and Access Administrator Associate - Certifications
Demonstrate the features of Microsoft Entra ID to modernize identity solutions, implement hybrid solutions, and implement identity governance.